First American Financial Leaks Hundreds of Millions of Title Insurance Records (#GotBitcoin?)
The Web site for Fortune 500 real estate title insurance giant First American Financial Corp. leaked hundreds of millions of documents related to mortgage deals going back to 2003, until notified this week by KrebsOnSecurity. The digitized records — including bank account numbers and statements, mortgage and tax records, Social Security numbers, wire transaction receipts, and drivers license images — were available without authentication to anyone with a Web browser. First American Financial Leaks Hundreds of Millions of Title Insurance Records (#GotBitcoin?)
Santa Ana, Calif.-based First American is a leading provider of title insurance and settlement services to the real estate and mortgage industries. It employs some 18,000 people and brought in more than $5.7 billion in 2018.
Earlier this week, KrebsOnSecurity was contacted by a real estate developer in Washington state who said he’d had little luck getting a response from the company about what he found, which was that a portion of its Web site (firstam.com) was leaking tens if not hundreds of millions of records. He said anyone who knew the URL for a valid document at the Web site could view other documents just by modifying a single digit in the link.
And this would potentially include anyone who’s ever been sent a document link via email by First American.
KrebsOnSecurity confirmed the real estate developer’s findings, which indicate that First American’s Web site exposed approximately 885 million files, the earliest dating back more than 16 years. No authentication was required to read the documents.
Many of the exposed files are records of wire transactions with bank account numbers and other information from home or property buyers and sellers. Ben Shoval, the developer who notified KrebsOnSecurity about the data exposure, said that’s because First American is one of the most widely-used companies for real estate title insurance and for closing real estate deals — where both parties to the sale meet in a room and sign stacks of legal documents.
“Closing agencies are supposed to be the only neutral party that doesn’t represent someone else’s interest, and you’re required to have title insurance if you have any kind of mortgage,” Shoval said.
You give them all kinds of private information and you expect that to stay private.
“The title insurance agency collects all kinds of documents from both the buyer and seller, including Social Security numbers, drivers licenses, account statements, and even internal corporate documents if you’re a small business. You give them all kinds of private information and you expect that to stay private.”
Shoval shared a document link he’d been given by First American from a recent transaction, which referenced a record number that was nine digits long and dated April 2019. Modifying the document number in his link by numbers in either direction yielded other peoples’ records before or after the same date and time, indicating the document numbers may have been issued sequentially.
The earliest document number available on the site – 000000075 — referenced a real estate transaction from 2003. From there, the dates on the documents get closer to real time with each forward increment in the record number.
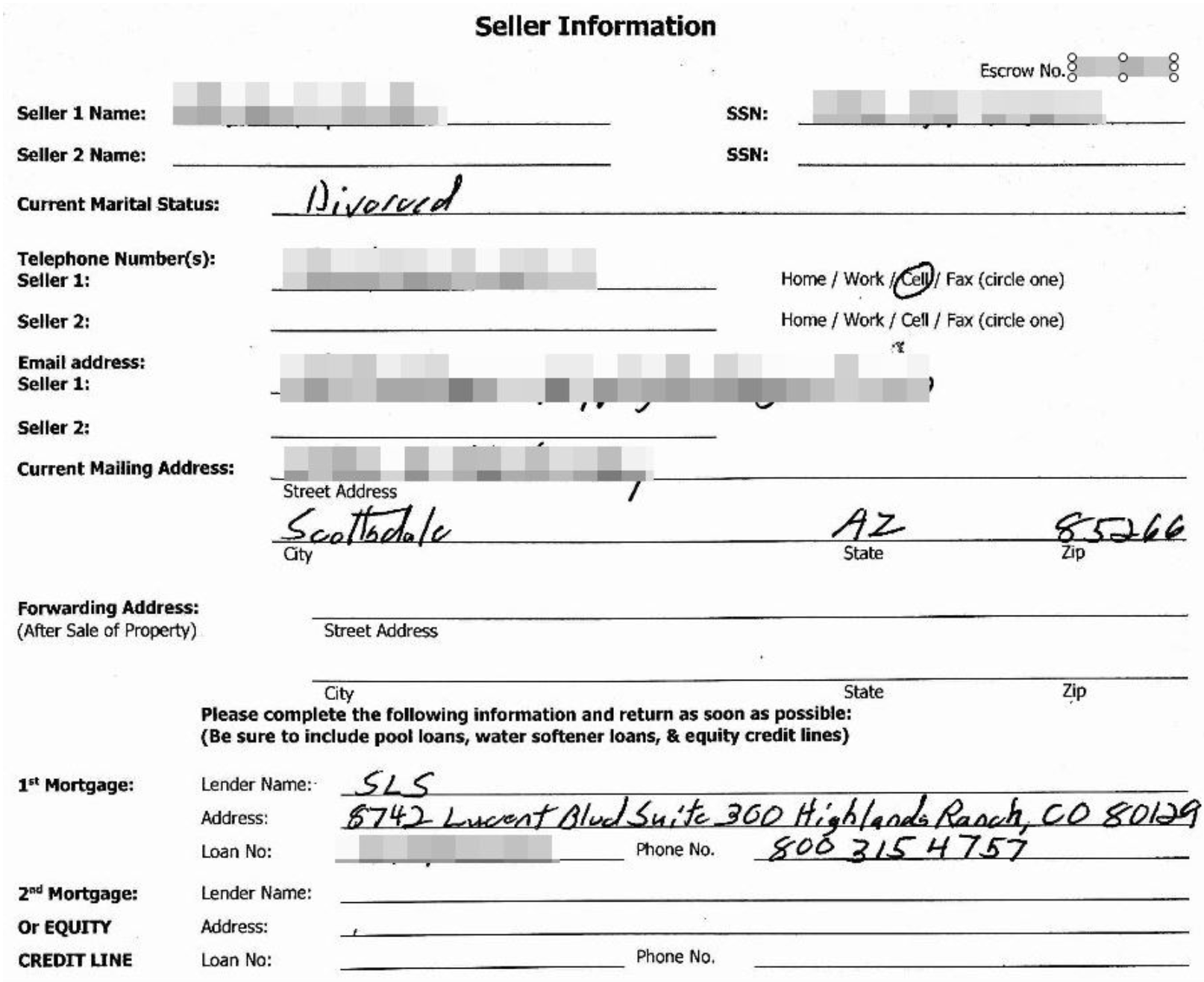
A Redacted Screenshot Of One Of Many Millions Of Sensitive Records Exposed By First American’s Web Site.
As of the morning of May 24, firstam.com was returning documents up to the present day (885,000,000+), including many PDFs and post-dated forms for upcoming real estate closings. By 2 p.m. ET Friday, the company had disabled the site that served the records. It’s not yet clear how long the site remained in its promiscuous state, but archive.org shows documents available from the site dating back to at least March 2017.
First American wouldn’t comment on the overall number of records potentially exposed via their site, or how long those records were publicly available. But a spokesperson for the company did share the following statement:
“First American has learned of a design defect in an application that made possible unauthorized access to customer data. At First American, security, privacy and confidentiality are of the highest priority and we are committed to protecting our customers’ information. The company took immediate action to address the situation and shut down external access to the application. We are currently evaluating what effect, if any, this had on the security of customer information. We will have no further comment until our internal review is completed.”
I should emphasize that these documents were merely available from First American’s Web site; I do not have any information on whether this fact was known to fraudsters previously, nor do I have any information to suggest the documents were somehow mass-harvested (although a low-and-slow or distributed indexing of this data would not have been difficult for even a novice attacker).
Nevertheless, the information exposed by First American would be a virtual gold mine for phishers and scammers involved in so-called Business Email Compromise (BEC) scams, which often impersonate real estate agents, closing agencies, title and escrow firms in a bid to trick property buyers into wiring funds to fraudsters. According to the FBI, BEC scams are the most costly form of cybercrime today.
Armed with a single link to a First American document, BEC scammers would have an endless supply of very convincing phishing templates to use. A database like this also would give fraudsters a constant feed of new information about upcoming real estate financial transactions — including the email addresses, names and phone numbers of the closing agents and buyers.
As noted in past stories here, these types of data exposures are some of the most common yet preventable. In December 2018, the parent company of Kay Jewelers and Jared Jewelers fixed a weakness in their site that exposed the order information for all of their online customers.
In August 2018, financial industry giant Fiserv Inc. fixed a bug reported by KrebsOnSecurity that exposed personal and financial details of countless customers across hundreds of bank Web sites.
In July 2018, identity theft protection service LifeLock corrected an information disclosure flaw that exposed the email address of millions of subscribers. And in April 2018, PaneraBread.com remedied a weakness exposing millions of customer names, email and physical addresses, birthdays and partial credit card numbers.
Meanwhile:
Cyberattack Hobbles Baltimore or Two Weeks And Counting
City faces second ransomware attack in 15 months; water bills, home sales face delays.
About 10,000 city government computers here remain frozen two weeks after a disruptive cyberattack that has delayed home sales and halted water bills.
Baltimore was hit May 7 by hackers demanding an undisclosed sum to unlock computers. The city hasn’t paid, and the Federal Bureau of Investigation is probing the incident. Mayor Bernard C. “Jack” Young has warned it could take months to recover some systems.
“It’s extremely alarming,” said City Council President Brandon Scott.
This is Baltimore’s second cyberattack in 15 months. In March last year, a short-lived ransomware attack on the city’s 911 system forced dispatchers to temporarily relay addresses and other information to first-responders by phone rather than electronically.
City officials emphasized that key services such as 911 emergency dispatch haven’t been affected by the current cyberattack.
Ransomware attacks are common in both the public and private sectors, and attackers are generally looking to exploit any vulnerability they can turn into extortion for money. After accessing systems through methods like malicious emails, hackers can encrypt files and then demand payment in bitcoin to unlock them.
Local governments are often more vulnerable than private companies, said Bill Siegel, chief executive at Coveware, a Connecticut-based firm that helps entities victimized by cyberattacks. “I think broadly they are not prepared for these sorts of things, they do not have the budget,” he said.
For Baltimore, “I think it’s pretty obvious that they have not been able to stay ahead of it,” said Mr. Siegel, who hasn’t worked with the city on this problem.
Frank Johnson, Baltimore’s chief information officer, didn’t respond to a request for comment Monday.
Mr. Scott said he will form a special committee to investigate the episode and city officials’ handling of it, “but most importantly, how they’re going to work to have this not happen in the future.”
While the city and outside contractors continued working Monday to restore the municipal computer system, officials began implementing a workaround to allow home sales to proceed.
Between 200 and 300 closings have been hung up because the city couldn’t tell title insurers whether the seller had any unpaid liens, said Alan Ingraham, chief executive of the Greater Baltimore Board of Realtors.
Starting Monday, sellers were able to sign an affidavit promising to pay any liens, such as unpaid water bills, that are discovered once the computers come back online. Mr. Young’s office said the city processed 42 applications for property deeds on the first day of the workaround.
Mark Glazer, executive director of the Maryland Land Title Association, a trade group for title insurers and agents, said this helps but he hopes the city resumes full operations quickly. May and June are busy months for deal closings, he said.
Meanwhile, the problems continue for some city agencies. Epidemiologists in Baltimore’s health department can’t access the state network that helps them warn the public when bad batches of street drugs trigger overdoses. And the city’s public-works department can’t generate new water bills for customers, which could mean residents will get unusually high bills once the problem is fixed.
“We can’t see the consumption data that our meters are collecting and sending to us,” said Jeff Raymond, a spokesman for the public-works department.
Greenville, N.C., was attacked last month by the same type of ransomware afflicting Baltimore, dubbed Robbinhood. The attackers demanded 13 bitcoins—worth roughly $69,000 at that point—to unlock the city’s files. The city didn’t pay, spokesman Brock Letchworth said in an email.
“While not 100% restored, all of our major technology needs are now being met,” he said.
Atlanta last year endured one of the highest-profile ransomware attacks on a major city. The city also refused to pay the ransom demand—$51,000 in that case—and has faced millions of dollars in costs to rebuild and bolster defenses.
In Baltimore, Mr. Scott said he pushed city officials to strengthen cyber defenses after last year’s 911 hack but that they “decided not to invest in this area.”
A spokesman for Mr. Young, who became mayor May 2 upon the resignation of Catherine Pugh, said Mr. Young has directed officials to obtain cybersecurity insurance, which would help offset the cost of any future hacks. First American Financial Leaks, First American Financial Leaks, First American Financial Leaks, First American Financial Leaks,First American Financial Leaks
Related Articles:
Ex-Intelligence Analyst Charged With Leaking Classified Information
Google To Launch New Privacy Tools To Limit Cookies
Alert! 540 Million Facebook Users’ Data Exposed On Amazon Servers (#GotBitcoin?)
Facebook Bug Potentially Exposed Unshared Photos of Up 6.8 Million Users (#GotBitcoin?)
Facebook Says Millions of Users’ Passwords Were Improperly Stored in Internal Systems (#GotBitcoin?)
Advertisers Allege Facebook Failed to Disclose Key Metric Error For More Than A Year (#GotBitcoin?)
Ad Agency CEO Calls On Marketers To Take Collective Stand Against Facebook (#GotBitcoin?)
Thieves Can Now Nab Your Data In A Few Minutes For A Few Bucks (#GotBitcoin?)
New Crypto Mining Malware Beapy Uses Leaked NSA Hacking Tools: Symantec Research (#GotBitcoin?)
Equifax, FICO Team Up To Sell Your Financial Data To Banks (#GotBitcoin?)
Cyber-Security Alert!: FEMA Leaked Data Of 2.3 Million Disaster Survivors (#GotBitcoin?)
DMV Hacked! Your Personal Records Are Now Being Transmitted To Croatia (#GotBitcoin?)
Lithuanian Man Pleads Guilty In $100 Million Fraud Against Google, Facebook (#GotBitcoin?)
Hack Alert! Buca Di Beppo, Owned By Earl Enterprises Suffers Data Breach Of 2M Cards (#GotBitcoin?)
SEC Hack Proves Bitcoin Has Better Data Security (#GotBitcoin?)


Leave a Reply
You must be logged in to post a comment.