Investigators Unable To Unlock iPhones of Suspect Involved In Pensacola Military Base Shooting
The United States is preparing to remove more than a dozen Saudi military students from a training program and return them to their home country after an investigation into a deadly shooting by a Saudi aviation student at a Florida navy base last month, a U.S. official told The Associated Press. Investigators Unable To Unlock iPhones of Suspect Involved In Pensacola Military Base Shooting
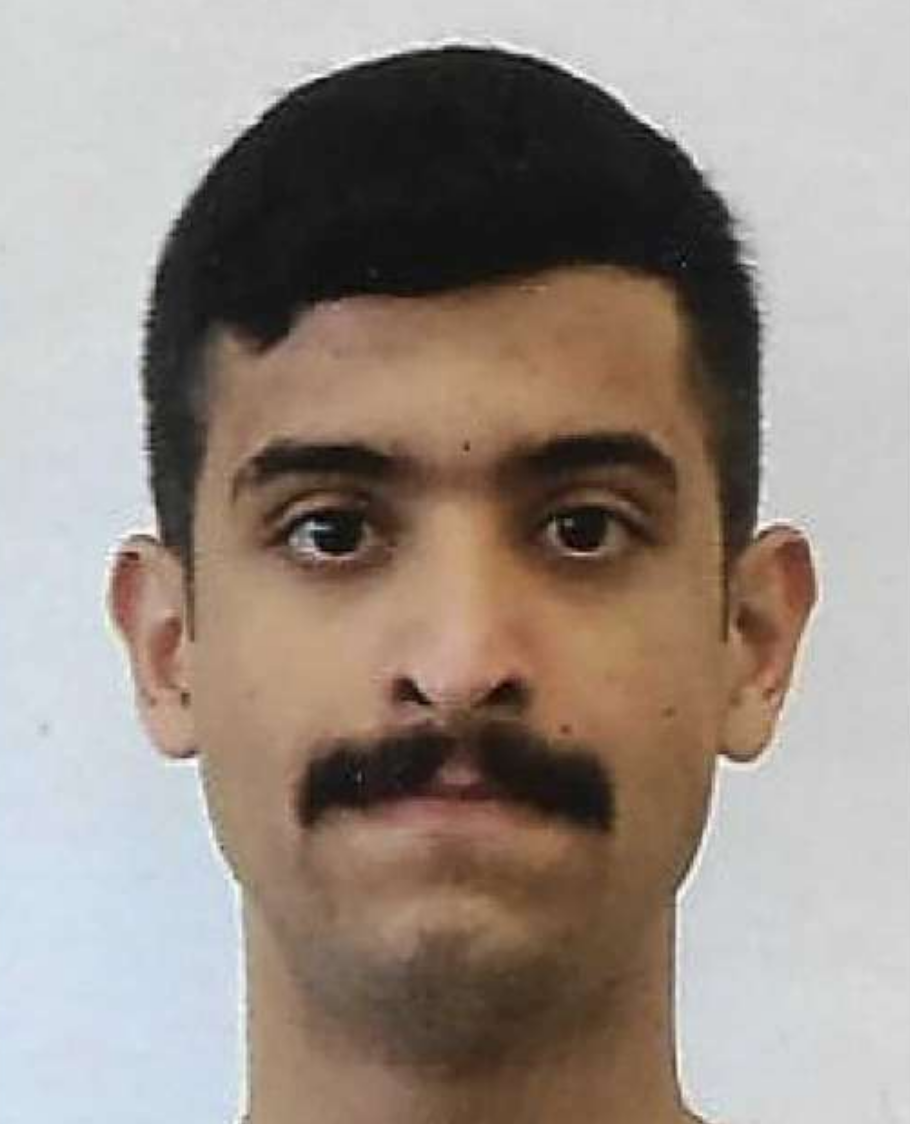
The 21-year-old Saudi Air Force officer, 2nd Lt. Mohammed Alshamrani, opened fire at the base in Pensacola, killing three U.S. sailors and injuring eight other people. The Justice Department has been investigating the incident as an act of terrorism.
Officials have said Alshamrani hosted a party before the shooting, where he and others watched videos of mass shootings. The gunman had also apparently taken to Twitter before the shooting to criticize U.S. support of Israel and accuse America of being anti-Muslim, another U.S. official told the AP last month.
Related:
Debate Over ‘Warrant-Proof’ Encryption Is Revived
Legal Constraints Hobble FBI’s Fight Against Domestic Terror
Alshamrani, who was killed by a sheriff’s deputy during the rampage at a classroom building, was undergoing flight training at Pensacola, where members of foreign militaries routinely receive instruction.
It was not immediately clear on what grounds the students were being removed from the program, though the official said they were not suspected of having played any role in the attack. The precise number of students being removed was also not clear. The officials discussing the case spoke on condition of anonymity to speak about details involved in an ongoing investigation.
The FBI declined to comment on Sunday. The Justice Department said Attorney General William Barr and Deputy FBI Director David Bowdich would provide an update on the investigation at a news conference Monday afternoon.
The plan to remove the students was first reported by CNN.
The December shooting raised questions about how well international military students are screened before they attend training at American bases. Some lawmakers, including a top Republican ally of President Donald Trump, have called for Saudi Arabia to be suspended from an American military training program.
Trump called for the program to be reviewed. But Sen. Lindsey Graham, R-S.C., said the program needed to be reevaluated after the attack.
A Saudi commanding officer had ordered all students from the country to remain at one location at the base after the attack.
National security adviser Robert O’Brien said in an interview on Fox News that the shooting “showed that there had been errors in the way that we vetted” the students. The actions being taken by the Justice Department and Defense Department to remove the Saudi students are to “protect our service men and women,” he said.
Federal officials are still investigating the shooting and examining evidence. Earlier this week, FBI asked Apple to help extract data from two iPhones that belonged to the gunman.
Investigators have been trying to access the two devices — an iPhone 7 and an iPhone 5 — but have been unable to access them because the phones are locked and encrypted, according to a letter from the FBI’s general counsel, Dana Boente. The FBI has received a court authorization to search the phones and the devices have been sent to the bureau’s lab in Quantico, Virginia, he said.
The investigation is considered a “high-priority national security matter,” Boente said in the letter.
FBI officials have sought help from other federal agencies and other experts, and investigators have been trying to guess the passwords, but those efforts have been unsuccessful, according to the letter.
Apple said in a statement that it has already provided investigators with all the relevant data held by the company and would continue to support the investigators.
Senior Justice Department and FBI officials told congressional staff on a phone briefing Monday morning that there was nothing Apple could do to unlock the iPhones in question, according to a congressional aide familiar with the call. But the officials criticized Apple for not having a method to do so, the aide said.
At least one of the phones was shot by a sheriff’s deputy during the attack, but investigators believe they may still be able to extract data from the device, according to a person familiar with the matter. The person spoke on condition of anonymity to discuss an ongoing investigation.
Updated: 1-13-2020
U.S. Calls Pensacola Attack Terrorism; Pressures Apple Over Gunman’s Locked Phones
Attorney general seeks more information about radicalization of Saudi student who killed three people at a naval base last month.
Attorney General William Barr called the December attack by a Saudi aviation student that killed three people at a Florida Navy base an act of terrorism, escalating pressure on Apple Inc. to help unlock a pair of the gunman’s iPhones that could provide more information about his radicalization.
Mr. Barr called on Apple to find a way to crack the encrypted phones in a high-profile request that ramped up a long-simmering fight between tech firms and the government over how to best balance digital security with the imperatives of criminal investigations.
Second Lt. Mohammed Alshamrani, a member of the Saudi air force who was training with the U.S. military, posted anti-U.S. messages on social media about two hours before he opened fire in a classroom at Naval Air Station Pensacola on Dec. 6, Mr. Barr said Monday. The gunfire lasted about 15 minutes before Lt. Alshamrani was killed by responding sheriff’s deputies.
During the attack, Lt. Alshamrani made statements critical of U.S. military actions overseas and fired shots at a picture of President Trump, officials said. In the weeks beforehand, the gunman used social media to blame the U.S. for crimes against Muslims, officials said, issuing a warning on the anniversary of the Sept. 11, 2001, attacks that “the countdown has started.”
Investigators have found no evidence that Lt. Alshamrani had co-conspirators in the U.S. or that he was inspired by one specific terrorist group, Federal Bureau of Investigation Deputy Director David Bowdich said. The FBI interviewed more than 500 of his friends, classmates and other associates, and analyzed more than 42 terabytes of digital information, he said.
But Justice Department officials said only a look at data and communications on the gunman’s phones could help them say for certain whether he discussed his plans with others.
Mr. Barr, stepping up a long-running fight between law-enforcement agencies and Silicon Valley over access to encrypted data, said: “This situation perfectly illustrates why it is critical that the public be able to get access to digital evidence.” He said that Apple had provided no “substantive assistance” getting into the two phones, which are locked with unknown pass codes and encrypted.
Apple, in a statement late Monday, said it always worked cooperatively with law enforcement to help in investigations and that it rejected Mr. Barr’s characterization that it hadn’t provided substantial assistance.
“Our responses to their many requests since the attack have been timely, thorough and are ongoing,” an Apple spokesman said. In response to several legal requests, the company quickly provided a “wide variety of information” when first contacted by law enforcement last month, “including iCloud backups, account information and transactional data for multiple accounts,” the spokesman said.
Only last week did the FBI notify Apple that more assistance was required and alerted the company of a second phone investigators couldn’t access, the spokesman said, adding that “early outreach is critical to accessing information and finding additional options.”
The Justice Department under Mr. Barr has increasingly highlighted the difficulties investigators face in accessing encrypted communications for suspects ranging from terrorists to child predators. Apple and other tech firms have said they help authorities wherever possible, but that creating vulnerabilities in their encrypted products would jeopardize broader internet security and make users less safe from cybercriminals.
“It’s very important for us to know with whom and about what the shooter was communicating before he died,” Mr. Barr said on Monday.
New details about the gunman’s views came as the U.S. said it was expelling 21 Saudi military students from a training program and immediately sending them back to Saudi Arabia. The probe found no evidence that the students helped plan the attack, but many of them had contact with child pornography and almost all of them possessed jihadist or anti-U.S. material, Mr. Barr said.
None of the students face federal charges, but all were expected to be returned to their home country by later Monday.
The attorney general’s public call came a week after the FBI’s general counsel sent a letter to Apple asking for assistance in accessing material on Lt. Alshamrani’s phones. Apple and other companies receive requests for help frequently from the FBI, but the use of a formal letter was seen as unusual.
Officials said investigators secured a court order within a day of the shooting but waited a month to contact Apple because they were trying to exhaust other options to attempt to get into the phones, which the gunman had damaged, firing a shot into one of them.
A Justice Department official said Monday that Apple hadn’t yet told the department whether company employees were able to get into the phones themselves. But senior Justice and FBI officials told congressional staff on a phone briefing Monday morning that there was nothing Apple could do to unlock the iPhones in question, according to two congressional aides familiar with the call. The officials criticized Apple for not having created a method for doing so, the aides said.
The news conference was Mr. Barr’s latest attempt to apply pressure on technology companies for widely adopting encryption standards that law-enforcement officials have long complained make it difficult for them to unlock digital data belonging to a criminal suspect, even with a warrant.
“We don’t want to get into a world where we have to spend months and even years exhausting efforts when lives are in the balance,” Mr. Barr said. “We should be able to get in when we have a warrant that establishes that criminal activity is under way.”
Mr. Barr’s comments could set the stage for a showdown like the one that took place during the final year of the Obama administration when the Justice Department tried to force Apple to create a software update that would break the privacy protections of the iPhone to gain access to a phone linked to a dead gunman responsible for a 2015 terrorist attack in San Bernardino, Calif.
Apple refused to comply, and the FBI found a third party that was able to unlock the device; the conflict was largely viewed as a publicity win for the iPhone maker.
The government suffered another setback in 2018, when the FBI disclosed it had accidentally inflated public statistics about the number of encrypted devices investigators were unable to break open. A new estimate has never been provided.
Because U.S. and Saudi officials missed signs of Lt. Alshamrani’s possible extremist views, the shooting drew attention to screening procedures and security concerns surrounding the more than 5,000 international military service members, including approximately 850 Saudis, who come to the U.S. each year for training. Military students who train in the U.S. are chosen by their home countries.
The Defense Department is expected to announce findings of a Pentagon review of its procedures as soon as this week. Among the conclusions, according to defense officials, is that U.S. officials now will examine the social-media history of training candidates as part of the review process.
Defense Secretary Mark Esper said Sunday that he already has ordered more stringent screening.
The shooting happened during a period of elevated tension between Washington and Riyadh, but Mr. Barr said the royal government had been cooperative in the investigation and assured him Saudi officials would review the students’ cases under their military justice and criminal code.
While Mr. Barr has repeatedly lamented the phone technology issue in speeches before, this was the first time he prominently linked it to an individual case. But Mr. Barr notably declined to say whether the Justice Department is considering seeking a court order to compel Apple to help authorities unlock the devices linked to the Pensacola shooter, which are an iPhone 7 and an iPhone 5. Former officials have said leadership at both the Justice Department and FBI appear reticent to descend into another drawn-out legal dispute.
Similarly, there has been little appetite in Congress to try to legislate the “Going Dark” issue in a manner that would force companies to build weaknesses into their products.
Just a few years ago, many iPhones were almost impossible to crack, but that is no longer true, security experts and forensic examiners say. Companies including Grayshift LLC, Israel’s Cellebrite Mobile Synchronization Ltd. and others offer methods to retrieve data from recent iPhones.
“We’ve got the tools to extract data from an iPhone 5 and 7 now,” said Andy Garrett, a chief executive of Garrett Discovery, a forensics investigation firm. “Everybody does.”
Four years ago, in the final year of the Obama administration, the Justice Department tried to force Apple to create a software update—a “backdoor”—that would allow law enforcement to gain access to a phone linked to a dead gunman responsible for a 2015 terrorist attack in San Bernardino, Calif.
Apple refused, and it continues to refuse to grant access via a software update, saying it could be exploited by others. The FBI turned to a third party, spending more than $1 million to obtain data from an encrypted Apple iPhone 5C.
Today, the bureau could likely obtain that data for $15,000 or less, thanks to new forensics tools it has purchased over the past two years that have made breaking into an iPhone much less daunting.
The changing security dynamics have undermined the Justice Department’s argument that Apple’s security is hampering investigations, forensics experts say.
“It’s a cat-and-mouse game. Apple locks things, but if someone wants to find a way to get into these devices, they will find a way,” said Sarah Edwards, a digital forensics instructor with the SANS Institute, an organization that trains cybersecurity investigators.
In 2018, Grayshift began selling an iPhone hacking device for as little as $15,000 to law enforcement customers in the U.S. The Grayshift device leveraged bugs in Apple’s products to access the phone. Today, Israel’s Cellebrite offers software that can also retrieve data from recent iPhones.
In the past two years, Grayshift has sold its products to the U.S. Bureau of Prisons, the Drug Enforcement Administration, the Internal Revenue Service and the FBI. The FBI has spent more than $1 million on Grayshift products, according to federal procurement records.
Georgia’s Gwinnett County, for example, started using the Grayshift device in 2018 and gained access to about 300 phones that year. Now, Chris Ford, an investigator with the district attorney’s office, is using the device to reopen cases that had gone cold due to phones that were previously unreadable.
His office is now producing about three times as much forensics data as it did before Grayshift, Mr. Ford said.
“It’s really opened the door for us in our investigation,” he said.
Grayshift representatives didn’t return messages seeking comment. Cellebrite representatives didn’t return messages seeking comment for this article.
Cellebrite has been able to gain access to data on the iPhone 5 since at least 2015, according to forensic investigators and an online training video. The other phone involved in the Pensacola shooting—an iPhone 7, according to people familiar with the investigation—is also more easily readable than it once was.
Forensic tools used to hack into iPhones have been enhanced recently, thanks to software called Checkm8 that exploits a vulnerability in Apple’s hardware. It allows forensics tools to download data, such as deleted files, that is often hidden from even the users of the iPhone, security professionals say.
A forensics tool built with Checkm8 works on all iPhone devices from the iPhone 5s to the iPhone X, and exploits a hardware bug that Apple is unable to patch, they say.
Investigators caution that there are many factors that can limit the data available to investigators on an iPhone, such as the version of the operating system, the complexity of the user’s passcode and the state of the iPhone itself.
If the phones were powered off when the FBI obtained them, then investigators would have to crack the iPhone’s passcode before they could obtain detailed data on the phone, said Ms. Edwards, the digital forensics instructor.
But cracking the passcode is something that both Cellebrite and Grayshift’s device are designed to do, forensics experts say. “It may just take a while to crack the passcode,” Ms. Edwards said.
Related Articles:
Majority Of Americans Stressed Over Being In A Mass Shooting – Trump To Blame?
As Global Order Crumbles, Risks Of Recession Grows (#GotBitcoin?)
U.S. Mortgage Debt Hits Record, Eclipsing 2008 Peak
U.S. Stocks & Treasuries Flash Recession/Depression #GotBitcoin?
Investors Ponder Negative Bond Yields In The U.S. (#GotBitcoin?)
Lower Mortgage Rates Aren’t Likely To Reverse Sagging Home Sales (#GotBitcoin?)
Financial Crisis Yields A Generation Of Renters (#GotBitcoin?)
Global Manufacturing Recession Weighs On US Economy (#GotBitcoin?)
Falling Real Yields (0.241% ) Signal Worry Over U.S. Economy (#GotBitcoin?)
Donald Trump’s WH Projects $1 Trillion Deficit For 2019 (#GotBitcoin?)
U.S. Home Sales Stumble, As Pricey West Coast Markets Suffer Declines (#DumpTrump)
Lower Rates Have A Downside For Bank’s Mortgage-Servicing Rights (#GotBitcoin?)
Central Banks Are In Sync On Need For Fresh Stimulus (#GotBitcoin?)
Weak Corporate Earnings Signal A Weak Economy (#GotBitcoin?)
Price of Gold, Indicator Of Inflation And Recession Surges (#GotBitcoin?)
Recession Set To Materialize In Approximately In (9) Months (#GotBitcoin?)
A Whiff Of U.S. Recession Is In The Air Again. Credit Trumponomics
Trump Calls On Fed To Cut Interest Rates, Resume Bond-Buying To Stimulate Growth (#GotBitcoin?)
Fake News: A Perfectly Good Retail Sales Report (#GotBitcoin?)
Anticipating A Recession, Trump Points Fingers At Fed Chairman Powell (#GotBitcoin?)
Affordable Housing Crisis Spreads Throughout World (#GotBitcoin?) (#GotBitcoin?)
Los Angeles And Other Cities Stash Money To Prepare For A Recession (#GotBitcoin?)
Recession Is Looming, or Not. Here’s How To Know (#GotBitcoin?)
How Will Bitcoin Behave During A Recession? (#GotBitcoin?)
Many U.S. Financial Officers Think a Recession Will Hit Next Year (#GotBitcoin?)
Definite Signs of An Imminent Recession (#GotBitcoin?)
What A Recession Could Mean for Women’s Unemployment (#GotBitcoin?)
Investors Run Out of Options As Bitcoin, Stocks, Bonds, Oil Cave To Recession Fears (#GotBitcoin?)
Goldman Is Looking To Reduce “Marcus” Lending Goal On Credit (Recession) Caution (#GotBitcoin?)

Leave a Reply
You must be logged in to post a comment.