Blockchain Will Be The Answer To Cybersecurity (#GotBitcoin?)
One of the most promising cybersecurity tools that exists today is something many people have heard about but few fully understand: blockchain technology. Blockchain Will Be The Answer To Cybersecurity
The technology has a lot going for it, but first it has to clear some major hurdles.
Commonly associated with bitcoin and other cryptocurrencies, blockchain has the potential to solve many cybersecurity problems and provide a built-in defense against cyberattacks. Before that can happen, however, it has to overcome some serious limitations.
But first, what is blockchain, exactly? Put simply, blockchain is a digital record of transactions that is stored on thousands or even millions of computers around the internet. Because blockchain’s distributed ledger network involves no centralized control over data, it can’t easily be tampered with, and once a record is posted, it can’t be changed.
To make sure only authorized users have access to the information, blockchain systems use cryptography-based digital signatures to verify identities. Users sign transactions with a “private key,” which is generated when a user creates an account. The private key, typically a very long and random alphanumeric code that is next to impossible for hackers to guess, is known only to the person who controls the account.
Using complicated algorithms, blockchain systems also create “public keys” from private keys to make it possible to share information. Public keys are known to the public. For instance, a bitcoin wallet address is a public key and others can send bitcoin payments to that address. However, only the person who has the private key can spend the bitcoin in the account.
Blockchain’s key features—decentralization, immutability and cryptography-based authentication—are what make it such a powerful cybersecurity tool. A user’s identity can’t be forged because only he or she has the private-key proof of identity. Third parties can be given limited access to records, while blockchain’s built-in audit trail means there is complete documentation of the creation, modification and deletion of records.
One of the problems blockchain has the potential to solve is the way identity and access management is handled online. Identity and access management involves making sure that information on computer networks about an individual or an asset is accurate—that I am who I say I am, or the file is really what it claims to be. It also describes the various actions users are authorized to perform or the information they are allowed to access.
Current identity-management techniques rely mainly on passwords, which are often exchanged and stored on insecure systems. The problems with passwords are well known: If they are too weak, they can be compromised; if they are strong, they can be hard to remember. We also have too many of them, stored in too many different places.
Weak passwords pose a particular problem for the rapidly growing Internet of Things, where connected devices come shipped with simple default passwords that people either don’t—or can’t—change. With IoT security a growing concern, a group of technology and financial companies—including Cisco Systems Inc., appliance maker Bosch, Bank of New York Mellon , cybersecurity company Gemalto and three blockchain startups—last year began working together to create a blockchain-based IoT security standard. They developed a protocol that allows users to bind together multiple kinds of weaker identities—such as serial numbers, QR codes and UPCs—into stronger cryptographic identities.
The widespread use of blockchain would allow device makers to securely distribute updates and patches, even if a device changes ownership (since all that information is stored in the blockchain). Because each device has a cryptographically protected identity, manufacturers can be sure they’re communicating with the right device.
Personal Data
Improving the safety of personal data online is another area where blockchain shows promise. Today, third parties such as health-care providers and financial institutions collect and store personal information, and consumers have little control over who can access it or with whom it is shared.
Existing data governance in the health-care sector, for example, lacks audit trails, so there is no guarantee of data integrity. There have been instances of employees stealing patients’ personal data and misusing it, and it is difficult or impossible to pinpoint the violator in a breach. While patients today have to consent to how their medical information is shared, they are often ill-informed about their rights, and many organizations are unable to record and implement patients’ instructions.
With blockchain, a patient’s entire medical record is stored in a ledger and encrypted with the patient’s private key. Changes in the patient’s condition are communicated to the ledger with the patient’s authorization and securely shared with various providers.
The ledger includes an audit trail and data are time-stamped, allowing the patient to know who made what changes and when. Health-care providers can see the patient’s data with his or her permission, but they can’t store it.
Another weakness associated with centralized identity-management systems is data manipulation, and here again, blockchain could provide an answer. One example that has received attention from the blockchain world is the problem developing countries have with land-title fraud, where corrupt officials alter property records to benefit themselves or in exchange for bribes.
With blockchain, when a property changes ownership, the technology can register time, location, price, parties involved and other relevant information. Government agencies, law firms and accounting firms can authenticate the title information as it is entered, and government agencies, courts and law-enforcement agencies can inspect documents to enforce compliance with know-your-customer and anti-money-laundering policies. Blockchain also prevents illegitimate access to data, and the owner retains ultimate control.
Hurdles To Be Cleared
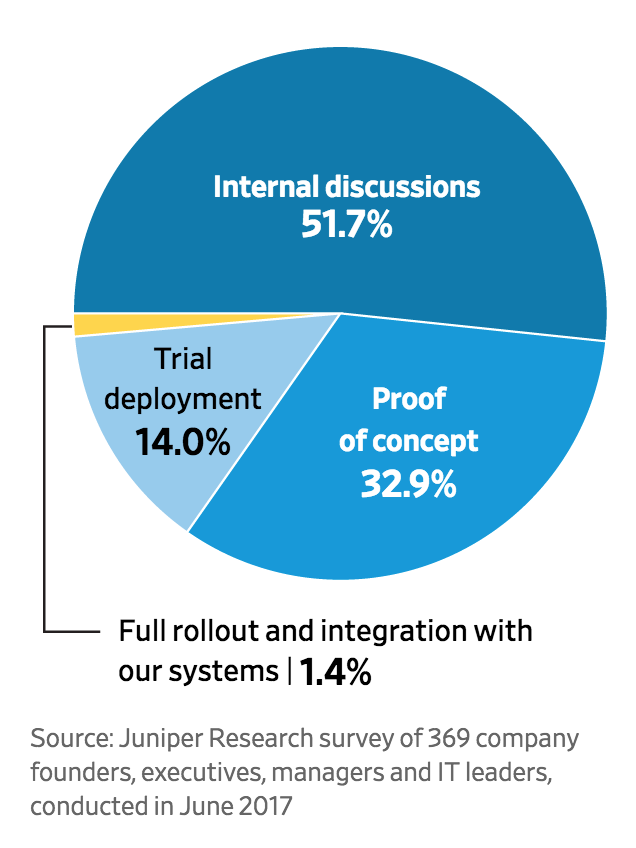
Still, before blockchain can be deployed widely as a cybersecurity tool, several challenges need to be addressed.
One concern is that most blockchain networks run the same code, so if a hacker finds a vulnerability, the entire system could be at risk. (To be sure, few “mission-critical bugs” have been found so far.)
Ensuring that data is accurate when it is entered into the blockchain ledger also presents a challenge. This can be especially problematic in the case of land registries in developing countries, where it can be difficult, even absent corruption, to determine the legitimate owner of a piece of land in the first place.
Companies that make cheap IoT devices, meanwhile, operate on small profit margins and have little incentive to incorporate blockchain in their devices. Most IoT devices also have low memory and processing power, and even lightweight blockchain technologies may require more than most IoT devices can handle.
To overcome these limitations, blockchain innovators need to increase research efforts to make it feasible to connect billions of IoT devices, while technology companies need to develop user-friendly security applications. Pressure from regulators and consumers is critical. If it is clear that their products won’t sell unless they’re more secure, small manufacturers will step up.
When it comes to land titles and others assets, blockchain projects are more likely to succeed if the governments or others who implement the system are seen as fair and impartial and the process itself is transparent and participatory.
Finally, key decision makers need to have a clearer understanding of the benefits of blockchain in cybersecurity—and communicate them to consumers and organizations.
Related Articles:
Annual January 3rd “Proof Of Keys” Celebration Of The Genesis Block! (#GotBitcoin?)
ETFs, Mutual Funds See Sudden And Dramatic Drop In Money Flowing In (#GotBitcoin?)
Trump Administration’s ‘Plunge Protection Team’ Convened Amid Wall Street Rout (#GotBitcoin?)
Crypto Craze Drew Them In; Fraud, In Many Cases, Emptied Their Pockets (#GotBitcoin?)
Meet The Watchdog Called CryptoMom (#GotBitcoin?)
Bitcoin On Facebook, Lite.IM Adds BTC Support For Leading Social Networks (#GotBitcoin?)
Your questions and comments are greatly appreciated.
Monty H. & Carolyn A.
Go back
Leave a Reply
You must be logged in to post a comment.