Ultimate Resource For Bitcoin’s Privacy And Scalability Upgrades (#GotBitcoin)
Bitcoin’s consensus layer has remained unchanged for over two years now. Since Segregated Witness (SegWit), which activated in August 2017, no hard fork or soft fork protocol upgrades have been deployed at all*, marking Bitcoin’s longest stretch without consensus forks so far. Ultimate Resource For Bitcoin’s Privacy And Scalability Upgrades (#GotBitcoin)
These could be Bitcoin’s protocol upgrades in the new year … or perhaps in the new decennium.
Schnorr/Taproot/Tapscript
Schnorr signatures are considered by many cryptographers to be the best type of cryptographic signatures in the field. They offer a strong level of correctness, do not suffer from malleability, are relatively fast to verify and, perhaps most interestingly, allow for math to be performed with them. To name one concrete benefit for Bitcoin: Several signatures can be aggregated into a single signature, which could, for example, economically incentivize privacy-enhancing CoinJoin transactions.
Related:
The Investor’s Perspective On The Bitcoin Taproot Upgrade
Privacy And Scale – Everything You Need To Know About Bitcoin’s Taproot (SOB#455)
Adding Schnorr signatures to the Bitcoin protocol has been a work in progress for some time now. But over the past year, developers working on a Schnorr signatures proposal, like Blockstream developers Pieter Wuille and Jonas Nick and Xapo’s Anthony Towns, revealed even more ambitious plans. Schnorr signatures will be proposed as part of a bigger soft fork protocol upgrade called Taproot, a proposal by Bitcoin Core contributor Gregory Maxwell, which was itself inspired by an older proposal called MAST (Merkelized Abstract Syntax Tree).
(Fractions of) bitcoin can be locked up in such a way that they can be spent under several different conditions, for example requiring timelocks, secret numbers of several participants to agree to unlock the coins. With MAST, all the different conditions are hashed and included in a Merkle Tree: a compact cryptographic data structure. The coins would then essentially be locked up in the final hash of this Merkle Tree, the Merkle Root. To spend the coins, you only need to reveal the condition you end up using. The alternative ways in which the coins could have been unlocked remain hidden forever.
Taproot, then, is based on an interesting realization: No matter how complex, almost any MAST-construction could (or should) include a condition that allows all participants to agree on the outcome and sign off on a settlement transaction together. This “cooperative close” would override all other conditions.
Taproot leverages this realization and utilizes Schnorr signatures to make the cooperative close look like a regular transaction. Simplified, the cooperative close would be done with an aggregated signature, which looks just like a regular signature. In doing so, the MAST-construction remains completely hidden to the outside world! This benefits privacy and efficiency.
Taproot may also come with an updated version of Bitcoin’s programming language, Script, called Tapscript. This would also make it easier to add new features (“OP codes”) to Bitcoin’s programming language later on.
Updated: 1-31-2020
Bitcoin’s Taproot Upgrade Won’t Help Privacy Where It Matters
The activation of Bitcoin’s (BTC) Taproot upgrade is moving forward as official Bitcoin Improvement Proposals (BIP) were submitted for review on Jan. 24. Even though Taproot is often hyped up for its privacy improvements, its true impact is likely to be very minor.
What Is Taproot?
Taproot is the name given to a proposal coined by former Blockstream CTO Gregory Maxwell in January 2018. The actual implementation was later developed by a team of Bitcoin contributors led by Pieter Wuille. Taproot is a proposal that enhances Bitcoin’s scripts, a set of instructions attached to each transaction that explains how the funds can be used.
In its simplest form, a Bitcoin transaction is secured by the recipient’s public key, which guarantees that only he can spend them. Scripts can support more complicated features, like timelocks and multi-signature requirements. The former can restrict money to only be spent after a certain point in time. The latter makes it possible to create wallets with multiple owners.
The conditions can be added together, so that there would be multiple options on how to spend the money. For example, the script might say that the funds can be moved immediately if three people agree, or after five days if only two of them do.
In Bitcoin’s current implementation, the full scope of the smart contract needs to be revealed when its beneficiary wants to use the money. That means that if only one of the conditions was triggered, everyone would know that there were others.
Taproot removes the need to publish the entire script, and only shows the condition that was triggered. In addition, multi-signature contracts where all parties agreed on a transaction can avoid revealing the fact that there was a script at all. To an external observer it would look like an individual wallet-to-wallet transaction, assuming the parties involved are in full cooperation.
This is made possible by a different feature called Schnorr signatures, which is encoded in BIP 340. Schnorr is considered a more secure and efficient version of elliptic curve cryptography, which is what underpins the system driving private and public keys.
The proposal is currently under evaluation, but there are no estimates available for its activation.
Limited Benefits To Privacy
Bitcoin is a fully public ledger, which allows specialized tools to track the flow of BTC from one wallet to the next. Thus, a protocol named CoinJoin (CJ) was developed to help break the chain of transactions and provide anonymity.
As it uses a peculiar transaction scheme, it is easy to prove that a certain wallet mixed Bitcoin through CoinJoin. This has recently started to create problems for users.
As previously reported by Cointelegraph in December, a Binance user was put under investigation for his history of mixing the coins he withdrew from the exchange. A similar case involving Paxos was recently reported by a Twitter user.
Taproot is often mistakenly believed to make CoinJoin transactions harder to see, or even make them indistinguishable from normal payments. In a conversation with Cointelegraph, Pieter Wuille revealed that this is not the case:
“Indeed, it [Taproot] hides scripts and makes multisig (often) indistinguishable. It does not directly do anything for CoinJoin.”
Wuille then added that Taproot is “certainly no silver bullet” for privacy.
The confusion may have arisen due to an initially planned feature called cross-input aggregation. It was later removed from the Taproot proposal due to potential issues from its implementation. Furthermore, Wuille clarified that it would not directly improve privacy:
“Cross-input aggregation won’t hide CJ or anything else. It’s not a privacy improvement, only an efficiency one (which may indirectly encourage CJ by making it cheaper, but even then, it won’t reduce the ability to recognize such transactions as CJ).”
Thus, Taproot only improves privacy in limited aspects and under specific conditions. For a person using Bitcoin to buy drugs from a darknet market, there is no benefit.
Updated: 2-3-2020
Privacy On Ethereum: Aztec Protocol Launches On Mainnet
The Aztec privacy network has officially launched on the Ethereum blockchain on Feb. 1. Using Zcash-based technology, it introduces confidential tokens where all amounts are cryptographically hidden.
The network is currently in limited deployment as it only supports zkDai, a private version of Maker’s stablecoin. Other zero knowledge tokens are set to be released in the coming weeks, while full access to custom token creation will be granted in two months, the company says.
The Aztec protocol, just like Zcash (ZEC), uses Zk-SNARKs to validate encrypted transactions. When generating a transfer, a proof of correctness is generated as the amount gets encrypted.
The system hinges on Aztec’s Cryptography Engine smart contract, which can be used to validate the transactions. The contract is based on a system of “notes,” which are generally used in a Bitcoin-like structure of inputs and outputs. Unlike Zcash, however, Aztec currently does not hide the money’s sender and recipient.
Like Zcash, Aztec needed to conduct a trusted setup ceremony. This is a key requirement for all zk-SNARK implementations, as it generates a set of common parameters to ensure efficient computation.
Future Developments Would Make Smart Contracts Private
Aztec’s goal is to deliver its “Triptych of privacy,” which would completely hide a particular portion of the Ethereum blockchain. The next step is to hide senders and recipients, while the final achievement is making smart contracts completely private.
Aztec’s CEO Thomas Walton-Pocock revealed to Cointelegraph that this may occur as early as this year:
“Our priority is to deploy PLONK to ACE in 2020. PLONK is the superfast Universal SNARK developed by AZTEC CTO Zac Williamson and AZTEC Chief Scientist Ariel Gabizon, which will eventually allow private smart contracts to execute with just one trusted setup.”
Updated: 2-16-2020
Authorities Arrest Ohio Man For Laundering $300M In Crypto On The Dark Web (A Good Case For Built-in Bitcoin Privacy)
Authorities recently took an Ohio local into custody recently for accusations of running an unlawful money laundering outfit on the Dark Web.
The alleged operator of an illegal business called Helix, Larry Harmon faces accusations of money laundering and running a money transference venture without proper licensing, the Department of Justice, or DoJ, detailed on Feb. 13.
Harmon Ran Helix For Years
The 36-year old Ohio native reportedly started up Helix in 2014, taking the endeavor all the way to crypto’s hay day in 2017.
The DoJ explained:
“Helix functioned as a bitcoin ‘mixer’ or ‘tumbler,’ allowing customers, for a fee, to send bitcoin to designated recipients in a manner that was designed to conceal the source or owner of the bitcoin.”
Per the allegations, Harmon attracted users by touting the ability to hide fund transfers from the government’s watchful eye. As part of his dealings, Harmon also operated a Dark Web search tool called Grams.
The Ohio Man Was In Deep
Harmon’s supposed endeavors naturally tied him to other Dark Web illegalities. “Helix allegedly laundered hundreds of millions of dollars of illicit narcotics proceeds and other criminal profits for Darknet users around the globe,” Assistant Attorney General for the DoJ’s Criminal Division Brian Benczkowski said in the statement.
IRS Criminal Investigation Head Don Fort Added:
“The sole purpose of Harmon’s operation was to conceal criminal transactions from law enforcement on the Darknet, and because of our growing expertise in this area, he could not make good on that promise. Working in tandem with other sites, he sought to be the ‘go-to’ money launderer on the Darknet, but our investigators once again played the role of criminal disrupters, unraveling the interlinked web from one tentacle to another.”
Charges include that Harmon’s Helix outfit transferred more than 350,000 Bitcoin — worth upward of $300 million at the time. The illegal entity also powered money laundering activities for users of AlphaBay, a highly trafficked Dark Web vendor, the DoJ detailed.
The DoJ pointed out, however, that the charges provided are still considered alleged activities until definitive guilt is proven.
Updated: 4-22-2020
Privacy Altcoin Beam To Execute Second Hard Fork In June 2020
After successfully completing its first hard fork in August 2019, privacy coin Beam plans to execute its second hard fork in June 2020.
Privacy-focused altcoin, Beam (BEAM), will soon execute its second hard fork. This fork will upgrade its Proof-of-Work (PoW) algorithm and activate new network features.
According to an April 22 blog post, Beam’s second fork will occur at block 777,777, shifting the network’s PoW algorithm from BeamHash II to BeamHash III.
The new PoW algorithm is expected to be a major improvement to the Beam mining network, and will enable fuller GPU card capabilities. Additionally, the firm said that the hard fork is designed to unlock some new features like confidential assets, one-sided payments, and the support of privacy protocol, Lelantus Mimblewimble.
Users Need To Upgrade Beam Software Before The Fork In Late June
Beam’s second hard fork is expected to take place on June 28, 2020. The testnet fork is anticipated to happen a few weeks earlier, Beam advisor, Guy Corem, noted in the Beam Telegram channel. Corem elaborated that the testnet fork date depends on block times.
According to the announcement, the hard fork will not require any other actions beyond a software upgrade from Beam users. As such, Beam is planning to release the node and desktop wallet binaries by the end of May, providing users with about 30 days to upgrade to the latest version. Compatible releases of node, wallet, and miner will be versioned Eager Electron 5.0, Beam noted.
Specifically, Beam wallets earlier than version 5.0 will stop working after the hard fork is completed. However, users will still be able to upgrade the wallets to the new version to access their funds, Corem said.
Beam’s First Hard Fork Took Place In August 2019
As officially announced, Beam successfully completed its first hard fork on August 19, 2019. This fork changed the mining algorithm from Beam Hash I to Beam Hash II at block 321,321. After the hard fork occurred, the Beam team reported a significant drop in mining difficulty. This was caused by some miners not performing a timely upgrade.
The Beam mainnet was launched on Bitcoin’s (BTC) tenth birthday, Jan. 3, 2019. Beam is a privacy-oriented cryptocurrency, like Monero (XMR) or Zcash (ZEC), and is based on a privacy protocol known as Mimblewimble. As reported in late 2019, Dragonfly Research analyst, Ivan Bogatyy, believes that the Mimblewimble protocol should not be considered a “viable alternative to Zcash or Monero when it comes to privacy” due to an unfixable privacy breach.
In March, Litecoin (LTC) and Grin (GRIN) developer, David Burkett, predicted that Litecoin will launch its Mimblewimble testnet before the end of summer.
Updated: 5-4-2020
Zcash Fully Shielded Transactions Jump 70% To New Record In April
The Zcash network has recorded a 70% jump in fully shielded transactions, marking a new record for April of over 8,700. This compounds gains of 100% made in March.
The number of fully shielded transactions recorded on the Zcash (ZEC) network leaped up almost 70% in April to hit a new record of over 8,700.
According to a May 1 tweet from the ZcashCommunity account, this represented 6% of the total transactions, which was also a record proportion historically.
April’s gains followed an equally impressive March, which itself saw a 100% increase in transactions over February. In total, the jump from February’s 2,430 fully private transactions to the 8,721 in April represents an increase of over 250%.
In contrast, it took three years for fully shielded transactions to break through the 2,000 per-month level, which only happened in November last year.
15% of Zcash Transactions Had Some Element Of Shielding
While 6% of the total transactions may not seem like an awful lot, this only includes those which were fully shielded. When considering all transactions with some shielded component, this goes up to 23,676, or 15% of the total.
Zcash supports two types of address: z-addr, which are shielded, and t-addr, which are transparent. Transactions between t-addr types are fully transparent, and can be viewed on the blockchain in the same way as Bitcoin (BTC) transactions.
Transactions between two z-addresses are fully shielded, and transactions between the two address types can be either shielding (t to z) or deshielding (z to t). It is worth noting that all of these three transaction types with a shielded component add to the privacy of the network.
Why Such A Big Increase Now?
Cointelegraph reached out to Zcash developer Electric Coin Company to see if it had any insight into the latest jump in figures, but had not received a response at press time.
However, it has recently become a lot easier for Zcash users to use shielded transactions. In early April, Guarda released its wallet app for Shielded ZEC. This now joins Zecwallet Lite, which was launched last November, and defaults to sending private transactions by shielding any transparent ZEC sent to it.
Zcash was also added as a perpetual contract option on Binance’s futures platform in February. This coincides with the point at which shielded transaction numbers started to go up dramatically.
Updated: 5-4-2020
Litecoin Mimblewimble Integration Sees Test Build And Codebase Progress
Litecoin and Grin++ developer, David Burkett, has posted an April progress update on Litecoin’s Mimblewimble integration, claiming that a testing framework has been built and codebase integration has started.
The lead developer on the Litecoin Mimblewimble (MW) project, David Burkett, has now built a functional testing framework and started to integrate the development work done so far into the Litecoin codebase.
According to a May 1 report on the Litecointalk forums, the project to implement the MW privacy enhancements into Litecoin has reached an important milestone with the build of a test-bed. Burkett claims that he has also run some end-to-end validation tests through the framework.
“I’ve built out a functional testing framework that builds valid headers, blocks, and transactions. I’ve now got some (mostly) complete end-to-end block validation tests,” he said.
As Cointelegraph reported in March, Burkett predicted that MW would be running on the Litecoin testnet by the end of the summer. This is a significant step towards that goal.
Codebase Integration
Burkett has also begun to integrate his work with the Litecoin codebase, initially focusing on the ConnectBlock logic. This part of the code validates blocks before adding them to the chain.
While Burkett was still unsure as to which specific area to tackle next, he did state that his high-level plan involved continued codebase integration and “lots more testing.”
Burkett also gave an update on his other project, Grin++, which has just achieved release candidate v1.0.0 status, marking its “first non-beta version.” Grin++ featured the first implementation of the Mimblewimble privacy protocol, back in January 2019.
Mimblewimble was first revealed in 2016 when its white paper — authored by an individual acting under the pen name Tom Elvis Jedusor — appeared on a Bitcoin research channel.
The protocol aims to improve blockchain privacy, scalability, and fungibility by combining transactions in a CoinJoin. As a result, blocks on the network comprise a list of all input, output, and signature data, which obscure transaction data for any third party monitoring the network.
Taproot doesn’t appear to be very contentious, though developers are still discussing implementation details.
Updated: 5-19-2020
18 Months In, Few People Use, Mine or Buy Privacy Coin Grin
Despite launching with considerable fanfare in early 2019, grin, the first cryptocurrency to test privacy protocol MimbleWimble, is showing no signs of life.
At its launch, professional investors poured funding — by some estimates, $100 million — into mining the cryptocurrency, with some even calling it a sort of “Bitcoin 2.0”.
Privacy without sacrificing scalability is the primary advantage of MimbleWimble, according to grin developers. The first grin coins were also issued via a so-called “fair launch” whereby, similar to bitcoin, all coins are minted by miners instead of being generated prior to the network going live.
“Grin was probably the most crowded venture capital trade of 2019,” said Ryan Gentry, lead analyst at Multicoin Capital.
On-chain data suggests once-eager investors soured on the young cryptocurrency. Grin’s hash power, a measure of computing resources devoted to securing the network, and mining difficulty, which gauges the amount of power required to mine, started to collapse in August 2019. After nine consecutive months of decline, the trend shows no sign of reversing.
Grin’s planned hard forks, or systemwide upgrades, could also be responsible for its declining network activity. Every six months, the network executes these upgrades that change grin’s mining algorithm to deter expensive, specialized mining equipment from dominating its hash power.
After the first fork, grin’s hashrate and difficulty climbed, but the second fork coincided with the steepest hashrate decline in the network’s short history. Grin is preparing for yet another drop in hashrate after a third next fork scheduled for July.
Even grin’s transaction count, a metric that could be easily manipulated to mask the network’s declining use, has dropped roughly 20% year to date, according to Coin Metrics. This smaller drop follows a more than 70% decrease in daily transactions through February and March 2019.
Grin developers say the cryptocurrency isn’t designed to cater to short-term speculative investors.
“Cryptocurrency is mostly a speculation game,” said grin developer John Tromp. “Grin is hurt in the short term by being speculation-unfriendly.”
Privacy Problems
Adding to grin’s woes, San Francisco-based Dragonfly Capital published research six months ago describing an “attack” that could reveal the identities of 96% of active grin users.
To date, the grin team has not fixed the vulnerability.
Ivan Bogatyy, who wrote the report, said grin’s core developers are “among the strongest engineers in the space.” However, they “faced a very hard cold-start problem with incumbents” such as monero (XMR) and zcash (ZEC) due to grin’s lack of “a robust privacy mechanism” to challenge leading privacy cryptocurrencies.
According to the people behind grin, Bogatyy’s report contains “many logical leaps” and the anonymity exploit is a known and “well-documented” problem.
Traders Are Not Grinning
Traders also seemed to have lost interest in grin. Since last June, the privacy currency’s price — quoted in dollars and bitcoin — has only dropped.
When it first launched, for example, New York City-based crypto fund Iterative Capital briefly supported grin on its over-the-counter trading desk and considered mining. But it didn’t take long for the firm to lose interest.
“Buying demand was so low and the technology was in such an incipient form that we quickly stopped bothering,” said Iterative Capital’s founder and managing partner Chris Dannen.
Grin launched during an “altcoin bear market,” said grin developer David Burkett. That the price has “so far only moved downward” is a “very similar movement to many coins launched at the same time.”
Every new cryptocurrency struggles to gain adoption early on. But for the privacy currency that promised to be the next big thing, replacing speculators with real users has proven to be an uphill battle.
Updated: 5-19-2020
Developers of Ethereum Privacy Tool Tornado Cash Smash Their Keys
Ethereum’s premier coin mixing service is now permissionless.
Tornado Cash, a privacy tool for obfuscating the history of ether (ETH) transactions, completed a cryptographic process known as a trusted setup ceremony on May 10 followed by a contract update on Monday to create perpetually self-executing code.
“With a record 1,114 contributions this was by far the largest Trusted Setup Ceremony to date,” Tornado Cash wrote in a May 13 blog post. “By comparison, all other trusted setup ceremonies had less than 200 participants.”
The ceremony, relying on a cryptographic method known as multi-party computation (MPC), makes Tornado Cash “completely trustless and unstoppable,” co-founder Roman Storm said in an interview with CoinDesk.
Tornado Cash v1 first launched in August 2019 but remained an audited “experimental software” because the developers retained control over user funds through a multi-sig wallet.
With v2, all that is gone. The MPC and Monday’s contract update effectively break up the developer key by creating a crowdsourced smart contract without a private key.
Private Transactions
Techwise, Tornado Cash leans on zero-knowledge proofs (ZKP), or mathematical evidence that a transaction occurred without revealing the information within the payment itself.
Tornado Cash joins two other ZKP-based Ethereum systems, Aztec and EY’s Nightfall. As reported by CoinDesk, privacy protocol Aztec launched a network on Ethereum for digital assets, beginning with dai, while EY also released a business-focused privacy solution for Ethereum transactions in October 2018.
Tornado Cash is more readily compared to existing coin mixers on Bitcoin because of its retail focus. CoinJoin developers Samourai and Wasabi have brought mixing to retail bitcoin investors, with Samourai available on Google Play as of February (a feature coming in Tornado Cash’s v3, Storm said).
Of course, there are other cryptocurrencies that only focus on privacy solutions, led by zcash (ZEC) and monero (XMR). The Electric Coin Company (ECC), a for-profit firm behind zcash’s development, is currently working on a bridge between itself and the Ethereum blockchain for enabling private transactions.
Just How Private?
For Tornado Cash, two questions remain: How many people will use it and how will regulators view it?
To the first, Samourai adoption after its mobile launch gives a positive signal. Bitcoin podcaster Matt Odell told CoinDesk the number of mixings on Samourai doubled month-over-month following the addition of mobile support.
That said, bitcoin (BTC) is often presented as a self-sovereign money alternative while ether’s prevailing use case has fluctuated.
Defining what ether is matters, particularly for Tornado Cash. The efficacy of a privacy protocol – from Zcash to Wasabi – is dependent on the number of users, called the anonymity set. Think of a ballpark crowd: If the stands are full of fans, it’s hard to pick out a singular person in the upper deck. Conversely, an empty stadium only helps frame the lone fanatic.
Maddie Kennedy, spokesperson for blockchain analytics firm Chainalysis, said Tornado Cash may not be the solution privacy-focused users may think it is. “While mixers, CoinJoins and solutions like Tornado Cash can make tracing funds more difficult, Chainalysis can often still follow funds through them,” Kennedy told CoinDesk in an email.
That sentiment was echoed by former bitcoin core contributor Gavin Andresen in a November blog post on Tornado Cash, highlighting additional measures such as IP-address masking that most users don’t consider.
“I won’t be surprised if there is a paper at the Financial Cryptography 2023 conference showing that 85% of tornado usage was not private; not because the cryptography is broken, but because it is really hard for mere mortals to use something like tornado (or CoinJoin or other similar technologies) in a way that doesn’t leak information about their wallet,” Andresen wrote.
Compliance Questions
There’s also compliance concerns, with the verdict still out on whether mixers are money transmitters or not.
In an email, the Financial Crimes Enforcement Network (FinCEN) told CoinDesk that mixers such as Tornado Cash could fall under the definition of a money transmitter, and therefore have “obligations” set by the Bank Secrecy Act (BSA).
For his part, Tornado Cash’s Storm said that now that the trusted setup has occurred, little can be pinned on the developers: self-executing code is self-executing code.
That doesn’t mean Storm and co-founder Roman Semenov are wanting to venture beyond the wake. In fact, Tornado Cash included a compliance feature with v2 to counter some regulatory concerns. The new version will include a cryptographic “note” which can prove to anyone presented the transaction’s history. The feature was added in light of reports of crypto exchanges freezing accounts of users who possessed coins with mixed histories.
Storm also pointed to the ECC’s and Zcash Foundation’s friendly relationship with U.S. regulators despite the cryptocurrency’s focus on privacy.
“We are in a little bit of a different situation [than other mixer wallets]. I think for us it’s very important to become compliant,” Storm said. “We do what we feel is right.”
Updated: 5-24-2020
Researchers Claim 99.9% of Zcash Transactions Are Traceable
A study into the traceability of top privacy coins reveals over 99% of Zcash users fail to utilize the protocol’s privacy features.
Researchers from Carnegie Mellon University have released a study into the privacy features of Monero (XMR) and Zcash (ZEC) — arguably the two most-popular crypto assets purporting to offer users anonymity.
The report finds that Monero’s introduction of strict security and anonymity requirements on its broader ecosystem has maintained the asset’s status as “effectively untraceable.”
Transversely, the report concludes that the lack of utilization of Zcash’s privacy capabilities on the part of more than 99% of users undermines the privacy of the overall network despite ZEC offering “strong cryptographic features.”
Zcash User Behavior Undermines Privacy
The report describes Zcash as a Bitcoin (BTC) fork that seeks “to completely break the link between the sender and the receiver.”
The researchers assert that “Zcash is not widely used” currently, citing a May 2020 survey of darknet markets indicating that “it [, Zcash,] is by far not the preferred cryptocurrency on the dark web.”
Through employing zero-knowledge succinct non-interactive arguments of knowledge, or SNARKs, ZEC is able to prevent any interaction between transaction prover and verifier — creating “a barrier that further impedes efforts to link addresses together.”
However, Zcash offers both anonymous shielded and pseudonymous transparent transactions, with the researchers finding that only 0.09% of ZEC transactions within a 30-day period made full use of the protocol’s privacy features.
“[E]ven though cryptographically Zcash is very well-founded, the users behave in a way that does not take full advantage of the shielded pool, making them traceable. As each user in the shielded pool becomes linked to the transparent pool, the overall anonymity of the ZEC ecosystem reduces as the anonymity set shrinks drastically.”
“[I]t seems that the large majority of Zcash users do not yet understand Zcash’s operating model,” the study finds, concluding that the “minuscule” set of ZEC users utilizing shielded transactions renders Zcash “effectively traceable.”
30% of XMR Transactions Found To Be Traceable
The report notes that an increasing number of altcoins have sought to brand themselves as privacy coins, claiming to offer completely private transactions in contrast to the pseudonymous transactions enabled by nearly all crypto assets.
The researchers observe several features of Monero designed to provide untraceability and unlinkability.
One-time use addresses are employed for every transaction output to prevent linkability, while traceability is addressed with one-time ring signatures — a form of zero-knowledge proof, alongside decoy inputs called mixins.
The paper also examines a number of further upgrades introduced to the protocol from 2017 onwards, finding that less than one percent of transactions carried out using XMR over the last two years were traceable according to most methods of analysis employed.
However, one model was still able to reveal transaction inputs with an accuracy of 30%.
Updated: 6-9-2020
Japanese Firm Unveils New Privacy Feature For Bitcoin Wallets
Japanese crypto firm Freessets has announced a new technology to enhance Bitcoin wallet (BTC) privacy.
According to a June 8 announcement, Freessets has created a system that allows wallets to request their addresses’ Bitcoin balances without revealing it to the servers from which they request the balances or transaction history.
The statement said that conventional Bitcoin wallets explicitly ask servers for the balance of their addresses, which links the balance, transactions and addresses. However, “using the technology Fressets has developed, it is mathematically proven that the servers cannot learn anything from the user’s query.”
The Significance Of The Development
Adam Ficsor, chief technical officer at privacy-enhancing Bitcoin wallet Wasabi told Cointelegraph that he is enthusiastic about the development. His firm’s wallet has a similar feature, but he believes Freessets’ implementation requires less bandwidth and is more suitable for mobile devices.
“Any improvement on making privacy more efficient is significant and needed,” he said, but he said he also has a few reservations. Ficsor expects that the firm’s approach will also mean losing transaction history when recovering preexisting wallets and he said that he is not comfortable with Freessets’ decision to develop its technologies in a proprietary fashion.
Updated: 6-10-2020
Human Rights Foundation Funds Bitcoin Privacy Tools Despite ‘Coin Mixing’ Legal Stigma
On one hand, the bitcoin industry has matured to include traditional brokerages and institutional traders. On the other, bitcoin privacy tech is still shrouded in a legal gray zone.
The Human Rights Foundation (HRF) took a strong stance on bitcoin privacy tech Wednesday by announcing its new Bitcoin Developer Fund. The first $50,000 grant from the fund has been awarded to freelance CoinSwap developer Chris Belcher.
CoinSwap, a mixing technique originally invented in 2013 by Greg Maxwell, is part of a comprehensive suite of privacy tools being developed by bitcoin advocates.
“The fund’s next gift, already earmarked for another developer working on strengthening Bitcoin pseudonymity at the network level, will be announced later this summer,” Alex Gladstein, the HRF’s chief strategy officer, said in an email.
HRF will also crowdsource fundraising for such privacy tech, he added, using both dollars and bitcoin, while making it “possible for activists to more safely receive donations, earn income and continue their important work under increased financial pressure.”
Belcher said he hopes to have a primitive testnet available near the end of the year.
“It will be a bit like Lightning, where there’s never a single day when it’s finished, but it slowly gets more and better features and bug fixes until one day you realize it’s everywhere,” Belcher said of CoinSwap, which he plans to keep as an open source hobby project and not a revenue-producing company.
Theoretically, any wallet provider could use the open source code to add the feature to their mobile app or desktop app. Privacy-focused wallets could even use CoinSwap features as another layer to current CoinJoin offerings.
“The bitcoin ecosystem could end up in a bad situation where it’s impossible to accept bitcoin as payment without consulting some centralized blacklist … so I talk a lot about privacy but fungibility is important too,” Belcher said. “Centralization also makes the privacy of the software worse, so I’m less interested in going in that direction … it’s all about tradeoffs.”
Adam Fiscor, co-founder of zkSNACKs, said the next Wasabi Research Club will examine CoinSwaps, though he said it would be premature to comment on it further.
Both CoinSwaps and CoinJoins are a type of non-custodial mixing, which could theoretically be layered as two privacy tools used in the same transaction. CoinSwaps are comparable to atomic swaps, while CoinJoin options typically pool disparate funds together as part of the transaction.
However, some compliance officers at leading analytics companies and crypto exchanges treat mixed bitcoin as inherently suspicious, which influences how legal authorities view the technology as well. It remains to be seen if CoinSwap features will suffer from the same stigmas as the incumbent method, CoinJoin.
CoinJoin
The technologists working with bitcoin privacy tech walk a delicate line, and tend to pay their lawyers accordingly.
Attorney Preston Bryne said he would not advise clients to use CoinJoin transactions, which he said is sometimes wrongly associated with money laundering. Many exchanges and wallet companies choose to be safe rather than sorry when it comes to legal battles.
Yet, lawyer Rafael Yakobi said there’s nothing inherently wrong with using this privacy feature, it’s all about how you report it. In the case of wallet providers, this may be possible in non-custodial scenarios where the intermediating startup never controls the assets.
“I’m quite confident that CoinJoin has not yet been mentioned in any piece of legislation. It’s not even mentioned by name in FinCEN’s guidance,” Yakobi said. “The more appropriate question is whether flagging CoinJoin transactions is implicitly required by the relevant regulations. I’m not sure about Europe, but in the U.S. it’s not an objective yes or no answer. Each business is required to formulate best practices designed to comply with the law.”
Over in Europe, it appears the law enforcement agency Europol is wary of the privacy-oriented Wasabi Wallet, because the analytics firm Chainalysis estimated $15 million worth of illicit transactions used the bitcoin wallet’s CoinJoin feature.
Critics like Reckless VR founder Udi Wertheimer and Jon Matonis of Cypherpunk Holdings, the latter of which invested in both the privacy-oriented Samourai Wallet and Wasabi-maker zkSNACKs, say blockchain analytics firms are overestimating the amount of illicit transactions when they flag mixed bitcoin.
“Exchanges, banks and regulators are being sold a false narrative if they believe that this [analytics] technology provides reliable, or more importantly, actionable results,” Matonis said. “It is purely a dangerous game of probabilities and false positives, disingenuously overstated to peddle more forensic services.”
HRF’s Gladstein recently took Elliptic, another blockchain analytics firm, to task for its “surveillance” work. “The tools you’re building regardless of your intentions will be used for policing bitcoin,” Gladstein said during a panel with Elliptic’s Tom Robinson at an event this month. “At the end of the day what you’re doing is warrantless surveillance against people in other countries.”
For his part, Matonis’s investment thesis revolves around the belief the legal community will adopt compliance norms that don’t restrict or criminalize privacy-tech like mixers.
“The concern around mixing technology, or coin hygiene, stems from the flawed thinking that cryptocurrency transactions are identical to bank transfers using fiat currency,” Matonis said. “This is a grand societal battle that must be won by privacy advocates, not because it is a cute feature or a principled position, but because it is an existential economic necessity. A peer-to-peer value transfer system fails without underlying coin privacy at its core, because the entire system would lack fungibility if all coins were not treated equally the way paper cash is today.”
This is why some bitcoiners continue to work on privacy tech, regardless of exchange policies and other hurdles.
Continued Growth
Meanwhile, CoinJoin usage continues to increase, with roughly 13,500 new Wasabi Wallet downloads this year.
So far in June, more than 10,000 fresh bitcoin were used in Wasabi CoinJoin transactions for the first time, the highest record since the all-time peak in August 2019 according to the Wasabi team.
Overall, usage has more than tripled since May 2019, when roughly 9,764 total bitcoin were used in Wasabi’s CoinJoin transactions, compared to 35,697 total bitcoin used in May 2020, they said.
And that’s not even to mention the few thousand bitcoin sent using other CoinJoin tools since the coronavirus began, including Samourai Wallet and JoinMarket. Generally speaking, usage appears to be up across the sector.
Matonis said as long as companies and public individuals focus on non-custodial, open source software, he believes privacy-tech projects will actually bear less compliance costs over time as the tools become normalized. For example, mixing protocols could become a “standard default feature” in bitcoin wallets.
“Both the bitcoin industry and law enforcement need to resist falling for the myth of blockchain forensics as perpetrated by the blockchain surveillance firms,” Matonis said of companies that routinely flag mixed coins as suspicious.
“Law enforcement methods will undoubtedly have to evolve beyond simply using money as an identity tracking device or simply relying on metadata through non-targeted driftnet surveillance,” he added. “This means employing real and sometimes cumbersome police work that doesn’t violate the rights of any individuals.”
Updated: 7-2-2020
Metamask Enhances User Privacy With New Wallet Update
Major Ether wallet service and browser extension, Metamask, introduces newly released version featuring enhanced privacy control.
Metamask, a popular Ether (ETH) wallet and browser extension, has just released a new major application upgrade.
Announcing the news on July 2, Metamask outlined that the new update, Metamask Version 8, offers a number of new features like enhanced privacy control and a new account-login system.
Updated: 7-8-2020
Bitcoin Will Never Be Truly Private Says Andreas Antonopoulos
Andreas Antonopoulos says Bitcoin will probably never have privacy features like those in Monero.
Bitcoin educator Andreas Antonopoulos says he would like to see more privacy features on Bitcoin, but they’re unlikely to happen anytime soon.
In a livestream Q&A on Antonopoulos’ YouTube channel on July 7, he said Bitcoin (BTC) was unlikely to ever implement privacy features similar to those used by Monero (XMR).
Antonopoulos said creating such features on a cryptocurrency like BTC “would create an enormous amount of controversy.” In addition, he said the structure of Bitcoin simply doesn’t allow ring signatures and stealth addresses.
“I think what we’re going to see soon is Schnorr, Taproot, and Tapscript, which open the door to a lot of improvements,” Antonopoulos said, “But they still do not involve zero-knowledge proofs or the types of ring signatures and stealth addresses that are done in Monero. Bitcoin is not a privacy coin.”
Bitcoin Privacy Features Effective?
The features to which Antonopoulos is referring — Schnorr, Taproot, and Tapscript (a scripting update to Taproot) — have been cited by others in the crypto community as having the potential to make Bitcoin more private.
The director of research at blockchain firm Blockstream Andrew Poelstra has referred to Taproot as a system which could possibly render any transaction mostly indistinguishable from one another on the BTC blockchain. However, he noted that “transaction amounts and the transaction graph are still exposed, which are much harder problems to address.”
Multisignature schemes (MuSigs) from Schnorr are another possibility. Poelstra said using this method doesn’t reveal the original set of signers, or even provide the number of signers for MuSig transactions.
Bitcoin can be better thought of as pseudonymous rather than fully anonymous, as many transactions on the BTC blockchain can still be traced even with these privacy improvements.
Updated: 7-13-2020
CoinSwap And The Ongoing Effort To Make Bitcoin Privacy ‘Invisible’
A developer known for working on enhancing Bitcoin privacy has set his sights on a new project he hopes will “massively improve” how we keep our transactions private.
Chris Belcher, who also created the technical privacy market JoinMarket, is currently working on putting to the test CoinSwap, an idea first proposed by legendary Bitcoin developer Greg Maxwell in 2013. Belcher has been focusing on CoinSwap rather than JoinMarket because he thinks it will give users better privacy, he told CoinDesk.
Belcher recently received not just one, but two grants for his efforts, showing just how excited Bitcoiners are about the potential of the project.
Though the Bitcoin network arose from a privacy-minded movement, its privacy is actually pretty thin. Just take a look at any block explorer for a glimpse of how easy it is to pull up any transaction that’s ever happened in Bitcoin’s history – as well as the transaction’s associated history.
“Right now, Bitcoin privacy is not very good at all. Anyone in the world can analyze the blockchain and then can find all sorts of information about users – their balance, their history, who they transact with and in what amounts, when – everything they spend,” Belcher told CoinDesk in an interview.
Belcher argues that this is, in some ways, worse than the financial privacy we have in legacy systems today. “The banking system, they know your transactions, but the general public doesn’t. With Bitcoin it is the general public — it is everyone that can see exactly what the user does,” Belcher added.
He added it’s important to most people that this type of information isn’t exposed to the whole world.
“Financial privacy is good for human dignity, [for example], if you don’t want your neighbors to see what charities you donate to or that type of thing, or if you’re paid in bitcoin you don’t want your employers to know what charities you donate to or what other activities you’re involved in,” Belcher added.
Coinjoins: Today’s Bitcoin Privacy
“CoinJoins” (distinctive from “CoinSwaps,” which Belcher is putting to the test) are the privacy transactions that are most popular on Bitcoin today. CoinJoins give users good privacy and are becoming more popular. Thus far, they have been adopted in the Wasabi wallet, Samourai Wallet and JoinMarket.
A CoinJoin takes all inputs from several transactions by different users and mixes them into one big, collaborative transaction. This one big transaction then sends the bitcoins mixed from different addresses out to different addresses. Because no one can tell where the spent bitcoins originally came from, the scent of the trail is obfuscated and the participants in the CoinJoin gain better privacy.
But it’s not perfect. There are still ways for people analyzing the Bitcoin blockchain (namely blockchain analysis companies) to detect when and where bitcoins are being mixed.
For one thing, the transaction sizes of mixed coins are much bigger than normal transactions because they contain so many different inputs.
Also telling is the fact they have outputs that are all the same size. “Equal output CoinJoins are very obvious. If someone sees them on the blockchain they can see that this kind of privacy protocol is happening,” Belcher said.
Why are outputs the same size? If Bob sends 0.8 BTC into the CoinJoin transaction and Alice sends 0.187 BTC and Mary sends 1.2222 BTC, and the resulting outputs are exactly 0.8 BTC, 0.187 BTC and 1.2222 BTC respectively, that coincidence is pretty obvious to anyone who is looking.
In order to preserve privacy, a CoinJoin transaction usually splits the amount of bitcoin dispensed into even pieces, say 0.1 bitcoin. So, if Alice put in 0.3 bitcoin, she will receive three 0.1 pieces sent to three separate addresses that she controls.
Most transactions don’t have a bunch of equal outputs like this. That’s why CoinJoins are easy to detect.
Indeed, there have been a few instances of cryptocurrency exchanges banning users who have evidently sent their bitcoin through such privacy services.
“They’ll be suspicious. If there’s someone analyzing the blockchain, they’ll see this is a CoinJoin, so they know this person did that. And if they see another transaction, [by comparison] they can see that it’s not a CoinJoin,” Belcher said.
CoinSwap: An Invisibility Cloak For Transactions
“CoinJoin” and “CoinSwap” have similar names and they both help to preserve privacy, so it’s easy to confuse them. But they’re different, and Belcher argues CoinSwaps “fixes many of the problems of some kinds of CoinJoins” and “is the next step for on-chain bitcoin privacy.”
CoinSwaps can be made to look invisible, Belcher said. If done correctly, a CoinSwap transaction can look just like a vanilla bitcoin transaction.
In a CoinSwap, it looks like two separate people are sending completely separate transactions. But under the hood, something else completely is happening.
Two parties, say Alice and Bob, execute such a swap. In short, Alice sends some bitcoin to a CoinSwap address. Bob sends the same amount of bitcoin to a separate CoinSwap address.
If both send the right amount of money over, the coins are “swapped.” The coins Alice sent to the CoinSwap address are sent to a new address owned by Bob, and the coins Bob sent to his own CoinSwap address are sent to a new address owned by Alice.
‘Teleporting’ Coins
Under the hood, the CoinSwap address, which is responsible for this swapping, is much fancier than a normal bitcoin transaction. It’s a multi-signature transaction, meaning it requires more than one person to sign off on it in order to send the transaction.
Usually, these types of transactions stand out on the blockchain since they look different from normal bitcoin transactions. But by including ECDSA-2P cryptography, these multi-signature transactions can be made to look just like normal bitcoin transactions. This is very much Belcher’s plan.
With ECDSA-2P in place, “Alice sends a CoinSwap to Bob and it just looks like just a normal transaction. But actually the coins have ended up somewhere else completely,” Belcher said.
This component is important. If all of these transactions look the same, people who aren’t even using CoinSwaps are getting more privacy too. There’s no way to tell if any transaction is a CoinSwap transaction or a normal one, turning bitcoin chain analysis on its head.
Similar technology will expand to the Lightning Network as well, so blockchain watchers can’t tell if any single transaction is a CoinSwap, a Lightning Network transaction or just a normal bitcoin transaction.
“CoinSwap could be said to allow bitcoins to teleport undetectably to anywhere else on the blockchain,” as a description of the technology on the Bitcoin Wiki puts it. For a deeper explanation, check out this post from JoinMarket developer Adam Gibson.
That’s not to say that CoinSwap is perfect, though. The problem with CoinSwap is that it is a much more complicated process to implement than CoinJoin.
‘As Decentralized As Possible’
In his mountain of a post, Belcher describes how to turn the idea of CoinSwap into reality.
A key reason CoinSwaps haven’t taken off since Maxwell described them seven years ago is that they’re not as straightforward as CoinJoins. So, Belcher has his work cut out for him in implementing the complexity for the first time.
His first step was just thinking about the best way to do it, outlining a number of different design considerations in the article making up his plan of attack. For one, he plans to use the Rust programming language, since it’s potentially more secure than other languages.
“I want to make it as decentralized as possible, so there’s no central point of failure that can be switched off or censored,” Belcher said. To meet this goal, he wants the “whole thing” to run over the privacy network Tor, which helps to shield IP addresses, which are kind of like a mailing address for a computer exposing where it is located.
“I think that’s quite necessary for privacy,” he said.
Belcher outlines this and various other considerations in his proposal, such as routing and using PayJoin, yet another bitcoin privacy technology, alongside it. Now that his ideas are out in the public, people can comment and make suggestions.
The next step is actually implementing it. Belcher told CoinDesk he hopes to release a minimum viable product in the next six months.
Updated: 7-15-2020
Six Months Later, Bitcoin Community Finally Debates How To Activate Taproot
The Taproot conversation is continuing with the Bitcoin community having to decide how to begin the months-long activation process.
The Taproot upgrade represents one of the most significant developments for Bitcoin’s mainchain in recent months. Despite seeing very little controversy, the community is still debating on the proper procedure on how to implement it more than six months after the BIPs were published.
The issues stem from the necessity of conducting a soft fork that would be accepted by all relevant stakeholders. According to a Reddit thread pinned in the r/Bitcoin community, “the biggest problem with activating Taproot is PTSD from the previous softfork, SegWit.”
History of SegWit
SegWit consensus in 2017 followed the BIP9 soft-fork procedure, which required 95% of all miners to signal that they upgraded to the new software and were ready to complete the fork. A time-out period existed that automatically rejected a proposal after consensus hadn’t been reached by a certain date.
The very high degree of required agreement meant that a single relatively large miner could stall the upgrade and “hold it hostage.” Allegedly, miner opposition to SegWit was due to “covert AsicBoost,” a mining enhancement technique that the upgrade would have made unusable. However, SegWit was ultimately the culmination of a community debate on block size spanning years, which was mostly resolved with the Bitcoin Cash fork.
To avoid similar controversy, two different techniques for Taproot are being proposed.
Taproot Activation Still Far Away
An alternative to BIP-9 is to codify that the upgrade will be activated after the timeout, instead of being rejected. Since this would effectively lock in the decision to fork before its activation, it is seen as a less ideal measure.
Instead, a “Modern Softfork Activation” procedure proposes a hybrid system where the upgrade would get rejected after failing to reach consensus in a year. After another six months of discussion, the community could decide to begin a two year-long procedure which would activate the upgrade at expiry. The maximum length for this procedure would be 42 months, or three years and a half.
As of right now, the timer is not yet ticking. More than six months have passed since Taproot’s initial formalization as a Bitcoin Improvement Proposal in January. Several code improvements have been pushed to it since, though they do not constitute major changes.
Taproot improves certain aspects of Bitcoin privacy related to complex spending conditions. It allows hiding the conditions that were not triggered, and can make multisig transactions look indistinguishable from single wallet transfers.
The upgrade was previously hyped up, which fueled some misconceptions on its upcoming features. Some believed that it would make the CoinJoin privacy protocol impossible to distinguish from normal transactions, though as Cointelegraph previously reported, CoinJoin is not affected at all in the final version of Taproot.
But despite the relatively uncontroversial and limited set of features, Taproot may take months — if not years — to be activated.
Updated: 8-31-2020
Secret Contracts May Soon Bring Privacy Features To Public Blockchains
Programmable privacy is about to become a reality.
Open-source Blockchain protocol Secret Network announced its intention to add privacy-based secret contracts to its mainnet. The upgrade will take place on September 15 once the proposal is passed by the community.
According to the foundation’s announcement, developers will have the opportunity to build and deploy so-called “secret” smart contracts that use encrypted inputs, outputs, and states.
Secret contracts could enable many different blockchains to utilize private data in decentralized apps without compromising their user’s personal security.
The Foundation Explained:
“Secret contracts allow for programmable privacy, allowing for arbitrarily complex data privacy controls to be implemented inside applications. The flexible encryption capabilities and controls offered by programmable privacy unlock the potential value of the decentralized web.”
Secret Network is focusing on onboarding new secret contract developers, secret node operators, and community members to help to increase the mass adoption of secret contracts among public blockchains.
The foundation will also launch secret tokens, which are privacy-based assets that are programmable like ERC20s, but private like zCash. Secret Network noted that it expects this will strengthen the mass adoption of DeFi as well.
Updated: 10-6-2020
Litecoin Relaunches Mimblewimble Testnet As Europol Targets Privacy Protocols
Litecoin’s privacy feature testnet returns as news emerges that Europe sees privacy and coin mixing technologies as major digital threats.
Litecoin (LTC) has relaunched its MimbleWimble testnet — a protocol designed to enhance privacy and obfuscate the traceability of distributed ledger transactions.
MimbleWimble is a modified implementation of the proof-of-work algorithm underpinning Bitcoin (BTC) in which blocks appear as a single large transaction, preventing the individual inputs and outputs relating to the transactions from being identified.
David Burkett, the lead developer of the MimbleWimble protocol for Litecoin, will now focus making it easier for “non-technical Litecoin users” to begin testing to functionality, in addition to ironing out aspects of the code that are “fragile.”
Burkett is targeting full activation of the protocol sometime next year, noting in a Telegram channel that it will be down to Litecoin’s miners and node operators to decide “when or even if they want to activate.”
LTC’s MimbleWimble testnet was previously launched on September 30, but was postponed due to low community participation.
Litecoin’s MimbleWimble progress comes as regulators increasingly look to crack down on privacy-enhancing crypto asset technologies, with Europol calling out privacy coins and naming decentralized marketplaces, cryptocurrency mixers, and anonymizing wallets among the top online organized crime threats.
In its ‘Internet Organised Crime Threat Assessment’ for 2020, Europol asserts that “privacy-enhanced wallet services using coinjoin [..] have emerged as a top threat,” citing Wasabi and Samurai’s respective wallets as examples. Wallets that use Coinjoin mix the coins of multiple users engaging in separate transactions, effectively providing a decentralized mixing service.
Europol asserts that the operators of darknet marketplaces are increasingly moving to integrate coinjoin wallets onto their platforms.
Europol also notes that while Bitcoin is still the dominant currency across darknet marketplaces, Monero (XMR) is emerging as the most popular privacy coin, followed by Zcash (ZEC), and Dash (DASH). The report identified Litecoin and Ethereum (ETH) as the two most popular altcoins on darknet marketplaces.
Update: 10-15-2020
The Implementation Of The Schnorr/Taproot Consensus Rules Has Been Merged Into Bitcoin Core
However, the upgrade’s activation method has yet to be determined.
This upgrade has been highly anticipated due to its potential to increase Bitcoin’s smart contract capabilities while simultaneously benefiting its transactional privacy. This is the first major protocol update since Segwit.
Updated: 10-15-2020
Bitcoin’s Next Upgrade Will Support Tor V3 Addresses
The next version of Bitcoin Core will support the latest type of Tor addresses, before they are fully rolled out.
In Brief
- The next version of Bitcoin Core will support Tor Network’s V3 addresses.
- Tor V3 addresses offer stronger cryptography and enhanced security.
- The old V2 addresses will become obsolete on October 15, 2021.
The next version of Bitcoin Core will support Tor Network’s latest V3 addresses—that will fully become the new standard next year—according to Pieter Wuille, a co-founder and former engineer at Blockstream.
Bitcoin Improvement Proposal (BIP) 155, which contains details of the Tor support, has been merged into the current Bitcoin reference implementation. It will be pushed into Bitcoin Core version 0.21.
The Tor Network is based on open-source software and enables anonymous communication over the Internet. In July, its developers announced that the network’s V2 addresses—that have been in use over a decade already—will be “retired” on October 15, 2021. They will be substituted with the new V3 addresses that have been in development since 2015.
“As humankind’s understanding of math and cryptography evolved, the foundation of version 2 became fragile and at this point in time, unsafe,” said the announcement, adding that “[In 2015], a large scale development effort spanning over 3 years resulted in version 3.”
Updated: 10-16-2020
Bitcoin’s Taproot Is Ready To Go, But It’s Unlikely To Be Included In The Next Release
Developers don’t want to move too fast.
The Bitcoin Improvement Proposals 340 through 342 were merged into the Bitcoin codebase on Thursday, signaling that the anticipated Taproot upgrade is ready.
Taproot and the associated technology of Schnorr signatures are considered to be the most important upgrade for Bitcoin in the past year. It is primarily a privacy improvement for complex spending conditions on Bitcoin like multisig transactions, time locks and other conditions based on Bitcoin Script.
As Cointelegraph reported previously, Taproot hides every additional spending condition beyond the one that was activated. For example, a transaction might be executed immediately if all four multisig signers agree, or it could require a certain amount of time to pass before funds are unlocke if only three out of four signers are present.
Normally, an outsider is able to identify every possible condition, but with Taproot they will see only the one that was eve triggered.
Furthermore, thanks to Schnorr signatures, a pure multisig transaction can be made indistinguishable from normal transfers. It is worth addressing that Taproot makes no changes to mixing protocols like CoinJoin, which will remain easily distinguishable.
While the initial code for Taproot was submitted for review in January, some complications primarily related to Schnorr signatures required an extensive amount of refinement.
The proposals have now been fully reviewed by Bitcoin core developers and are ready to be included in a client release. Pieter Wuille, the lead developer for Taproot, told Cointelegraph that “it’s all done, except activation.”
Cointelegraph previously reported that consensus for activation may require some time to be reached. The process could potentially last for years, though Taproot is generally considered much less controversial than previous upgrades like SegWit.
The process starts as soon as the activation code is included in Bitcoin Core, allowing miners to signal approval for its inclusion. But Taproot seems to have come slightly at the wrong time for immediate activation.
Jonas Nick, researcher at Blockstream and Bitcoin core developer, told Cointelegraph that “Taproot is not ready for activation yet.”
He explained that activation logic is generally not included in a major release, referring to the upcoming 0.21 version. The codebase reached “feature freeze” on Thursday, with the base Taproot code making it just in time. Nevertheless, nly bug fixes will be added from now on. Explaining why developers are cautious, Nick said:
“Major releases can contain changes to dependencies and interfaces (e.g. RPC). Users should be able to run softfork activation logic without the additional work required to be compatible with a new major version.”
The logic to activate Taproot on mainnet is likely to be included in a future minor version, but in the meantime, Nick said that “Taproot could be activated on something like signet or testnet if someone produced the code for that,” as the raw implementation is already present.
Updated: 10-30-2020
Bitcoin Developers Still Divided On Specifics Of Taproot Activation
The code for Taproot, Bitcoin’s biggest upgrade in years, is finalized and has been packaged into a forthcoming update. Only, it’s not ready to be deployed yet because Bitcoin developers have differing opinions on the best route to activation.
Taproot will enhance Bitcoin’s smart contract capabilities by implementing a new digital signature scheme, Schnorr. Implementing the upgrade requires a “soft fork” of Bitcoin’s code, and there are a few competing proposals for how to activate it.
In a bid to expedite implementation discussions, Bitcoin Core contributor A.J. Towns recently surveyed 12 other developers who have been active in the implementation process to glean their thoughts on what activation should look like.
The results of the survey show that, while developers are generally aligned when it comes to the big picture of Taproot’s activation, they disagree on the details. As they debate the finer points, the developer’s conservative, careful deliberation may seem like nitpicking to outsiders.
But it shows that so-called “soft-fork” upgrades like Taproot are not entirely riskless events – and that the specter of the controversial Segwit soft fork has haunted discussions.
Taproot Activation Proposals, Explained
The Segwit transaction load increase was Bitcoin’s last soft fork, or an upgrade that is “backwards compatible,” meaning software running the old version of the code can still interact with the upgraded version.
Segwit’s activation was anything but smooth and relied on tweaks along the way after miners failed to adopt the upgrade in its first year. To keep the upgrade from failing, node operators – those Bitcoin users who run Bitcoin’s software and keep a copy of its ledger – adopted the upgrade and miners followed suit after these node users threatened to reject transactions from the miners.
In a perfect world, both node users and miners would upgrade simultaneously to ensure no conflict would “split” the chain – or result in two rival factions supporting two different versions of Bitcoin’s code.
Even though Taproot is a non-controversial upgrade, the memory of Segwit is making developers cautious when evaluating this latest upgrade.
Two Proposals
Two of the leading implementation proposals for Taproot rely on a mix of miner signaling and user activation. BIP 8, introduced in 2017 by Bitcoin developers Luke Dashjr and Shoalinfry, would include a signaling period for miners; if enough miners don’t activate to reach consensus on the upgrade, then a “flag day” for activation would automatically upgrade Bitcoin nodes that have downloaded v0.21 of Bitcoin Core.
These nodes would reject blocks and transactions from miners who do not support Taproot, so in theory, this method would incentivize miners to adopt the new ruleset lest they lose out on profits.
In a second Taproot implementation proposal, Core developer Matt Corallo’s Modern Softfork Activation, fuses BIP 8 with BIP 9 (the latter being the proposal originally adopted to activate Segwit but which proved inadequate).
Corallo’s hybrid model first includes a one-year signaling period for miners. Second, if a super-majority of miners does not update during this timeframe, then the upgrade would be subject to a six-month review to make changes (if any) to the proposal.
The third and final step is a BIP 8-style activation period of two years, with a non-mandatory flag-day for node users to activate the update.
What Bitcoin Developers Think
For the first question in his survey, AJ Towns asks developers what percentage of miners need to signal an upgrade for it to be considered a safe majority. Eight believe that nothing less than 85%-95% would be sufficient. The thinking is that anything less threatens a network “split” where some miners run the older code and some the newer code, which would create two conflicting transaction histories.
Failing a miner-signalled activation, seven respondents think a flag day for node-enforced activation could come as soon as 12-18 months after activation begins. If too few miners adopt the upgrade, this would mean nodes could enforce the Taproot ruleset and only accept blocks from miners who also signaled for the upgrade.
“In a perfect world, both node users and miners would upgrade simultaneously to ensure no conflict would “split” the chain – or result in two rival factions supporting two different versions of Bitcoin’s code. “
Almost all of the developers surveyed want to wait to see if miners and users adopt the upgrade on their own before deciding on a hard date for flag day (if there’s enough early support, a flag day may not be necessary at all).
If activation doesn’t come to pass through voluntary activation, then a flag day activation is the last option on the table. Most respondents were in favor of a mandatory flag day to automatically signal the update. This would mean updated nodes would reject blocks from miners who haven’t signaled for the upgrade.
Disagreements On The Finer Details
So-called forced signaling through the flag day would have the benefit of making Taproot default on any Bitcoin Core node running v.21; in turn, these nodes would only accept block data from miners who have also signaled the update, so in theory this would encourage miners to upgrade lest they lose their business.
But What If The Miners Have Node Users Who Do Accept Their Blocks?
This is one caveat to forced signaling: If too many miners and node users don’t accept Taproot and refuse to update their software, then the network could split into two competing chains. If enough economic interest backs the “old” version of Bitcoin, then the result could be two competing assets.
This outcome is partly why some developers, like Matt Corallo, think that forced signaling is unnecessary.
Since Taproot has been largely uncontroversial, it would be a political risk to force signal the upgrade, he argues. He considers the activation method a relic of Segwit’s “user-activated soft fork,” a proposal to activate Segwit through similar means after miners failed to adopt the upgrade. Segwit was very controversial and political. Taproot is not, but Corallo believes enforced signalling threatens to make it that way.
In his post, Towns writes the mandatory signaling would be a way to definitively enforce Taproot’s network-wide activation after enough consensus has been established through discussion and miner support.
“If you want to maximize the number of nodes that will enforce the rules should a flag day occur, but also only choose the flag day after an initial activation attempt is already widely deployed, then you have no choice but to make signaling mandatory when the flag day occurs,” Towns writes.
What’s The Holdup?
Towns introduces an alternative activation proposal in the survey which features a four-year activation time frame. As ever in Bitcoin development discussion, this, too, received some pushback.
“Once the decision to activate has overwhelming support from developers and users, the longer the timeframe for activation (beyond that practically required for miners to safely upgrade) the more things that can go wrong,” former Bitcoin Core developer Eric Lombrozo said to Towns on Twitter.
Risks aside, if most developers and Bitcoiners think Taproot is a shoe-in for an upgrade, it shouldn’t take four years to activate, especially since it has already been so-long in the making.
After all, if Taproot’s been in the works since 2018, shouldn’t miners and node operators know what to expect?
As Blockstream CEO Adam Back put it on Twitter, “Taproot can’t be a surprise after several years.”
Updated: 11-4-2020
Blockstream Is Working on Simpler, More Private Multi-Sig Bitcoin Transactions
With Bitcoin’s long-awaited Taproot upgrade on the horizon, the engineers at Blockstream are working on a new scheme to improve multi-signature transactions.
These transactions, which require signatures from more than one private key to authorize spends, will stand to benefit from Taproot. This upgrade implements Schnorr signatures into Bitcoin’s codebase, a cryptographic signature scheme that will make creating and executing smart contracts easier on the network.
In a post-election day blog post, Blockstream engineers Jonas Nick and Tim Ruffing lay out a new multi-signature design that would reduce the technical complexity of multi-signature transactions in a way that still preserves privacy.
Nick and Ruffing, alongside French National Security Agency member Yannick Seurin, published a cryptographic e-journal on this MuSig2 design that is currently undergoing peer review.
‘Non-interactive Signing’
MuSig2 combines the strengths of the two leading multi-signature designs without sacrificing trade-offs.
Bitcoin’s oldest multi-sig trick, the ‘CHECKMULTISIG’ OP-code, for instance, requires less communication from the signers of a multi-sig transaction but is less private than the MuSig1 multi-signature scheme, which improves user privacy at the expense of adding extra steps to the signing process.
Specifically, MuSig1 requires the parties in a multi-signature transaction to communicate in multiple rounds to approve a transaction.
MuSig2 would retain all the privacy guarantees of MuSig1 while only requiring two rounds of communication between signers to approve a transaction (e.g., Alice generates a 2-of-3 multi-signature transaction she sends to Bob for approval; Bob signs the transaction, sends it back to Alice and the transaction is approved).
“It offers the same functionality and security as MuSig1 but makes it possible to eliminate almost all interaction between signers. With MuSig2, signers need only two rounds of communication to create a signature, and crucially, one of these rounds can be preprocessed before signers know the message that they want to be signed,” the blog post explains.
Besides improving general multi-signature wallets, MuSig2 could stand to benefit Lightning Network privacy and improve so-called threshold signatures that are often used by exchanges and custodians for fund storage.
If Taproot is adopted in the coming months, then Blockstream will replace the MuSig1 standard with MuSig2 in a code library for Schnorr signature schemes. The post also hints that Blockstream’s Liquid sidechain may run the Taproot code early to test the multi-signature scheme before it is ready for deployment on Bitcoin’s mainnet.
Updated: 11-18-2020
Bitcoin Mining Pools Begin Signaling Support For Taproot/Schnorr Activation
Poolin has published a new tracker for mining pools that are signaling for Taproot, and in-development upgrade for the Bitcoin network that aims to boost transaction privacy.
As previously reported, Taproot — and, by extension, Schnorr signatures — are being bundled as part of a soft fork that, if approved and integrated, would represent the first significant update to Bitcoins since the addition of Segregated Witness. Taproot aims to make all transactions appear the same to outside observers, regardless of its composition or style.
According to Poolin’s tracker, three pools are signaling support for the Taproot/Schnorr soft fork. In addition to itself, BTC.com and Slush Pool are doing so.
The code for Taproot was merged into the library of Bitcoin Core last month, representing the final stage before the official deployment. How that process will exactly play out remains to be seen — as noted by Poolin, there are two approaches to activation for node operators (including miners).
As of the time of writing, Poolin accounted for nearly 18 percent of mined blocks in the past 24 hours, according to BTC.com. BTC.com accounted for about 9% of blocks, and Slush for about 2%.
Updated: 11-19-2020
Majority of Bitcoin Hashrate Signals Support For Taproot Scaling, Privacy Upgrade
Bitcoin mining pools representing over 54% of the network’s current hashrate have signaled support for the scaling and privacy protocol upgrade Taproot, merged into Bitcoin Core last month.
Bitmain’s Antpool backed the protocol upgrade Thursday morning in a message sent to Poolin, the pool told CoinDesk, joining five other pools in Poolin’s Taproot Activation initiative and pushing the percentage of hashrate in support of the upgrade over 50%. Antpool plans to publicly express its support in a forthcoming block’s coinbase.
Poolin’s vice president, Alejandro De La Torre, told CoinDesk he is “beyond happy” that most major mining pools have responded affirmatively to their “consensus-built effort” to support Taproot.
Notably, Binance Pool is the only top-five pool to not yet support Taproot.
Taproot aims to improve transaction privacy and enhance Bitcoin’s smart contract functionality. As an added bonus, it’s also designed to keep Bitcoin’s blocks small, with block space as accessible as possible.
“The only uncertainty with Taproot is when and how it will be activated,” said Daniel Frumkin, engineer and technical writer at Slush Pool, in a direct message with CoinDesk.
“In the end it should be a straightforward process with minimal drama,” he added, noting that Taproot is “not controversial.” Frumkin contrasted this proposed upgrade with the heated industry-wide disagreements caused by the 2017 SegWit2X proposal, which many miners also supported.
Seeing any miners opposing the Taproot upgrade would be a shock to Frumkin. “I’d expect the rest of the major pools to signal support in the following weeks,” he said.
Updated: 11-22-2020
Privacy Coins No More? Ciphertrace Files Patents For Tracing Monero Transactions
The firm claims it will be able to identify XMR used for illicit purposes to support criminal investigations.
Crypto analytics firm CipherTrace announced on Friday that it had filed two patents for technology capable of tracing transactions for privacy coin Monero.
In a Nov. 20 blog from CipherTrace, the firm stated that the patents would include forensic tools to explore Monero (XMR) transaction flows to assist in financial investigations, statistical and probabilistic methods for scoring transactions and clustering likely wallet owners, as well as visualization tools and ways to track stolen or illegally used XMR.
“CipherTrace’s Monero tracing capabilities will allow [Virtual Asset Service Providers] to identify when inbound XMR may have criminal origins, allowing them to adequately risk rate customer transactions per any required regulations,” the blog stated. “[Our] goal is to enable the detection of criminal users, therefore increasing the safety and sustainability of privacy coins like Monero in the future.”
While Bitcoin (BTC) is still the preferred medium of exchange for many darknet market users, there has been increasing acceptance for privacy coins like XMR. Law enforcement agencies have not yet determined a reliable way to trace Monero, and firms like CipherTrace have an opportunity — the company has reportedly been working on a means to trace XMR transactions since early 2019.
CipherTrace CEO Dave Jevans told Cointelegraph in August that the firm developed the first tool for tracking Monero transactions. Such a tool could potentially support investigations of crimes and reduce incidents of money laundering.
The company has stated it developed these Monero-tracing tools as part of a project with the U.S. Department of Homeland Security, but the latter isn’t the only government agency looking for a way to identify XMR wallets, transaction dates and times. In September, the Internal Revenue Service announced it would give a bounty of up to $625,000 to anyone who can break Monero.
Capabilities for CipherTrace’s tracing tools have not yet been confirmed. One Monero Outreach representative told Cointelegraph in October that they would be “highly suspicious of any claims that corporations can trace Monero transactions” and any firm that did so would be unlikely to “trace the wallets or amounts for any transaction.”
The price of Monero is $123.37 at the time of publication, having fallen 3.6% in the last 24 hours.
Updated: 12-15-2020
‘Secret’ Bridge Turns ERC-20 Tokens Into Privacy Coins
“Secret Tokens combine the programmability of ERC-20s with the privacy of coins like Zcash or Monero.”
An open-source blockchain protocol called the Secret Network is now offering privacy features for the Ethereum blockchain and 14 ERC-20 tokens.
According to a Secret Network blog post, the protocol launched its Secret Ethereum Bridge on the mainnet today, which is designed to allow Ether (ETH) and all ERC-20 token holders to create programmable versions of their assets with privacy features. The Secret Network compared these “secret” tokens to privacy coins like Monero (XMR):
“Secret Tokens combine the programmability of ERC-20s with the privacy of coins like Zcash or Monero. Interactions with Secret Token contracts are encrypted, viewable only to address owners or holders of their viewing key.”
Secret Network said that it would initially offer these privacy features to 14 ERC-20 tokens, including ETH, Yearn.Finance (YFI), Uniswap (UNI), Band (BAND), Compound (COMP), Chainlink (LINK), Aave (AAVE), Kyber (KNC), Synthetix (SNX), Ocean (OCEAN), Maker (MKR), Dai (DAI), Tether (USDT), True USD (TUSD), and wrapped Bitcoin (WBTC).
The latest Ethereum announcement is part of a broader plan from the Secret Network to bring privacy features to public blockchains. Developers can build and deploy the protocol’s “secret” smart contracts that use encrypted inputs, outputs, and states. These contracts reportedly allow a blockchain to utilize private data in decentralized apps without compromising users’ personal data.
The protocol said it was also planning on launching bridge mining rewards starting in January. Crypto users can earn Secret’s SCRT tokens for keeping their assets locked on the Secret Ethereum Bridge.
Updated: 12-25-2020
Blender Launches Decentralized Privacy Bitcoin Wallet

Launched in September 2020, Blender Wallet by Blender.io, a recognized privacy team, represents a new-gen approach to anonymous Bitcoin (BTC) wallets. It merges an unparalleled level of decentralization and an intuitive user interface.
Why Do You Need A Decentralized Bitcoin (Btc) Wallet With A Built-In Mixer?
A decentralized cryptocurrency wallet refers to a type of service with zero points of centralization. This means that it does not rely on the server, node or website. Users of decentralized wallets are solely responsible for their keypairs.
Don’t Trust; Verify
Decentralized (trustless, noncustodial) wallets eliminate the need for its customers to rely on the service team when storing crypto and authorizing/receiving transactions. Thus, their customers are less vulnerable to the issues typical with CEXs: account restrictions, withdrawal delays, government shutdowns and so on.
It is very difficult for malefactors to hijack users’ data or coins when they are not allocated to centralized storage.
Privacy First
Also, issues of tracking and deobfuscating addresses and transactions are really thorny in 2020. Regulatory watchdogs in many countries are exploring more and more tools to find out how Bitcoiners use their assets and for which purposes?
Even the coins that emphasize their devotion to privacy – Monero and ZCash, for example – are targeted by regulators. Thus, using a mixer, a service that “blends” the transactions to obfuscate their routing, is a must for contemporary crypto users.
Introducing Blender Wallet: When Privacy Meets Powerful Functionality
Blender Wallet is a flagship B2C product by top-tier privacy-focused team Blender.io. It should be referred to as a noncustodial decentralized multi-purpose Bitcoin (BTC) wallet with built-in coin mixer.
Main Functions Of Blender Wallet
First of all, Blender Wallet provides its customers with a safe and secure environment for storing their Bitcoins (BTC). Blender Wallet supports Segregated Witness Bitcoin (BTC) scalability technology and assists users in creating SegWit addresses for fast and cheap transfers.
All Blender Wallet transactions are obfuscated through the in-app Bitcoin (BTC) mixer. Thus, all user activity in the Bitcoin (BTC) network becomes literally untraceable. It is the pioneering product that allows users to reach that level of anonymity without special blockchain skills.
At press time, Blender Wallet is available as a web interface, while the mobile application for Android devices is coming soon.
Useful Features For Retail Payments
Blender Wallet is one of a few wallets that allows all clients to manage multiple Bitcoin (BTC) addresses simultaneously. It may be of crucial importance for freelancers or contractors. On the other hand, employers who decided to pay employee salaries in crypto will enjoy a “one-to-many” transaction feature.
Users can label their transactions in one click to manage their expenses easily. For instance, Bitcoiners onboarded by Blender Wallet can identify payments related to work, recreation and entertainment, digital bank transfers and other categories.
Similar labels can be attributed to addresses as well. Once labeled, the owner of the wallet can search for addresses and transactions using customized keywords.
All transactions authorized and received with Blender Wallet are charged with zero service fees, so clients only pay the miner’s commission to have their transactions included in new blocks.
Setting Up Your Decentralized Bitcoin (BTC) Wallet With Blender Wallet
Since Blender Wallet is a KYC-agnostic platform, it does not require users to disclose their critical personal data, e.g., real name, phone number, email addresses and country of residence, among other things.
It takes five steps maximum to get your Bitcoin (BTC) account set up with Blender Wallet.
1. First, you need to click on the “Create” button on the main page and pass captcha to avoid spam registrations.
2. In the second step, the user creates his/her own encoded mnemonic (like an ordinary password). This will help the user to access funds but will not be sufficient unless he/she inputs a seed phrase (see next step).
3. The third step is a crucial one. Blender Wallet gives the user his/her seed (“mnemonic”) phrase of 24 words. This phrase should be secured in physical storage. Blender Wallet does not store passphrases and mnemonic phrases.
4. The next step just asks the user to verify his/her mnemonic phrase, or four words out of 22.
5. Two-factor authentication is the last step. It is not necessary and can be skipped. If it is important for you, you should prepare a second device through which to authorize your usage of Blender Wallet.
Once this step is completed or skipped, the Bitcoiner can enjoy a seamless anonymous BTC storage and transaction experience with Blender Wallet.
Bottom Line
Blender Wallet by Blender.io represents a new type of privacy-focused Bitcoin (BTC) wallet. It merges the benefits of full anonymity and intuitive user experience. Its functionality is enhanced by unparalleled retail payment features.
Also, Blender Wallet offers all of its clients in-app Bitcoin (BTC) mixers to obfuscate critical transactional data.
Updated: 12-28-2020
Bitcoinmix Makes A Difference In Anonymous Cryptocurrency Use
There have been concerns raised about the privacy associated with cryptocurrencies such as Bitcoin and Ethereum.
Many users would want to have a measure of privacy but unfortunately, such features were not incorporated in the codes of these coins. This is why a Bitcoin mixing service, Bitcoinmix.org was established to give people access to this anonymity while using Bitcoin and Ethereum.
The company has taken cognizance of the need for anonymity and developed an algorithm that is resistant to the conventional blockchain analysis, thereby ensuring that clients’ transactions are effectively anonymized.
The company achieves this through the holding of large volumes of bitcoin and ethereum with which it effectively mixes the incoming coins of the customers. This obfuscation ensures that the mixed coins are dissociated from the transaction made using the originating wallet.
The company’s services has been of immense help to users who hold large volumes of coins and would not want to have unwanted attention. Every transaction made on such wallets that are channeled through this service isolates the wallet from the transaction.
Other clients are those who want to keep away malicious players such as hackers. This is even so important for users who have substantial volume of coins in their wallets. Bitcoinmix which started as a service that focused on mixing bitcoin has grown in recent months. The company expanded its blending service to include the mixing of ethereum in addition to its bitcoin mixing for which the company is known.
With the introduction of ethereum mixing service, users of ether can now access the anonymizing service. So sending and receiving of ether can be done anonymously.
Bitcoinmix has been rated as one of the oldest and reliable coin mixing services in the industry as it has built a reputation as a reliable mixer in an industry in which credibility means everything. This is despite the fact that blockchain was invented to exclude third party involvement in transactions and business.
The service does not take away from the concept but ensures that the lapses created by openness of the blockchain are ameliorated. This is why our services have become popular over time.
The company’s services can be accessed at Bitcoinmix.org. The easy to use platform was designed in a way in which the client doesn’t need to input personal details in other to use the service. Essentially, the customer sends their coins which are mixed and then other coins held by the company are sent to the address designated by the customer.
Equivalent volume of the deposited coins meant for mixing are sent to the customer. These coins are just like newly minted and have no history which could be traced through blockchain analysis.
So if you’re thinking of ways to use cryptocurrencies anonymously, the company’s service is what you need. Even though the focus in the meantime is on blending bitcoin and ethereum, there’s hope that this service would be extended to other coins that their users need to conduct more anonymous transactions.
Updated: 12-30-2020
All Major Mining Pools Now Support Taproot, Bitcoin’s Biggest Upgrade In Years
Binance Pool, the mining pool run by one of crypto’s biggest exchanges, is prepared to support Taproot, a good omen for the next major Bitcoin upgrade. The addition of Binance Pool to the “yes” column means that all the major pools are now on board.
Taproot is a scaling and privacy change that will be the biggest upgrade the digital currency has received in years – and it’s far less controversial than the last one.
According to crypto mining pool Poolin VP Alejandro De La Torre, Binance Pool says it will support the Taproot upgrade, clearing up any ambiguity, since the pool was the only one with over 10% of the network that hadn’t said “yes” to the proposal.
Binance Pool represents 11% of the Bitcoin mining hashrate, so its support pushes mining pool support up to about 91% of the hashrate.
Binance did not respond immediately to request for comment.
De La Torre leads Taproot Activation, an initiative to find out if there is agreement on Taproot as a change. According to the website, a few smaller mining pools, including Lubian.com and BTC.TOP, have not responded about whether they support the upgrade or not.
Signaling For Taproot
This support from miners comes in stark contrast to SegWit, Bitcoin’s last major upgrade, which activated in 2017. SegWit was deployed by way of BIP 9, requiring that 95% of mining pools flag support the change before the change would officially activate. To block the change, mining pools simply did not flag,
So far, mining pools have no problem with Taproot. Binance Pool’s support is a bellwether sign that the change could activate soon if no one finds some sort of fatal flaw in it.
This news is particularly consequential because if Taproot is deployed by way of BIP 9, then mining pools will need to flag that they’re ready for the change before it can activate.
But there’s still some debate about this process. The mechanics of Taproot itself are not controversial. Bitcoin’s most active developers all but universally agree it’s a positive change.
Still, how to deploy the change is still up for debate. Over the last several months, developers have been discussing the best way to deploy Taproot. To oversimplify a complex debate, some think BIP 8 would be better because it doesn’t allow mining pools to block the change out of sluggishness or apathy.
Knowing that mining pools, such as Binance Pool, support the change might give BIP 9 a boost.
Updated: 1-13-2021
Bitcoin Miners, Developers Narrow Down How Taproot Will Be Activated
* Bitcoin miners representing roughly 91% of the network’s hashpower have demonstrated support for Bitcoin’s biggest upgrade in years, Taproot.
* These activation methods vary the length of time required and whether or not to include a measure that would force the upgrade through full nodes with a “user activated soft fork.”
* Given miner support, Bitcoin developers believe the upgrade should activate without issue, regardless of the specific proposal chosen.
Now that most all major mining pools have pledged support for Bitcoin’s Taproot upgrade, all that’s left is the actual activation – but the members of Bitcoin’s open-source community have to pick the method first.
There are currently a handful of proposals vying for attention among Bitcoin’s stakeholders. Summing up the differences between them, some of these allot longer activation times than others, and some would allow the upgrade to be “forced” through full node activation if miners don’t put their hashrate where their mouth is when the time comes.
Bitcoin Upgrade: Multiple Paths To One Destination
Bitcoin’s biggest upgrade in half a decade, Taproot will enrich Bitcoin’s smart contract scripts, making it easier to execute highly complex transactions on the Bitcoin blockchain. Among other things, this will improve multi-signature software and privacy for the network.
Bitcoin developers have proposed multiple ways to bootstrap the upgrade, but they all rely on some version of Bitcoin Improvement Proposal 8 or Bitcoin Improvement Proposal 9 (BIP8 and BIP9, for short). Each proposal is similar but offers slightly differing approaches to activating the upgrade, which will require cooperation from both Bitcoin miners and node operators to go smoothly.
There are two primary versions of BIP8 vying for attention: one version, called BIP8 (true) includes a “flag day,” at which point the update will be forced via full node activation, even if miners fail to adopt it; and one version, called BIP8 (false), wherein the upgrade simply fails if miners don’t adopt it.
“True” designates that the BIP includes forced activation, whereas “false” designates a version of the BIP that doesn’t have forced activation.
Why the addition of the forced activation, you might be wondering? One apprehension going into activation discussions has been whether or not mining pools would adopt the upgrade, considering miner reluctance stymied SegWit’s activation in 2016 and 2017.
Mining pools that represent roughly 91% of Bitcoin’s hashrate, though, have announced their support for the upgrade as part of an initiative spearheaded by Alejandro De La Torre, a VP at bitcoin mining firm Poolin.
Torre said Poolin’s takeaway from the survey is that “BIP9 is the most favorable choice” for activation.
Bitcoin cannot tell time, so BIP9 allots a signaling period that is gauged by Bitcoin’s block time (whereby a pre-defined period of time is measured via Bitcoin’s block schedule, which can be erratic). If enough miners adopt the upgrade during this timeframe, it is locked in and considered successful; if this threshold is not reached, then the upgrade fails.
Bitcoin Miner Support Could Mean Easier Activation
With miners behind the upgrade, BIP9 could provide the quickest and easiest route to activation, Ben Carman, a Bitcoin developer who has helped review Taproot’s code, told CoinDesk.
“In the beginning I was in favor of BIP8 because I was worried about miners being able to block the upgrade. However, with things like taprootactivation.com I have moved to being in favor of BIP9. It seems we have basically everyone on board to do the upgrade and BIP9 would be the simplest, as well as only require a couple lines of code to be started. Other methods would require larger code changes to implement new activation logic.”
The other activation methods Carman mentions, BIP8’s differing versions, are similar to BIP9 sans a crucial tweak: BIP8 includes an option to force the update through a “flag day” if miner signaling fails (this option would be employed with the BIP8 [true] activation method). Additionally, a smaller change measures activation time by block height instead of BIP9’s use of block times.
This change means that if miners don’t adopt Taproot, the update can be forced through full node activation at a certain date with BIP8 (true), or the upgrade can be paused per BIP8 (false) and resumed later.
If enough miners don’t adopt the upgrade during the signaling period for BIP9, though, the process fails and must be started over from the beginning.
‘BIP9-Style Activation’ Could Come From BIP8
BIP9 has been used in the past for Bitcoin soft forks (upgrades that are compatible with previous software versions). It was originally used to activate the SegWit upgrade, but not enough miners signaled for the update so other means were required. Under this scheme, if not enough miners support an upgrade the signaling period for it merely expires and the process can be repeated.
Jonas Nick, a Bitcoin Core developer who has been one of the leads on Taproot, told CoinDesk that “BIP9 style activation is the least disruptive path and therefore a reasonable choice,” but that it would most likely come from BIP8, hence why this route is called the “BIP9 equivalent.”
Assuming the upgrade will be adopted during the signaling period, the upgrade would be adopted as outlined in BIP9 (i.e., via complete miner support), but using BIP8’s activation logic, which measures the activation window through block times and which can easily be tried again if the upgrade fails.
That’s why, while “no one can say for sure,” Nick believes that fellow Taproot development lead AJ Townes’ proposal (a slight modification of the so-called “gently discourage apathy” route), could win out.
Taproot ‘Flag Day’
Under this scheme, miners would have a year to signal for the upgrade. If miners representing 95% of Bitcoin’s hash power signals for the upgrade during this period, Taproot activates without further action. If not, the update undergoes a reviewal period during which developers and miners cooperate to iron out the kinks.
After this period ends, a “flag day” would be coded into the update to force the upgrade through mandatory signalling, whereby node operators would only accept blocks from miners who support Taproot.
This would effectively be a “user-activated soft fork” (UASF), the same method proposed to activate SegWit, though the method proved unnecessary because miners adopted the update after the UASF proposal gained traction. This method is known as “forced activation.”
By giving miners plenty of time to upgrade but also maintaining a flag day just in case, the proposal is meant to discourage miners from “not updating out of laziness,” KoinKeep Bitcoin wallet developer Dustin Dettmer told CoinDesk.
Townes has sketched out what this proposal would look like, but the code for it has not been included into Bitcoin’s software. The method includes BIP8 (false), so this code would need to be reviewed and inserted into Bitcoin Core first, Nick said.
Taproot: Rooted In Risk?
Even as Nick and Townes put their weight behind the modified BIP8 implementation, Matt Corallo, another reviewer of the Taproot code, believes the activation method is too risky, even if miners are largely on board.
“The forks in Bitcoin, for better or for worse, define the process and benchmark by which future changes are made and evaluated,” he told CoinDesk. The SegWit block size wars, he continued, set “an incredibly high standard” for how “on-its-face simple change[s]” are made to Bitcoin’s software – namely, with conservative deliberation that takes as few risks as possible.
Corallo believes the mandatory flag day activation method proposed in other methods is unnecessarily brazen and indicates too much influence from Bitcoin’s developer community, unless all other activation methods have been exhausted.
“Some of the proposed activation methods being discussed throw [the lessons learned from SegWit] away, setting a visible precedent that Bitcoin can be changed with almost only developer buy-in and with coercive and marginally riskier activation, opening the door to re-litigating years-settled debates.”
Corallo “doubts activation [will] be an issue,” but he concluded by saying, “I see no reason to take that risk unless all other options have been tried.”
Offering his alternative, Corallo’s own Modern Activated Soft Fork (MASF) takes bits and pieces of both BIP8s. This activation path involves a year-long signaling period for miners. If enough miners do not update during this timeframe, then the upgrade would pause per BIP8 (false) to be subject to a six-month review to make changes (if any) to the proposal.
If, after this point, Taproot still doesn’t have enough support, then a two-year period begins wherein node operators can push the update through an opt-in, non-mandatory flag day.
As opposed to a mandatory option, which would force activate Taproot on all nodes running the latest version of Bitcoin on the flag day, this opt-in flag day would get Taproot up and running only on nodes whose operators chose to upgrade, not the entire network.
Opponents of the MASF proposal say the long activation timeline could result in apathy among users, where the time-lapse has them losing interest in the upgrade so they don’t adopt the code. Still others say that it’s an unnecessarily lengthy process, especially for an upgrade that would benefit multi-signature and privacy technologies waiting for Taproot to bring their projects to fruition.
Bitcoin Miners’ Preferences
Only one of the respondents to Poolin’s miner poll, BTC.com, favors Corallo’s method. Slush Pool and Ant Pool both responded in favor of the original BIP 8. Poolin itself and NovaBlock want the BIP9 equivalent wherein BIP8 (false) is used sans the flag day, while Luxor is putting its chips on BIP9.
Regardless of which proposal wins out, Jonas Nick conservatively estimates that Taproot’s activation will kick off sometime this year. Given that the upgrade is non-controversial and miners support it, the actual difference between each activation method could be of little consequence, Nick said.
“In my perception, because Taproot has overwhelming support many developers would be fine with any reasonable proposal,” he concluded.
Updated: 1-15-2021
Tor-enabled Bitcoin Nodes Are Back After Bug On Network
Anonymous Tor-enabled Bitcoin nodes normally make up as much as 25% of totally reachable Bitcoin nodes.
The Bitcoin (BTC) network has been steadily recovering in terms of running BTC nodes after a major outage on the Tor network.
According to the latest data from node monitoring resource Bitnodes, Tor-enabled Bitcoin (BTC) nodes are back to normal following almost a full-swing crash in early January 2021. As of Jan. 13, the number of reachable Tor-based BTC nodes amounted to 2,581, up from as few as 122 nodes on Jan. 9.
Based on Bitnodes data, Tor-enabled Bitcoin nodes make up a significant part of the Bitcoin network, normally accounting for about 25% of totally reachable running nodes. According to the latest recorded data, Tor-based nodes made up over 23% of total BTC nodes on Jan. 13.
According to Bitnodes, the current number of Bitcoin nodes amounts to 11,190 nodes, up from around 8,300 on Jan. 7.
A Bitcoin node is a computer connected to other computers to host and synchronize a copy of the entire Bitcoin blockchain and essentially keep the entire network running. Tor-based Bitcoin nodes are a type of node implemented privately using the Tor anonymous network.
The latest dip in Tor-enabled BTC nodes is likely to be caused by a recent crash on the Tor network. On Jan. 10, Tor Project officially announced that the Tor network was experiencing instability due to an implementation bug in its v3 onion service. Tech-focused news agency TechNadu reported that the outage was likely due to a hacker attack.
The downtimes in the Tor network subsequently affected a large number of Tor-enabled or so-called “onion” websites including private Bitcoin wallets and exchanges like Wasabi and Bisq. On Jan. 11, Wasabi reported that it managed to keep its services intact using a fallback system. “If the Tor onion service of the backend becomes unavailable for the user, the wallet falls back to communicating with the backend’s clearnet endpoint, still over Tor,” Wasabi wrote.
A spokesperson for Tor Project told Cointelegraph that there is no evidence that the Tor Network was under an attack but was rather triggered by traffic overload. “The outage may have come from a poorly written custom Tor client requesting directory information too often,” the person said. There is also no evidence that the traffic overload was actively trying to hurt v2 onions, the representative noted.
According to the spokesperson, the network “was always fully intact” but the traffic overload “destabilized v3 onions” due to a bug. As a result, v3 onion services were inconsistently reachable for a few hours on Jan. 9 and again for a few hours on Jan. 10, the person stated. A fix for the underlying bug is now in an alpha release on the Tor Project website.
Updated: 2-3-2021
Taproot Update: Bitcoin Users Home In on Activation Plan
The meeting ended with rough consensus in favor of BIP8 (false), as well as with approval of two possible methods to put this BIP into motion.
Many of Bitcoin’s most active stakeholders have just about nailed down the activation method for Taproot, the Bitcoin software’s biggest upgrade in years.
In a public meeting on Internet Relay Chat (IRC) Tuesday, Bitcoin developers, miners, business professionals and enthusiasts hashed out the specifics of how to package the Taproot upgrade into an update – and how to activate it once the code has been shipped.
The most active of the 200 or so participants on the chat (mostly, but not all, developers) seemed to agree on the Bitcoin Improvement Proposal (BIP) that would be used to activate Taproot. To prep the BIP for shipment, they also voted to “merge” two “pull requests” (PRs) on GitHub that outline the rules for Taproot’s activation logic into Bitcoin’s source code when the time comes to push the upgrade.
One of these, PR #1021, includes a measure to allow users to force activate the upgrade should miners not support it, while PR #1020 only “recommends” this forcing but does not enable it by default.
Since most all participants support BIP 8 without forced activation, as meeting leader and Bitcoin Core developer Michael Folkson noted in the chat, further discussion will pinpoint a date to begin activation – and further discuss the extent to which a “flag day” to force activation is necessary.
Why A Taproot Flag Day (Probably) Isn’t Needed
Not that miners blocking the upgrade should be an issue for Taproot, which has some 91% miner support, according to a survey run by F2Pool VP Alejandro De La Torre.
The survey provides crucial feedback from miners for Bitcoin’s decentralized organization, which cannot unilaterally coordinate updates the way a centralized software provider can.
Upgrades like Taproot require painstaking coordination between miners, full-node users (those running Bitcoin’s open-source code) and other stakeholders to ensure nothing goes wrong (like introducing a bug or splitting the Bitcoin network into two incompatible versions).
Because miners have shown no resistance to Taproot, most participants voiced a preference for BIP8 (false), with the (false) referring to the exclusion of a “flag day” to force activation through full nodes should the upgrade fail through lack of miner activation.
BIP8 as currently devised would give Bitcoin miners and full-node operators a year to adopt the upgrade, after which point the upgrade would be “locked in” with enough support. In one version of this, BIP8 (false), the update simply fails without enough support. In another, BIP8 (true), a “flag day” would force miners to signal for the upgrade when the activation time frame expires if they did not do so beforehand.
Technical note: There are a few ways to upgrade Bitcoin, the easiest being through miner activation where mining pools upgrade and begin mining blocks under the new rules. Failing this, node operators can upgrade and choose to reject blocks from miners who have not signaled support for an upgrade.
This so-called “user activate soft fork” (UASF), also used to activate SegWit, would force holdout miners to adopt the new upgrade.
“Completely anecdotal but I’ve not seen any [emphasis theirs] opposition to Taproot,” one willcl_ark said in the chat, referring to whether or not a flag day is necessary. “I think using the lowest common denominator of activation parameters (false) seems like the sensible choice to avoid any purposeful or accidental chain splits in the case miners don’t signal.”
What’s the holdup?
Still others, like prolific Bitcoin Core developer Luke Dashjr, are not convinced the inclusion of a flag day is unnecessary. In fact, it’s a matter of principle to demonstrate that node operators decide software, not miners.
“It doesn’t matter,” he said in the chat in reference to miner support. “Miners do not decide protocol changes,” he continued, intimating that it’s the node operators who decide instead by choosing what software to run.
Further, he espoused that BIP8 (false), “let[s] miners decide” the fate of the upgrade. When the time comes, he said later in the chat, he will configure his node to run the BIP8 (true) version that rejects non-Taproot blocks from miners.
“BIP8 with mandatory [activation] is not an unnecessary show of force,” said hsjoberg, reiterating Dashjr’s belief that the user-choice of a UASF is a necessary check and balance on miner apathy.
Still, a show of force could introduce unnecessary risk and set an unwelcome precedent for future upgrade deliberations, especially when miners have given users no reason to be combative, so go the arguments in favor of BIP8 (false).
“[BIP8 false] is safer than [true], so it’s worth doing [false] first given that we know hashpower is ~90% already pro-Taproot,” Bitcoin Core and CoinSwap developer Chris Belcher said.
Others like Suredbits and Bitcoin Core developer Ben Carman pointed out that you could configure the upgrade later on into activation to include the flag day should miners fail to signal, “making it safer and easy for users to enforce the UASF.”
At the end of the meeting, the participants agreed to merge pull requests on GitHub for both a non-forced activation route (PR #1020) and a forced activation route (PR #1021). With both of these rules in Bitcoin Core’s GitHub, the rules for a forced activation could be used only if necessary.
More Deliberation
The chain split scenario that willcl_ark described is basically the bogeyman everyone wants to avoid here. The fear is that BIP8 (true) requires 100% of hashrate to signal for the upgrade after the Taproot activation deadline ends.
Thus, if enough users went this route at the same time that others use BIP8 (false) for non-forced activation (which only requires 95% of hashrate), the two different code versions may create two incompatible histories of Bitcoin’s transaction ledger.
That’s why, if forced signalling must happen at all, it’s best to do so through AJ Townes’ PR #1021, which “makes it safer for the UASF option which is the most ‘dangerous’ scenario,” Carman wrote in the chat.
For now it seems as if those involved in discussions favor BIP8 (false) with the addition of a UASF through PR #1021 if needed, but further discussion is needed to hammer out the exact timeline of the initial activation period (or how long users have to upgrade after the update goes live), as well as what activation date to set.
These “what ifs” and “whens” will be hashed out, among other matters, in a meeting next Wednesday.
How Bitcoin’s Taproot Upgrade Will Improve Technology Across Bitcoin’s Software Stack
Scaling, privacy and custody software will all benefit from Bitcoin’s biggest upgrade in years.
Bitcoin’s Taproot upgrade is (basically) a shoe-in as Bitcoin stakeholders figure out the best way to bring it online.
Digital signatures are created from the private keys that control bitcoin wallets and are required to approve transactions. Taproot addresses will use Schnorr signatures, rather than Bitcoin’s current signature algorithm, the elliptic curve digital signature algorithm, or ECDSA for short.
In terms of data and processing, Schnorr signatures are smaller and faster than ECDSA signatures and also have the added benefit of being “linear,” which means Schnorr-based smart contracts can be optimized for functions that ECDSA signatures cannot.
These differences have made Taproot a highly anticipated upgrade because it will give Bitcoin a boost to transaction privacy and allow for more lightweight and complex “smart contracts” (an encoded contract with self-executing rules).
he tooling and coding improvements Taproot brings will be largely under the hood and will be a boon to developers. Regular Bitcoin users, however, will also benefit from usability, performance, and privacy improvements to multisignature (multisig) technology, privacy software and even scaling tech like the Lightning Network.
Without Taproot, applying the following upgrades to these softwares would either not be possible or not be as viable.
MuSig2: Boosting Privacy And Efficiency Of Multisig Transactions
Bitcoin development hub Blockstream is developing a new multisig software, MuSig2, which will make multisig transactions more efficient, cheaper and more private.
Unlike usual Bitcoin wallets, which only require a single signature from a private key, multisig wallets require at least two or more signatures from different private keys to approve a transaction. The idea is to distribute the risk of a wallet among multiple keys and, if needed, multiple parties.
Under the current design with ECDSA contracts, multisig transactions record the signature of each multisig participant individually.
Schnorr signatures would allow each signature to be recorded as one signature on the blockchain, making the transactions more lightweight in data, and thus cheaper.
“[Taproot] benefits multisig wallets such as Blockstream Green because using MuSig2 is cheaper and more private than current multisig setups,” Blockstream researcher and applied cryptographer Jonas Nick told CoinDesk.
The Bitcoin upgrade will also raise the limit on signers a multisig wallet allows from 15 to a “much higher number,” said Bitcoin developer Chris Belcher.
Schnorr-signature based transactions are more private because, thanks to so-called scriptless scripts, all Taproot transactions have the same digital footprint. That means a single signature transaction and a multisig transaction look the same on the blockchain under Taproot’s rules.
This privacy improvement spills over into other areas of Bitcoin’s development, too.
“MuSig2 also improves efficiency of multi-party contracts such as Lightning Channels, CoinSwaps or discrete log contracts, and improves the privacy of routing in the Lightning Network by enabling ‘scriptless scripts.’ This also means that the anonymity set of regular transactions would become larger because, for a blockchain observer, it could just as well be part of a multi-party contract or multisig wallet,” Nick said.
CoinSwap: Disguising Mixed Coin Transactions
All of the softwares Nick referenced rely on multisig wallets to bind market participants in cryptographically reinforced rules of engagement called smart contracts.
One of these, the privacy protocol CoinSwap, is widely considered to be the best successor to CoinJoin, currently the most popular software for “mixing” bitcoins to obscure their transaction history.
One shortcoming of CoinSwap’s precursors including CoinJoin is such transactions show up as distinctly different from normal ones. This makes it easier for blockchain analysis to pinpoint CoinJoins on-chain, thwarting any privacy benefits.
According To Belcher, Bitcoin’s Taproot Upgrade Will Fix This Problem.
“A good benefit of Taproot is also that it allows scriptless scripts. As you may know, protocols like Lightning Network and CoinSwap depend on so-called hash time locked contracts. Currently these contracts are visible on the blockchain. The thing that scriptless scripts allows is for those contracts to also look exactly the same as a Taproot single-sig transaction.”
Point Time Lock Contracts: Making Lightning More Private
As Belcher points out, Bitcoin’s Lightning Network uses hash time locked contracts (HTLCs) to facilitate transactions. But Schnorr Signatures would pave the way for point time lock contracts (PTLCs), an improvement on HTLCs that allow for more private and efficient smart contracts for Lightning.
The privacy gain comes from a modification to how Lightning Network nodes “route” transactions. Lightning transactions must be sent directly and peer-to-peer on what are called “payment channels.” Otherwise, lacking this direct connection, payments must be routed through peers to which both the sender and receiver are connected.
Lightning Network nodes route transactions by passing on a hash of the payment to each node on that payment’s path. PTLCs alter this hash by adding random info at each hop to make the payment less traceable to any party conducting blockchain surveillance.
Additionally, PTLCs will enable more complex smart contract logic to facilitate unprecedented blockchain escrow conditions and to improve oracles. (Since a blockchain can’t process data outside of its network, an oracle feeds this data to it.)
“Technically, [PTLCs] could be done today with ECDSA but it doesn’t have the same proven security, and if it was implemented it would have to be redone once we get Taproot,” Ben Carman, a developer at Suredbits, told CoinDesk.
Other Taproot improvements
Carman and his colleagues at Suredbits have been working on discrete log contracts (DLCs), a fairly new smart contract logic for Bitcoin that, while working today, will be more flexible and easier to use when Bitcoin’s Taproot upgrade kicks in.
Belcher told CoinDesk that Schnorr signatures will also enable “batched validation” wherein a Bitcoin full node could “validate 1,000 Taproot signatures in nearly the same time it takes to validate one [ECDSA] signature.” This scaling solution would significantly speed the time it takes a node to verify all signatures in a block.
Additionally, Taproot could use “ring signatures” to give users the ability to prove they own certain coins without having to reveal the public key associated with those coins.
“That means someone could prove that they own a certain coin without revealing which exact coin. For example, it would be possible to prove you own at least 1 BTC (or any amount) by doing a ring signature over all the Taproot [unspent transactions] worth more than 1 BTC, and yet it doesn’t actually reveal which is yours,” Belcher said.
This has implications particularly for Lightning Network node operators who want to prove payment channel ownership without sacrificing privacy.
Updated: 2-17-2021
Bitcoin Taproot Upgrade Nailed Down For July, But Some Finer Details Still Aren’t Finalized
The finalized code for Taproot will be shipped in March, but will it house the “user activated soft fork” feature that threatened to activate SegWit?
A release date and activation timeline are set for Bitcoin’s Taproot upgrade, but developers and other stakeholders are still debating the best method to coordinate Bitcoin’s biggest upgrade since SegWit.
Per a public IRC chat discussion, the code for the fully primed-and-ready Taproot upgrade will be deployed sometime between March 17 and March 31 (or April if necessary), but the actual signaling that kick-starts the activation process probably won’t start until July.
If everything goes as planned, then Bitcoin’s “economic majority” (miners and node operators who run Bitcoin’s code) could update within two weeks of the signaling period’s start. Come August 2022, Taproot’s activation period will reach its timeoutheight and signaling will end.
Assuming mining pools reflecting 90%+ of Bitcoin’s hashrate support Taproot before the timeoutheight (as one survey indicates), then the vast majority of support would ensure Taproot is a success, and the other 10% or so (the “economic minority”) can update without consequence afterward.
But what happens if the mining pools don’t signal to activate Taproot? Well, that’s where the hang-up is in discussion right now. But for some of Bitcoin’s stakeholders the hang-up shouldn’t even exist.
True Or False?
First, a quick note about Bitcoin upgrades.
Unlike a centralized network, whose central operators can mandate an upgrade whenever and however they choose, Bitcoin’s network is decentralized, so upgrades require deliberate decision-making and discussion among Bitcoin’s stakeholders (namely, developers, miners, business and power users).
Taproot is a “soft fork,” meaning a change that is compatible with previous versions of the software (unlike a “hard fork,” where newer rule-sets and older rule-sets are incompatible).
Soft fork or not, at the heart of the matter for activating Taproot is whether to give node operators (those individuals running Bitcoin’s source code) an option to force activate the upgrade if a supermajority of miners fail to support it before the timeout.
This would allow node operators to reject blocks from miners who don’t support the upgrade. This sort of measure (a so-called “user-activated soft fork”) was used to prod along the SegWit upgrade activation in 2017 and is believed to have budged the Overton window for miners to accept the upgrade.
The other option is to not include this feature at all. These Bitcoin Improvement Proposal (BIP) options to force or not force the upgrade are referred to respectively as BIP8 (true) and BIP8 (false), also known as LOT=true and LOT=false.
LOT is short for lockinontime, a feature that dictates whether Taproot will be “locked in” if network-wide activation isn’t reached when the timeoutheight is reached; the (true) option automatically mandates the upgrade after the activation window expires, while (false) lets it fail entirely.
Opponents of BIP8 (true) say this aggressive measure is gratuitous because Taproot isn’t at risk of failing. As Bitcoin Core contributor Andrew Chow put it, with the Taproot activation survey sent to miners, “the community has already decided to activate, [so] there’s no need to [do] LOT=true. Miners are part of the community.”
Could Taproot Activation Cause A Bitcoin Chain Split?
Still others in favor of BIP8 (true) believe it is a necessary feature for coordinating the upgrade, which in the rarer circumstance of extreme discoordination, could split the Bitcoin network into incompatible versions if something goes wrong.
“LOT=true does not split the chain. It strictly reduces the likelihood of that,” BIP8 (true) primary proponent Luke Dashjr said in the chat.
Dashjr shares this view with others, like hsjoberg, who noted, “Lot=true would make sure upgraded nodes mandate a specific chain.” This means that node operators who run true would mandate that the Taproot-activated version of Bitcoin is the “real” chain, so theoretically this would help coordinate consensus between actors to avoid a split.
One brg444 contended that “if lot=true activates there will be a network split.” But this would only be if the forced activation went through. Brg444 said they think this is unlikely, because the threat of this very split would be enough to scare miners into activating before the forced activation occurs.
The Ghost Of SegWit Past
But Is A Scare Tactic Really Necessary Or Is It An Egregious Show Of Force?
“[In my opinion, people] have PTSD from SegWit … [they’re] being preemptively defensive for seemingly no reason other than they’re afraid of past events that now seem to have a low probability of actually occurring,” Lightning Labs CTO Olaoluwa Osuntokun said in the chat, referring to miners originally opposing the activation of SegWit.
“[P]pl are just shadow boxing casper rn lol,” he said later. “Let’s give [BIP8 (false)] a shot and revise afterwards if stuff actually happens.”
After all, if six months or so after activation begins miners haven’t signaled for Taproot, then LOT=true could be coded in after the fact to enforce the upgrade.
Still, this would add yet another step to the process, and making this change post-factum would be more cumbersome than just including it in the initial release. But some think it’s a more prudent decision, especially considering the stigma that brands Bitcoin development as a closed garden that is subject to the tending of developers only.
“LOT=true appears as if the developers are forcing a change upon the community. While that may not necessarily be the case, the appearance of that happening is not a good thing. Given that we don’t believe there will be any issues with activation, I would prefer LOT=false to avoid this view,” Chow said.
A Question Of Coordination
Notably, the last meeting to discuss Taproot seemed to indicate majority support for LOT=false. With only 100 or so attendees this round (as opposed to nearly double the attendance last time), and some favor growing for LOT=true, though, “we can’t really measure ‘community consensus,’” contributor Darosoir said.
According to the Taproot activation wiki, 26 attendees in yesterday’s meeting vocally favored LOT=false while 19 favored LOT=true (some more neutral parties indicated they would be fine with either).
Hardly representative of Bitcoin’s sprawling international community, the IRC chatters left the meeting without clear consensus on the precise activation parameters, with some voicing the need to boil down the complexities of the process to get a more informed opinion from the wider community.
“I will say, though, that I think this discussion would have benefitted from having a more clear view of the community overwhelmingly supporting this. Off topic for this meeting, but anyone interested in how to get better data around this, I’d be interested to work with,” Keagan McClelland, co-founder of Start9 Labs, wrote in the chat.
With a date set for the end of March and the bulk of the activation parameters chosen in BIP8, the final question to answer for Taproot’s deployment is whether or not to include the “user activated soft fork” measure from the get-go or not.
Taproot will ship by BIP8 in late March and activation is slated for July, so this question will have to be answered within the month.
Updated: 2-26-2021
Crypto Leaders Back MIT’s Four-Year Initiative To Harden Bitcoin’s Security
Crypto industry captains are throwing their support behind a long-term project from MIT’s Digital Currency Initiative to enhance Bitcoin’s security.
The Massachusetts Institute of Technology’s Digital Currency Initiative has revealed a new “Bitcoin Software and Security Effort” intended to foster research into bolstering the Bitcoin network’s defenses.
The open-source initiative has received support from a diverse group of crypto industry leaders, including Gemini’s Cameron and Tyler Winklevoss, MicroStrategy’s CEO Michael Saylor, Square CEO Jack Dorsey, and major European digital asset manager, CoinShares.
In a blog post unveiling the project, DCI said that Bitcoin’s ascent from an “obscure cryptographic toy” to a robust network that “secures on the order of $1 [trillion] of value” was due to the millions of hours invested into building the project by open-source developers.
Coinshares announced a $500,000 donation to the project and chief executive Jean-Marie Mognetti hinted that perhaps other crypto companies should do likewise:
“As a beneficiary of the work of hundreds of developers who secure, upgrade, and maintain the open-source protocols that underlie the Bitcoin network and the applications built on top of it, we believe for-profit firms in the digital asset industry have an obligation to fund independent, neutral development efforts and research that advances the mutual interest of all ecosystem participants.”
The DCI’s four-year research and development program aims to “harden the Bitcoin network and steward the industry’s commitment to funding open-source software.”
The blog post noted that, “The objective of DCI’s new program is to contribute neutral, expert resources to improving the robustness of the Bitcoin protocol. Bitcoin’s security is foundational to the underlying technology’s continued evolution, as well as the broad realization of the public-good promises of digital currencies.”
The post listed several key issues that MIT is exploring, including sustaining a senior team of Bitcoin developers, exploring new programming languages, and pre-emptive investigations against possible attacks,
MIT also stressed the need for the network’s security to grow and strengthen alongside increasing adoption, noting the challenge associated with coordinating a decentralized network:
“Unlike traditional assets, Bitcoin is software running on a decentralized network. Bitcoin’s security is predicated on the accuracy and robustness of the software and hardware running it, and the actions of those participating in the network.”
In July 2020, DCI researcher James Lovejoy warned that attempted 51% attacks — attempts to capture a majority share of nodes and thus control over the Bitcoin network — may be more plausible than previously thought.
Lovejoy stressed the need for active blockchain monitoring in order to identify 51% attacks targeting proof-of-work blockchains, stating: “You need an active observer to be monitoring the network to check whether or not an attack occurs.”
“Up until now we’ve been reliant on victims to tell us about whether they’ve been attacked. As you can imagine, if this results in insolvency or a loss of user funds, victims are often not super interested in revealing when an attack has taken place,” he added.
Updated: 7-9-2021
Bitcoin’s Taproot Activation Gains Momentum From New ‘Speedy Trial’ Proposal
Taproot is the largest upgrade Bitcoin has seen in years, and many are proposing projects on top of it.
Bitcoin developers have been debating the best way to activate the Taproot upgrade for at least a year. Some are hopeful a new proposal called “Speedy Trial” might put an end to the debate, by bringing forth a solution that more developers can get behind.
Ideated by Blockstream developer Russell O’Connor and written up on the Bitcoin developer email list by technical Bitcoin writer David Harding, “Speedy Trial,” would take a quicker approach than some of the other proposals in determining if miners are ready for activation of Taproot. All of the largest mining pools have already indicatedthey plan to upgrade.
“The idea received significant discussion and seemed acceptable to several people who could not previously agree on a proposal (although this doesn’t necessarily make it their first choice),” Harding wrote on the email list.
Taproot is the largest upgrade Bitcoin has seen in years, and many are proposing projects on top of it. It will boost privacy and scalability, and will bring a variety of other technical benefits.
Tentative Taproot Agreement
Consensus for changes to Bitcoin is hard because people from all over the world contribute to it and have different opinions about how things should work. But so far it seems like “Speedy Trial” is getting a fair amount of support.
“Seems almost everyone is on board,” developer Ben Carman tweeted.
Looking through the comments on GitHub, 100% of developers so far have responded with “ACK,” which indicates support for the proposal. Meanwhile, Bitcoin developer AJ Towns has already coded up a draft version of the activation proposal, which similarly has a long train of ACKs.
That said, it takes time to build consensus over such a consequential proposal. CoinDesk messaged several Bitcoin developers who have not yet voiced an opinion. Most said they had not yet had time to read the proposal. Another said he did not have an opinion yet.
‘Quickly Succeed’ Or ‘Quickly Fail’
The change itself, Taproot, isn’t being debated at all. Rather, developers are debating the best way to push through the change. No CTO or central leader is in charge of the network to impose new rules. Instead, a sizable portion of the global network needs to be prepared for the new Taproot rules.
If they aren’t prepared or if not all miners upgraded to the new software in time, there’s a chance the network could split into two.
Developers have different ideas of how to deal with this dangerous possibility. The above article goes into much more detail about the history of this debate and its potential consequences.
Speedy Trial would give miners a chance to flag if they’re ready or not – but would do so on a shorter time line than other proposals. Rather than giving miners a year to flag support as once proposed, which opponents argue is too much time, Speedy Trial gives miners three months. Another key part of the proposal is that after this three-month lock-in, there’s a waiting period of six more months before Taproot will activate.
“The goal of Speedy Trial is to allow a Taproot activation attempt to either quickly succeed or quickly fail – without compromising safety in either case,” Harding writes.
Beyond that, the proposal shares a lot of similarities with other proposals. If 90% of Bitcoin blocks in a window of time flag readiness, this should show that roughly 90% of miners are ready. At this point, the change will be locked in.
If this 90% lock-in threshold isn’t reached in three months, however, activation fails.
“There is no mandatory activation and everyone is encouraged to try again using different activation parameters,” Harding writes. At this point, users would need to come up with a new plan.
Updated: 3-18-2021
‘Speedy Trial’ Taproot Activation on Bitcoin Could Still Include A Safety Net
Speedy Trial is nearly approved for activating Taproot, but the code may still include a “user activated soft fork” safety net, just in case.
Taproot – Bitcoin’s most anticipated upgrade ever – has been “close” for a year now, but no one in Bitcoin’s community has agreed on how to activate it. With Speedy Trial, there might finally be a solution, though it may still involve a “user-activated soft fork” (UASF).
In a public meeting on Tuesday on Internet Relay Chat, Bitcoin stakeholders more or less agreed on the recently proposed Speedy Trial method, saying activation could begin this April or May (a month or so later than anticipated, when prior activation methods were on the table). There were no serious objections to the proposal in the meeting.
With Speedy Trial (more or less) receiving widespread support, the Bitcoin community is nearing the conclusion of a saga that began years ago. Assuming all goes as planned and Speedy Trial is a success, Taproot could be live on Bitcoin’s blockchain in November of this year.
And if it fails? Well, then the Bitcoin community learns new lessons about consensus. And it also means it could be back to square one with a “user-activated soft fork” as an inevitable activation method.
What Is Taproot?
Taproot will outfit Bitcoin with Schnorr signatures, a signature scheme which Bitcoin could have used from day one and which will give a boost to Bitcoin’s privacy, custody and scaling softwares.
Unlike SegWit, Bitcoin’s last big upgrade, there’s no opposition to Taproot. But even as the upgrade itself isn’t up for debate, the way to bring Taproot online has been the subject of some very heated debate.
That’s because unlike a centralized network or service, where one person or group of people can dictate upgrades unilaterally, Bitcoin has no central authority. Upgrades are debated painstakingly among hundreds if not thousands of stakeholders across social channels.
Even when an upgrade is a so-called “soft fork” like Taproot, meaning it is compatible between older and newer software, the implementation is treated with care. So if consensus on a Taproot activation route isn’t clear, it’s hard to move forward with an upgrade without sufficient support.
What Is Speedy Trial?
Such was the case with the so-called lockedintimeout or “LOT” debate.
Essentially, the community could not decide whether or not Taproot should fail if miners don’t adopt it, or whether or not the activation should include code for a “user-activated soft fork,” wherein node operators force activate Taproot by blacklisting blocks which don’t support the upgrade’s code (a similar “user-activated soft fork” scenario played a role in activating SegWit).
Bitcoin developer Russell O’Connor proposed Speedy Trial to break the deadlock and provide a fast trial-by-fire to see whether or not miners would upgrade quickly (and thus, whether a UASF is even necessary).
Under Speedy Trial, miners would have three months to signal support for Taproot after its code is shipped through Bitcoin Core, Bitcoin’s primary software version. If 90% of the blocks in a given time frame are not Taproot-supporting, then that means miners don’t support the upgrade and activation fails.
If the threshold is reached, then activation takes place after a six-month “locked-in” period. During this time frame, the upgrade is in the bag, but its actual activation is delayed to make sure there are no hiccups.
(One potential hiccup: Miners don’t actually have to upgrade to Taproot during the signaling period; they only need to signal their support, and they do so by including a unique bit of code in the blocks they mine. Thus, the delay partly exists so miners have ample time between signaling and activation to upgrade their nodes).
The code that would put Speedy Trial into motion could come either from Bitcoin Improvement Proposal 9 (BIP9), the code for which already exists, or through BIP8, which would need to be coded.
Running In Circles?
“We’re basically where we were a few weeks ago, but with more data,” Bitcoin developer Sjors Provost expressed on a Van Wirdum Sjorsnado podcast on Speedy Trial.
Indeed, this approach is a truncated version, in a way, of the LOT=False proposal that was previously debated alongside LOT=True.
Should Speedy Trial fail, it would resemble LOT=False in that nothing happens. This would also likely pave the way for a LOT=True scenario, some community members pointed out in a Tuesday Taproot Activation discussion.
“If Speedy Trial fails I think a UASF release is inevitable,” user Shesek said.
“Users would be advised to expect a followup ‘real’ deployment in the event this isn’t signalled,” Bitcoin developer Luke Dashjr said in the chat, with “real” meaning an activation by node operators through LOT=True or UASF. The prolific developer is of the opinion that Speedy Trial will fail because the timeline is too short and because miners may not activate even after they signal.
Putting To Bed Or ‘Punting’ The Problem?
In some respects, Speedy Trial is a consolation activation. It’s nobody’s first choice but people still support it because it may offer an end to what has become a tiring, dragged-out discussion over an upgrade that makes changes to a couple of lines of Bitcoin’s code (yes, really).
Blockstream and Bitcoin developer Rusty Russell likened Speedy Trial to “punting” the problem (namely, smooth soft fork activation coordination) down the field to deal with another day.
“I understand people are tired, and nobody wants conflict,” he said in the chat, while clarifying later his position that he believes Speedy Trial is “a terrible idea.”
According to Russell, it’s a terrible idea because it sets a precedent that the fastest and most effective way to an upgrade should win out, not one which makes node operators the final arbiters for choosing a change to Bitcoin’s software.
This arbiter role, Russell and those like him argue, was the key takeaway from the SegWit saga and one of Bitcoin’s most effective checks for users against powerful interests.
That’s why proponents of this line of thinking want code for some form of UASF included with the Speedy Trial release from the get-go.
If Speedy Trial fails, then activation would lean on a BIP8-style user-activated soft fork – a proposal that was previously discussed but which had no consensus, thus prompting Speedy Trial.
This activation method would take place after Speedy Trial and would include a year-long (or 15-month) signaling period, after which time Taproot would automatically activate on user nodes through the UASF. (This scenario would have Taproot activating in 2022 or, at the latest, 2023).
Still, Speedy Trial has to fail for this backup to take effect, and it appears as though stakeholders are on board with trying Speedy Trial first.
Yet another meeting will be held next week that could finally put the matter to bed.
Updated: 3-24-2021
New Taproot Activation Timeline Means The Upgrade Is (Probably) Coming To Bitcoin This Fall
If the timeline holds, Taproot’s November activation could make for an exciting autumn for bitcoiners.
Bitcoin’s developers and community members seem to have finally settled on a timeline to activate Taproot, Bitcoin’s biggest upgrade since SegWit in 2017.
Per notes from a public Internet Relay Chat (IRC) meeting, the code for Taproot could be ready for users to active in the Bitcoin Core client via “Speedy Trial” in May of this year. If Speedy Trial is successful, this would mean the upgrade could be online in November.
“There is broad agreement that we should target something like a May 1st release, with [a 1 week signalling start time afterwards],” Bitcoin Core contributor Jeremy Rubin wrote in meeting notes. If successful, this would mean an “activation time of around Nov 15th,” he notes.
Speedy Trial allots a three-month trial period to see if miners representing at least 90% of Bitcoin’s hashrate will signal their support for the upgrade. If this threshold is reached, then Speedy Trial is successful and the upgrade will be “locked in” three months after the beginning of signaling. After this, Taproot’s rules would be officially enforced in another three months.
(If, for example, signaling were to begin on May 7 and miners showed sufficient support, then Taproot would be locked in on Aug. 7 and go live on Nov. 15. The later the signaling begins, the later the activation.) New code in Bitcoin Improvement Proposal 8 (BIP8) will set the parameters for the Taproot activation, which will judge when to lock in the upgrade based on block height.
As stakeholders appear to be in agreement on the timeline, bitcoiners finally have a (more or less) concrete deadline for when they can expect Taproot’s code to be available to the public to download, marking an end to what has become a painstaking road to a relatively simple upgrade.
Taproot Activation’s And The Long Road To Consensus
There is still the caveat that May 7 may not be the exact start date of Taproot’s activation, but it will likely be somewhere around that time.
As ever in Bitcoin’s development, upgrade parameters are in constant flux because no single person or organization has final say over how development should proceed. It’s up to Bitcoin’s distributed, international community to come to a consensus on what changes to make to Bitcoin and, just as important as evidenced by the Taproot activation discussion, how those changes will be brought online.
Take the so-called user-activated soft fork (UASF) that was so hotly debated during the Taproot activation discussions. This would give node operators the option to force-activate Taproot should miners fail to update their own nodes with the upgrade by rejecting blocks from noncompliant miners.
Miners have given no indication, though, that they will reject Taproot, and the UASF proposal lacked enough support to make its way into Bitcoin Core, the software implementation that 99% of the Bitcoin network runs.
Still, Luke Dashjr and others are coding a UASF that anyone can opt into (but which won’t be included into Bitcoin Core) in case Speedy Trial fails. If Speedy Trial were to fail, then nothing would happen and Taproot would simply fail to activate. Under this scenario, a UASF could be deployed, probably next year, to bring the upgrade online.
This is largely unlikely, however, given broad miner support for the uncontroversial upgrade.
Updated: 4-12-2021
Final Taproot Activation Specifics Chosen With A Bitcoin Blockchain ‘Coin Toss’
The coin toss is a stand-in for the rough consensus that stakeholders usually broker to make these decisions.
Bitcoin developers couldn’t settle on the specifics of Taproot’s activation, so they used a “coin toss” on the Bitcoin blockchain this Tuesday to wrap up activation discussions that began a year ago.
According to blockchain data pulled from this journalist’s Bitcoin node, the result of the coin toss has determined that Taproot’s activation timeline will be measured using median time passed (MTP) instead of block height.
For the actual “toss,” the last digit of the block 678079’s hash were used to decide the outcome where a value of 0 represented MTP and a value of 1 represented height.
Taproot – an upgrade that will enrich Bitcoin’s smart contracts – is all set to go using the “Speedy Trial” activation method outlined a month ago. Today’s coin toss settled a dispute, though, over how the Bitcoin blockchain will measure the time that has passed between when the upgrade is released and when it will “time-out.”
Block Height vs. MTP
There were two options up for debate: one using “block height,” which chooses a timeout that triggers once a specific block is mined and the other using MTP, which chooses the timeout based on real-world time derived from block data.
The coin toss occurred on block 678079 and the result landed on MTP. Following the result, Bitcoin Core contributor Andrew Chow removed his pull request for a block height-based scheme.
MTP means that when Taproot’s code is shipped, miners and node operators will have a time period of exactly three months to upgrade to Taproot before a timeout period is reached.
If miners representing 90% of Bitcoin’s hashrate upgrade in this timeframe, then Taproot is “locked in” and it will activate three months after this lock-in. Assuming Taproot is shipped by May, this means the upgrade would be fully functional on the Bitcoin blockchain no later than November.
“We have two good options, and coin flip is people agreeing to put aside minute preferences on two acceptable options for the big picture,” Bitcoin Core contributor Jeremy Rubin wrote in a Bitcoin devlist email. “As such, I think that a coin flip is appropriately used in this circumstance, although I recognize the sentiment that some may feel it’s treating development a little too *flippantly*.”
Updated: 5-2-2021
What Are Bitcoin Mixers, And Why Do Exchanges Ban Them?
Bitcoin transactions are easy to trace, except when the sender uses a mixer to muddle the link between their crypto address and real-life identity.
One of the original allures of cryptocurrency is the narrative that using them provides the sender or recipient anonymously, but this is a common misconception within the sector.
In reality, Bitcoin (BTC) and many other cryptocurrencies are easily traceable.
Proof of this came earlier this week when on April 27, U.S. authorities arrested the mastermind of Bitcoin Fog, a darknet-based BTC mixing service. Authorities were able to capture the operator after analyzing ten years of blockchain data.
One doesn’t need to be a forensic analyst to know that every single transaction is tied up to addresses on the blockchain and that they will stay there forever. While government agencies cannot determine the IP address or personal data from the address, these coins usually end up being used for products or service payments. This is the trail that leads back to the sender and recipient.
In the case of Bitcoin Fog, law enforcement was able to identify server hosting expenses paid using digital currency. Bitcoin mixing services such as Bitcoin Fog allow users to mix their coins with other users, making it almost impossible to detect the destination addresses. This obfuscates the ties between the inputs and output addresses, providing a better level of privacy.
Mixing services are offered in a wide range of methods, including fully centralized solutions where trust is required, to Coinjoin mixers, which depend on a large group of users to self cooperate and act simultaneously. There’s even the possibility of trading on decentralized exchanges (DEX) to virtually eliminate any possible tracing.
Mixers Do Present A Few Risks
Centralized mixers offer the obvious single point of failure problem. Even if one trusts that the entity is using multisig addresses, if the service is willing to share its data or has been breached, their users will lose their privacy.
CoinJoin solved this problem by combining the inputs of multiple users into a single transaction. The service will then take those coins, craft them into a transaction, and have each participant sign before broadcasting it to the network.
These transactions are then merged into one, and each user gets the original quantity in return. However, no one can see the origin of those coins, not even the entity that merges the transaction.
Even though CoinJoin isn’t exactly untraceable, it provides plausible deniability, as no one can point out which entity owns each output. The larger the number of participants, the higher the degree of deniability.
Some cryptocurrency users also require anonymity for sending tokens to their wallets, and Wasabi Wallet has long been used for its embedded CoinJoin functionalities.
While its infrastructure is technically centralized, its design assures that the operators cannot deanonymize users or steal any funds. At the moment, the Wasabi wallet is only available for desktop solutions, so as is the case with anything in cryptocurrency, beware of clones!
A similar service is provided by Samourai wallet, which also offers a Chaumian CoinJoin mixing service, called Whirlpool. To achieve a full-privacy solution, users have to connect the Samourai wallet to their own full Bitcoin node. However, it does offer desktop and mobile versions.
Even though these mixing services aren’t illegal in most jurisdictions, some exchanges and services might refuse users linked to addresses associated with coin mixing activities.
As more people realize the importance of achieving a certain degree of privacy for self-protection, the fewer incentives companies will have to deny their clients to use mixers.
Updated: 5-4-2021
Almost Half Of Bitcoin Hash Rate Signaling For Taproot Activation
Major Bitcoin miners have begun signaling for Taproot activation that will improve scalability and privacy for the largest cryptocurrency by market capitalization.
The road to the Taproot upgrade finally coming in 2021 is already underway, with major Bitcoin (BTC) mining pools already signaling support.
According to data from Taproot.watch, a webpage created by Bitcoin developer Hampus Sjöberg, Taproot signaling now accounts for about 44% of the total Bitcoin hashing power as of the time of writing.
AntPool and F2Pool — the two largest Bitcoin mining pools by hash rate — are among the earliest supporters of the Taproot activation in the mining arena. Other pools in support are Foundry USA and Slush Pool, with the latter responsible for mining the first signaling block.
Based on Bitcoin’s consensus, Taproot activation will only go forward if 90% of all mined blocks include an activation signal within a difficulty adjustment window (2,016 blocks).
This consensus agreement must happen in one of the difficulty epochs between now and Aug. 11 to be locked in as a network upgrade for November. As previously reported by Cointelegraph, the current difficulty period began on May 1 after a 12% downward adjustment.
As of publishing time, only 97 signaling blocks have emerged in the current window. Meanwhile, miners responsible for 382 blocks have elected to not include a “signal bit.”
The “no votes” by these miners, which account for 19% of the 2,016 blocks in the current difficulty window, means that the Taproot activation cannot be locked in until at least the next difficulty epoch.
However, given the reported support by miners for Taproot, the activation — touted to be the most significant for Bitcoin in over four years — is expected to proceed without as much controversy as the Segregated Witness saga of 2016 and 2017.
Taproot as an upgrade to the Bitcoin protocol will reportedly enable users to mask additional spending conditions, which could have significant implications for Bitcoin’s smart contract capabilities.
The ability to hide additional spending conditions beyond the ones triggered by the transacting parties could also improve Bitcoin’s privacy.
Updated: 5-7-2021
Bitcoin’s Upcoming Taproot Upgrade And Why It Matters For The Network
The upcoming Taproot activation stands to potentially make the Bitcoin ecosystem more user-friendly as well as secure.
While a vast majority of crypto enthusiasts around the globe seem to be gushing about Ether (ETH) at the moment and how its upcoming London hard fork stands to push the premier altcoin’s value even higher, reports have recently surfaced that suggest Bitcoin’s much-awaited Taproot upgrade will go live also sometime by the end of this year.
In this regard, many Bitcoin (BTC) mining pools seem to already be signaling their support for the activation and as per data available on Taproot.watch, a website designed by core Bitcoin developer Hampus Sjöberg, Taproot signaling currently accounts for about 56% of BTC’s total hashing power.
It should be mentioned that two of the largest Bitcoin mining pools by hash rate — AntPool and F2Pool — have been major proponents for this upgrade from the very beginning. Even other relatively large mining operators, such as Foundry USA and Slush Pool, have also expressed their support for the activation.
What Exactly Is Taproot?
In its most basic sense, Taproot can be thought of as the latest step in Bitcoin’s evolutionary path because the upgrade seeks not only to enhance the overall usability of the network by making transactions cheaper, faster and easier to deploy but also eventually allow for the deployment of smart contracts.
Furthermore, Taproot also proposes significant privacy promises — i.e., it seeks to make all transactions look the same to everyone except the transacting parties. This potential camouflage-based framework seems as though it has been inspired by security-centric crypto offerings available in the market today, thus potentially moving Bitcoin closer to some privacy-focused coins, at least from a design standpoint.
On the subject, Antoni Trenchev, co-founder and managing partner at crypto lending platform Nexo, told Cointelegraph that the proposed Taproot update is proof of Bitcoin’s decentralized nature and that the network is always looking to improve and grow. He also believes that the upgrade serves as a reminder to investors that, unlike gold, Bitcoin is a dynamic store of value in every sense, adding:
“All these admittedly major improvements pave the way for even wider Bitcoin adoption and continued price appreciation. In all, Taproot is one of BTC’s most anticipated updates since the block size upgrade of 2018.”
Joel Edgerton, chief operating officer of cryptocurrency exchange bitFlyer USA, told Cointelegraph that even though most in the crypto community seem to be focused on Bitcoin’s price action at the moment, what they are overlooking is the fact that BTC’s underlying technology is what actually gives it its value, and Taproot is an important development, for several reasons:
“Firstly, it reduces transaction data size, which could lower transaction fees for complex transactions. Additionally, it increases privacy on multisig and time-locking wallets by making it difficult to distinguish them from simple, single-sign wallets while also allowing for increased wallet functionality by allowing developers to use vaulting logic.”
In Edgerton’s view, Taproot demonstrates the Bitcoin community’s maturity and how everyone seems to have learned valuable lessons from the Bitcoin upgrade wars of 2017 — i.e., it is of utmost importance to plan and implement upgrades via the use of a decentralized, community-based vote.
Back in 2017, Bitcoin underwent a hard-fork, resulting in the creation of a new cryptocurrency called Bitcoin Cash (BCH). Although the process was quite straightforward, the period leading up to the hard fork was full of strife, with many core community members clashing with one another.
A Technical Breakdown
On paper, Taproot is an elegant engineering solution that has been devised using proven cryptographic foundations that can help provide several evolutionary improvements to the Bitcoin protocol.
Lior Yaffe, CEO of blockchain software company firm Jelurida, pointed out to Cointelegraph that by combining Schnorr signatures and Merkelized Abstract Syntax Trees, or MAST, Taproot is able to convert the representation of complex Bitcoin transactions, such as multi-signature transactions and transactions used to set up a Lightning channel, to look just like a regular Bitcoin transaction when submitted on-chain.
In cryptography, a Schnorr signature is easily “provably fair” and is functionally superior to conventional logarithmic signatures, which are routinely faced with intractability-related issues. Similarly, MAST are unique digital offerings that allow for the deployment of various user-selected conditions that must be fulfilled in order for an encumbered number of Bitcoins to be spent.
Overall, this reduces storage and can indirectly lower fees for these transaction types. Also, in the long run, when its usage becomes widespread, Taproot may be able to significantly improve privacy for Lightning and multi-signature users. “From an ecosystem perspective, I view Taproot as an all-in attempt by the Bitcoin devs and community to finally make the Lighting network a mainstream payment platform,” Yaffe added.
How Will Taproot Affect BTC?
Another aspect of the proposed upgrade worth considering is whether or not Taproot will have any major effect on Bitcoin’s future price action. In this regard, Edgerton does not see the activation having any sort of short-term impact on Bitcoin’s value. He does believe, however, that the “under the hood” changes that will come as a result of this update will make the Bitcoin network way more functional and competitive.
Yaffe believes that in the long term, improving Lightning network adoption — i.e., by reducing transaction fees and settlement times — will keep Bitcoin and its ecosystem as a relevant internet era payment method, adding further:
“Given that the recent surge in Bitcoin price can be attributed more to its potential use as a store of value and to adoption by institutional investors, I don’t expect Taproot to have any meaningful short-term price impact.”
Lastly, Siddharth Menon, co-founder and chief operating officer of cryptocurrency exchange WazirX, told Cointelegraph that since 2010, the latest Taproot upgrade has been highly anticipated and stands to have a positive impact on the currency. “Slowly but steadily, this network gets better every day,” he added.
Other Important Aspects Of Taproot Worth Considering
Per Bitcoin’s community consensus, the aforementioned Taproot activation will only be given the green light if 90% of all mined blocks include an activation signal within a difficulty adjustment window (2,016 blocks). More specifically, the consensus agreement needs to take place during one of the difficulty epochs between now and Aug. 11 so that the network upgrade can go ahead as planned in November.
As of May 7, a total of 327 signaling blocks have emerged in the current window, while miners responsible for 610 blocks have chosen not to include a “signal bit.” The “no” votes issued by these miners currently account for 30% of the 2,016 blocks in the current difficulty window. Some pools that have so far voted against the activation include big names such as Poolin, Binance Pool, BTC.com, viaBTC and HuobiBTC.
Updated: 5-10-2021
Why Bitcoin’s Taproot Upgrade Matters
The most important impact for the investing market overall: It’s a reminder that Bitcoin is a technology.
You might have noticed some green squares floating around Twitter. Like the laser eyes, they are part of the insider signaling that creates a sense of cause and belonging. Unlike the laser eyes, they are not directly about the price – they signal support for the proposed Taproot upgrade for the Bitcoin network.
Why is this important? It’s not just the benefits the upgrade brings, which are significant. Taproot is important because it reminds us of what Bitcoin is.
The Good Stuff
Before We Dive Into Why This Matters, Let’s Look At Some Of The Main Benefits Of The Proposed Upgrade:
* Increased privacy: This does not refer to Bitcoin addresses or enhanced anonymity; it refers to types of transactions. Taproot will make complex transactions, such as those requiring multiple signatures or those with delayed release, indistinguishable from simple transactions in terms of on-chain footprint.
* Lower fees: The data size of complex Bitcoin transactions will be reduced, which will lead to lower transaction costs.
* More flexibility: A new type of signature will enhance smart contract functionality in Bitcoin, making it easier and cheaper for users to set more complicated conditions for a transaction.
* Lightning boost. Taproot will make transactions on the Lightning Network cheaper, more flexible and more private. The Lightning Network is a layer 2 solution that enables faster and more scalable payments that periodically anchor in aggregate form to the Bitcoin blockchain, offering eventual Bitcoin security while amplifying speed and potential throughput.
A Meaningful Step
With all of the above, Taproot is the most significant upgrade to the Bitcoin network since the block size increase of 2017. The relative infrequency of Bitcoin upgrades highlights one of its main features: It is robust.
Making any amendments to Bitcoin is hard. There is no one “in charge” who can decide what changes get pushed through. And achieving consensus among such a diverse and dispersed group of participants is a challenge, to say the least. That Taproot is more or less unanimously supported highlights what a big deal this upgrade is.
What has turned out to be contentious, however, is the method of the upgrade. In March, a compromise was reached in the form of a “Speedy Trial,” which gives miners a series of two-week blocks in which to signal support for Taproot.
This kicked off last Saturday, with the most recent difficulty adjustment. From that moment, Bitcoin miners had until the next difficulty adjustment (two weeks later) to signal support for the Taproot upgrade in their mined blocks. If 90% of processed blocks signaled support, the upgrade would get “locked in” for activation in November.
On Tuesday, however, it became apparent this signaling round wasn’t going to be successful. With almost 25% of the window’s blocks processed by around mid-day, 20% had not signaled support, so the 90% threshold was out of reach.
Updated: 5-27-2021
US Financial Surveillance Agency Wants To Know More About Privacy Tech
The agency is asking privacy focused companies to participate in a virtual event aimed at boosting its understanding of privacy tech.
The U.S. Financial Crimes Enforcement Network (FinCEN) wants to increase its understanding of how privacy technology works, including those governing certain blockchain protocols.
The agency is expected to host a virtual program on Sept. 9 and is inviting companies “developing solutions to privacy issues” to participate, according to a press release on Wednesday.
FinCEN said the event will focus on the role of “privacy-preserving principles” in developing technical solutions that increase innovation in financial services while countering the well-worn narrative of illicit activity and national security risks.
Those being asked to tag along to the agency’s “Innovation Hours Program” include Fintechs, Regtechs, venture capital firms and financial institutions.
Privacy solutions being targeted include cryptographic zero-knowledge proofs (ZKP) and homomorphic encryption. ZKP allows two parties to prove a value is true, such as x, without revealing the identity of either party.
Though the concept stems from the 1980s, its technology has been bootstrapped to certain blockchain projects and protocols, including those used by Zcash and Mina.
The agency is asking participants to demonstrate, in one-hour meetings, just how these types of solutions operate and how businesses use them. That includes ways in which the privacy solutions can be utilized for private and public sector efforts, per the release.
“We support responsible innovation,” said Michael Mosier, FinCEN’s newly appointed Acting Director, “especially that which promotes the resilience and safety of our financial system and the American people.”
Mosier, who worked at blockchain surveillance firm Chainalysis as chief technical counsel before his departure in 2020, will likely bring additional knowledge regarding blockchain privacy to the agency’s event.
Those interested should submit a request online before July 23 and provide relevant background information regarding their firm’s business and products, FinCEN said.
Updated: 6-7-2021
Bitcoin’s Taproot Update Shows How It’s Not Like Gold
When Bitcoin undergoes a technological shift, it’s a test of narratives that underpin the asset’s value.
Bitcoin’s strongest narrative is “digital gold.” Investors buy it not out of an expectation that it will behave like gold behaves in the market today, but that it will some day take on the historic importance that gold has held across cultures and ages.
My colleague George Kaloudis recently reminded me that there’s one important aspect in which bitcoin will never be like gold: In a vault or in the ground, gold will always be gold; bitcoin, however, is a technology, and a technology will be updated.
This quality is now on display with the Bitcoin network’s progress toward an update called Taproot. (Keep an eye out for George’s forthcoming in-depth report on Taproot at coindesk.com/research.)
Taproot is a bundle of several improvement proposals. Notable among them, it would add data efficiencies that could ease supply-side pressure in Bitcoin’s transaction-fee market. It also includes updates to multi-signature transactions, a Bitcoin feature that is significant for custodians and other organizations that take direct custody of bitcoin. In this column, I’ll focus on the latter.
Multi-signature addresses are a governance tool for organizations that directly custody bitcoin. Taproot includes updates designed to make multi-sigs easier to use, and to improve their privacy: a multi-signature Taproot transaction cannot be distinguished from other Taproot transactions.
This could be significant for organizations that require multi-signature transactions, but do not wish to advertise to the network that they are using them.
Bitcoin’s pseudonymity has made it a target for criticism that the network can be used for criminal purposes. Pseudonymity also provides security for legitimate operators. On the internet, nobody knows you’re a dog; on Bitcoin, nobody knows you’re a financial institution. For organizations using the Bitcoin network, privacy reduces the likelihood of cyberattack.
This chart, adapted for readability from txstats.com, shows just how visible current multi-sig users are to the network. It also raises a question: With multi-sig growth at anemic levels, is there really demand to justify adding these features? (We discussed that question on CoinDesk TV’s “All About Bitcoin” show last week.)
Multi-sig’s shortcomings may be a barrier to adoption, which Taproot could address, opening the door to increased use. That could improve custodian services and make direct-custody forms of investment more attractive. Or, this could be a vaunted new feature that nobody will use. (Remember Microsoft Sets?)
Most technology investors understand the technology risk inherent in an update. (See Samsung Galaxy Note 7.) There’s also the adoption risk of developing a feature that nobody uses.
Unlike Ethereum, Bitcoin developers prefer backwards-compatible updates. After Taproot is implemented, users will still be able to use pre-Taproot transactions. This would be self-defeating for Taproot’s multi-sig privacy features: pseudonymity only works in a crowd.
Improving multi-sigs also could make it easier to develop applications on top of Bitcoin, an especially relevant issue in 2021 as decentralized finance, non-fungible tokens and stablecoins have driven the cryptocurrency bull market. At this writing, the year-to-date returns on ether are roughly 10 times those of bitcoin.
At this point, it seems likely that Taproot will be enacted by the Bitcoin network, as more and more miners signal approval. Whether users take advantage of its features will be a telling test of bitcoin’s adaptability and, by extension, its viability as an updatable technology investment.
On the other hand, a perceived inability to update or adapt may strengthen Bitcoin’s resemblance to gold – which, after all, does neither.
Among events in Bitcoin’s history, the Taproot update is receiving far less attention than, say, the Bitcoin halving, which occurred around this time last year. In the long run, it may prove more significant.
Updated: 6-12-2021
Bitcoin Taproot Upgrade Finally Locked-In, Activation Set For November
With Taproot achieving the 90% critical consensus mark among mining nodes, all is now set for Bitcoin soft fork activation later in November.
The Taproot upgrade has achieved the first significant milestone on the road to activation as 90% of the Bitcoin (BTC) mining hash rate signaled for the protocol improvement within the current difficulty epoch.
Data from Taproot.watch, a webpage created by Bitcoin developer Hampus Sjöberg, shows the lock-in stage is now completed.
All recognized mining pools signaled for the upgrade with Slush Pool being the first to do so. It is perhaps fitting that Slush Pool also mined block 687285 that sealed the Taproot lock-in.
TAPROOT LOCKED IN AT BLOCK 687285 BY SLUSHPOOL pic.twitter.com/FFDdibtmGt
— pourteaux (@pourteaux) June 12, 2021
AntPool and F2Pool — the top two Bitcoin mining pools by hash rate share — were also among one of the earliest supporters of the Taproot activation in the BTC mining arena
In a conversation with Cointelegraph Bitcoin core developer Pieter Wuille explained the activation step for Taproot, stating: “According to BIP341, once locked in, activation is automatic at block height 709632 – expected around November 14, 2021.”
Wuille also commented on the significance of Taproot, adding:
“It’s the first consensus change since Segwit activated in august 2017. It extends Bitcoin’s script capabilities in ways that make certain things cheaper (especially more complex applications like multisig and layer 2 things), and somewhat more private by often hiding what the exact spending rules were.”
According to Wuille, the activation in November is only the beginning as the real work will be building the software to leverage the benefits of the protocol improvement.
June 12’s historic significance for Bitcoin has also moved beyond Taproot as the day seen a record number of transactions mined in a single block. Data from blockchain explorer Blockchair shows 4,075 transactions in block height 687249.
This record figure is almost twice the average transactions per block recorded on June 11 and is four times the typical transaction count for Bitcoin blocks.
With hash rate declining amid mining restrictions in China, Saturday’s transaction count average might be due to a slowdown in block production forcing more transactions to be included in a single block.
Bitcoin’s Taproot upgrade, the most anticipated upgrade for the largest cryptocurrency since 2017, has enough mining support to lock in activation, according to CoinDesk.
* At least 90% of the blocks mined in any of the designated two-week difficulty periods needed to “signal” their support for the upgrade for the activation process to begin, CoinDesk said.
* Taproot will likely have locked in with more than 99% of blocks signaling decisively in its favor by the time the difficulty period ends Sunday: CoinDesk.
* Taproot will adjust the Bitcoin code in a way that introduces new possibilities for privacy, multisignature wallets and security, and scaling, CoinDesk said.
* Over time, Taproot’s tooling and coding improvements will lead to a better Bitcoin user experience in terms of overall performance, and offer privacy improvements to multisignature technology, privacy software and scaling technology such as the Lightning Network, CoinDesk said.
Updated: 6-14-2021
The Future of Bitcoin Privacy: Cross-Input Signature Aggregation
Privacy is something everyone talks about but few people actually take time to do properly. This is as true in life as it is in Bitcoin. Coinjoins are not a great user experience right now.
Not only are the anonymity sets small, but the process itself takes a long time and costs money, which motivates people to not do it. Not enough people custody their own coins, and even fewer have the technical knowledge to actually coinjoin in one of the many protocols.
The problem, like with most privacy tech, is that it costs a non-negligible amount of time and money. This can be a problem in an increasingly authoritarian world that demands permission to do even the most basic things. Many places transmitting or handling money must comply with AML/KYC laws, which are a giant tax on these companies. CoinJoin isn’t quite that bad, but it’s still not easy and most people simply don’t bother with it.
Cross-input signature aggregation changes the equation. Currently multiple inputs require multiple signatures. Cross-input signature aggregation is combining these multiple signatures with Schnorr, or combined into a single signature. This may not sound like much at first, but think about what this means.
Signatures are the biggest parts of a transaction, so reducing signatures means that the transaction becomes smaller. Not only do smaller transactions mean more transactions per block, but also mean less fees per transaction. A transaction with only 1 input will cost the same, a transaction with 2 inputs will get a significant savings, a transaction with more inputs gets even more savings on a per-input basis.
Practically speaking, this means that if there Alice wants to pay Bob and Carol wants to pay Dave, Alice and Carol can combine their respective transactions and pay less fees in total. This is somewhat true today by what’s called batching, but cross-input signature aggregation takes this to another level. Even if there are hundreds of inputs, only 1 signature is required, so the transactions get cheaper on a per-input basis the more inputs there are.
Now this is not possible until Segwit v2 at least, which would be the softfork after Taproot, but it’s a huge development. It makes coinjoin economically rational! Instead of paying for the privilege of better privacy, you would be saving money to get better privacy.
This will be particularly true of exchanges, where a lot of these transactions take place. They will want to coinjoin exiting customer transactions with lots of other transactions to save money and the side-effect will be more privacy for the rest of that transaction!
In any case, there’s a lot of buzz around requiring more KYC, but this is one possible response at the protocol level that we might be coming towards.
Updated: 6-15-2021
Bitcoin Network Approves Privacy Update As Scrutiny Increases
Bitcoin is gaining more privacy features as concern increases over the use of the cryptocurrency during a recent spate of ransomware attacks.
The most significant update in four years to the computer software that underpins the world’s largest digital token was approved this past weekend with little fanfare. In past years, fights among the groups known as miners who run the network were characterized as a civil war and led to offshoots such as Bitcoin Cash.
While the main advance makes the network easier to use for certain big embedded applications called smart contracts, the so-called Taproot update could also let more people use privacy wallets and services that make it harder to figure out who paid whom.
That could enhance the anonymity features prized by advocates of the currency, which law enforcement says is often used for illicit purposes. The U.S. has recently linked cyberattacks against Colonial Pipeline Co. and meat producer JBS SA to groups in Russia that used the cryptocurrency.
“Things will be less fingerprintable — which use-case or wallet they are,” Adam Back, chief executive officer of crypto services developer Blockstream, which helped code Taproot, said in an interview.
Proponents of Bitcoin, who have long called the taint of illicit use overblown, said the changes could improve how payments to hundreds of people are sent, and how crypto derivatives or bets are made on the network.
Today, the vast majority of smart-contract applications are being built elsewhere, on networks like Ethereum.
Taproot won’t quite make the Bitcoin network a direct competitor since Ethereum has more developer activity and features, and is easier to use. But it’s a step in that direction, and it could make Bitcoin more attractive to more users and developers.
“It could in principle allow them to make practical things which are today too big, or complicated programs, so they get expensive,” Back said. “It would allow them to be used more widely.”
The exact new applications Taproot will enable could take a while to determine.
“It will honestly take years for the developers to figure out how they are going to implement these new transaction types,” said Nic Carter, general partner at Castle Island Ventures. “But it’s definitely a scope for creativity. I definitely see it as a driver in as much as it proves that Bitcoin can still innovate and can upgrade itself.”
The Taproot update was approved last weekend by the majority of miners, whose computers verify transactions and are awarded Bitcoin. It will take place in November.
“We obviously support anything that will grow demand for new uses of Bitcoin and the Bitcoin network,” said Fred Thiel, CEO of Marathon Digital Holdings, a Bitcoin miner that’s in favor of the upgrade. “What this does is it ensures long-term viability for the Bitcoin network and mining.”
Taproot will be a soft fork, meaning that the upgrade will be compatible with prior versions of the software.
One key feature is so-called aggregated public key multi-signature, which effectively hides some of the complexities of a transaction posted to the Bitcoin network. Not only does it ensure greater privacy of transactions, it also allows for cheaper transactions by reducing the amount of data to be recorded on the blockchain.
Leading blockchain investigative services like Chainalysis and Elliptic said they should still be able to figure usage out anyway.
“Taproot has little impact on the traceability of Bitcoin,” said Tom Robinson, co-founder of Elliptic. “However there is a push to introduce other privacy features into Bitcoin, which would make it far more challenging to track criminal funds. I believe that Bitcoin has been able to grow over recent years partly because its traceability has assuaged concerns from regulators about its illicit use.”
The lower fees could also potentially provide a boost to efforts like RSK and Stacks, which are making it easier for developers to build decentralized applications, or dapps, for Bitcoin — such as yield services that let people holding the digital currency earn interest on the coins.
Updated: 6-26-2021
Bitcoin Taproot Locked In To Improve Privacy And Introduce Smart Contracts
The Bitcoin Taproot upgrade will activate later in 2021 as developers urge to create applications that will leverage its advantages.
On June 12, Bitcoin (BTC) mining pool Slush Pool mined block 687,285 with the transaction including a Taproot upgrade activation signal. That particular block was the 1,816th to include a signal for Taproot activation by a BTC miner within the difficulty epoch that lasted from May 30 to June 13.
With 2,016 blocks created every difficulty period, crossing 1,816 blocks with a Taproot activation signal satisfied the 90% signaling threshold required to lock in the upgrade. This event meant that Taproot, Bitcoin’s first protocol upgrade in over four years, was set for its activation phase to be expected in mid-November.
Apart from bringing an end to the signaling period that lasted about six weeks over three consecutive difficulty epochs, block 687,285 also brought forth a new milestone for the Bitcoin upgrade in development since 2018. BTC proponents say beyond the automatic activation happening near the end of the year, the focus should now shift to building wallets and other ecosystem applications that can leverage the improved scripting capabilities brought on by Taproot.
What Is Taproot?
Before getting into the nitty-gritty of what Taproot is and how it works, it is perhaps important to present at least a high-level explanation of how Bitcoin transactions work. When sending BTC from one wallet to another, the sender’s public address uses a private key to create a unique cryptographic signature.
This cryptographic signature contains the necessary permissions that serve as proof to any nodes validating the transaction that the sender truly owns the funds being sent, thus fulfilling the spending condition. It is possible to create different spending conditions for unspent transaction outputs (UTXOs).
When UTXOs are spent, it becomes necessary to reveal all spending condition data — both the ones satisfied and the possible conditions that could have been met — a feature that comes with significant data usage and privacy implications. Taproot is an upgrade designed to solve this issue by masking spending conditions, except those that are in the branch of the script agreed upon by the transacting parties.
In a conversation with Cointelegraph, Riccardo Casatta, Bitcoin developer and one-time Square crypto grant recipient, outlined the basic premise behind Taproot, stating, “The taproot upgrade includes a bunch of improvements, the most significant enhances privacy in the long term.” According to Casatta:
“A misconception we have today is that Bitcoin usage is mostly private, while in reality, transaction activities leave a lot of traces on the blockchain. For example, Bitcoin is sent to different addresses — e.g., starting with ‘1,’ ‘3’ or ‘bc1,’ according to the version and the smart contract behind them. This is a problem because it reveals information about the user’s spendings.”
With Taproot, it becomes possible to combine the public keys of all participating entities in a transaction to create a unique key. By creating a new output called Pay to Taproot (P2TR), it is possible to have output conditions with locked funds to a single public key rather than individual key or script hashes that require a complete accounting of all spending conditions included in a UTXO.
This coalescing of multiple signatures into a single aggregate signature is based on Schnorr signatures. Taking advantage of the linear nature of Schnorr signatures, Taproot proponents say it will be possible to make multi-signature (multisig) indistinguishable from their single-signature counterparts, or as Casatta puts it:
“With taproot, different spending conditions may look identical in the most common case, and this is great because it reveals less information about users, and it also improves efficiency.”
Near Unanimous Support Among Miners
As previously reported by Cointelegraph, Bitcoin’s Taproot upgrade achieved the 90% critical consensus among mining nodes on June 12. Indeed, the process received near-universal backing from miners, with all recognized mining pools signaling for Taproot.
Slush Pool kicked off the process back in May, mining the first transaction block with a Taproot activation signal. It was, perhaps, fitting that the fifth-largest Bitcoin mining pool by hash rate distribution was also brought forth by the miner responsible for actually locking in the upgrade.
Despite the fact that the process for commencing the signaling period slowed down with China’s May Day celebration, the consensus among miners to support the upgrade began to reach significant proportions by the second difficulty epoch. This near-unanimous support cemented the commitment expressed by miners even before the planned upgrade was merged into Bitcoin Core in late 2020.
The initial delays in attaining the required 90% consensus during the first month of the process were likely due to some miners needing to adjust certain firmware requirements to perform signaling. Thus, even soaring to about 70% within the first three days, the miner signaling percentage fluctuated between 40% and 70% over the first difficulty epoch.
AntPool and F2Pool — ranked first and second in terms of hash rate distribution, respectively — were early supporters of the activation, as was Foundry USA. By May 17, every major mining pool was signaling for Taproot, including Binance with its maiden transaction block. BTC.Top was late to the party, as the mining pool reported having to run tests on protocols required to begin signaling for Taproot.
Privacy, Scalability And Smart Contracts
Several Bitcoin developers agree that Taproot will offer a significant improvement in Bitcoin’s privacy. In a conversation with Cointelegraph earlier in June, Pieter Wuille, Bitcoin developer at Chaincode and one of the earliest proponents of the Taproot upgrade, remarked:
“It [Taproot] extends Bitcoin’s script capabilities in ways that make certain things cheaper (especially more complex applications like multisig and layer-two things), and somewhat more private by often hiding what the exact spending rules were.”
Apart from masking certain spending conditions and making transactions indistinguishable, Taproot also offers a significant reduction in the block space occupied by transaction data. While this feature will reduce transaction throughput by compressing the data size associated with multisig transactions, it is hardly a panacea to Bitcoin’s scalability issues.
However, it opens the door for smart contracts on the Bitcoin blockchain since the upgrade already lessens the amount of space needed for multisig transactions in a block. Smart contract transactions by nature involve interactions among several addresses and users.
With Taproot, these smart contract operations will not appear to be any different from a simple wallet-to-wallet BTC transfer. Detailing some of the likely smart contract use cases that could emerge once Taproot is activated later in 2021, Casatta told Cointelegraph:
“In the middle/long term, I see an increase in Bitcoin smart contract usage, enabling use cases like inheritance and delegation in company spendings. And the best part is that, by looking at the blockchain, we will not know about that.”
Many Bitcoin developers agree that beyond the November activation, network participants will need to create useful applications based on the upgrade. The upgrade itself will activate according to the terms in Bitcoin Improvement Protocol 341 (BIP-341) at block height 709,632.
Taproot will be a soft-fork upgrade, meaning that network participants are not bound to adopt the change. However, given the likely fee advantages offered by the upgrade, service providers are likely to update their software to implement Taproot.
Updated: 7-8-2021
Bitcoin Privacy Wallet Wasabi Lays Out Roadmap For Version 2.0
Wasabi Wallet 2.0 will introduce privacy enhancement “WabiSabi,” a more efficient CoinJoin framework.
Today, privacy-focused Bitcoin wallet Wasabi reports it has made significant progress toward the release of its Wasabi Wallet 2.0.
Founded almost three years ago, Wasabi Wallet pools multiple users’ unspent transactions (UTXOs) into a single Bitcoin transaction using CoinJoin. CoinJoin is a trustless process that makes it difficult for third-party observers, or even participants, to trace funds and it significantly lowers transaction fees. In order to protect the anonymity of its users, Wasabi traffic runs through the Tor network, an online network that focuses on censorship resistance and anonymity, by default.
Wasabi Wallet 2.0 aims to improve the user interface of the wallet as well as introduce a more efficient coinjoin framework, which developers call WabiSabi.
“One of the biggest challenges was developing the software for more than just cypherpunks and people very well versed in Bitcoin,” said CTO David Molnar.
“It was difficult to get the developers and contributors to see the bigger picture, that we can only win the privacy war if we expand our vision to include all future Bitcoin users and not just the privacy advocates and cypherpunks.”
While the new UI will allow users to access “pleb-friendly,” frictionless and secure payments via Tor, WabiSabi boasts its own set of upgrades.
* Users will no longer need to run coins through multiple coinjoins in order to gain privacy.
* There will no longer be a minimum (0.1 BTC (-5.54%)) or maximum (7 BTC) denomination when using coinjoins;
* There will be improved block space efficiency, allowing more inputs into a single coinjoin transaction. This will lower fees for each user.
Wasabi Wallet 2.0 has no defined launch date; however, the company has committed to and published three milestones:
* Wasabi Wallet 2.0 Preview will contain only the most fundamental features and will be used only on the Bitcoin testnet. This will be released in around 6-14 weeks.
* Wasabi Wallet 2.0 Release Candidate will include all features and will be available to the public for reviewing and testing. The team will work on this version until ”the quality of the software is sufficient.”
* Wasabi Wallet 2.0 Final Release (Series) will be the first version of the 2.0 series and the default when new users download the wallet. With that being said, both versions will be available until “most users” migrate to 2.0.
Updated: 10-1-2021
Creating A Bitcoin Taproot Account In Ledger Live
What Is Taproot?
Taproot is Bitcoin’s latest and most significant network upgrade since SegWit in 2017. Taproot consists of a bundle of improvements to the Bitcoin protocol. These improvements are expected to boost Bitcoin’s privacy, efficiency, and smart contract or scripting capabilities. You can learn more about Taproot and how it improves Bitcoin here.
Taproot automatically activated at block height 709,632 on November,14th 2021.
Taproot activation was done via a soft fork. A soft fork is an optional change to the rules of the Bitcoin network that needs to be approved by each Bitcoin node. Fortunately, the Taproot upgrade is backwards compatible. Backwards compatibility means that nodes that have upgraded to Taproot still retain full compatibility with nodes that have not.
Ledger fully supports Taproot and is bringing its full capabilities to all Bitcoin users.
What Changes For Me?
With Taproot now supported by Ledger, you are able to create a new type of Bitcoin account in Ledger Live: a Taproot account.
Taproot accounts join the list of available Bitcoin account options alongside Legacy, SegWit, and Native SegWit accounts (more on these account types here).
Depending on your Ledger device, creating a Taproot account first requires a series of updates.
Ledger Nano X
- Update Ledger Live through the notification banner or download the latest release of Ledger Live from the Ledger Live download page. Learn how to update Ledger Live.
- Open Ledger Live and connect your Nano X device to the Manager.
- Ensure that your Ledger device is running firmware version 2.0.0 or higher. If not, please update.
- Update the Bitcoin app to version 2.0.1.
- Navigate to the Accounts tab and click the +Add account button.
Add account window appears. - In the drop-down menu, select Bitcoin (BTC) then click Continue.
- Toggle Show all address types, select a Taproot account, click Add account then Done.
Ledger Nano S
- Update Ledger Live through the notification banner or download the latest release of Ledger Live from the Ledger Live download page. Learn how to update Ledger Live.
- Open Ledger Live and connect your Nano S device to the Manager.
- Ensure that your Ledger device is running firmware version 2.0.0 or higher. If not, please update.
- Update the Bitcoin app to version 2.0.1.
- Navigate to the Accounts tab and click the +Add account button.
Add account window appears. - In the drop-down menu, select Bitcoin (BTC) then click Continue.
- Toggle Show all address types, select a Taproot account, click Add account then Done.
Can I Send Bitcoin From A Taproot Account To A Non-Taproot Account?
- Yes, Taproot accounts are fully compatible with non-Taproot accounts.
- This means that you can safely send BTC from a Taproot account to a Legacy, SegWit, and Native-Segwit account and vice versa.
Why Should I Use A Taproot Account?
Taproot accounts can create more efficient and private Bitcoin transactions.
Taproot introduces an improved cryptographic scheme called Schnorr signatures. Transactions that leverage Schnorr signatures take up less space inside Bitcoin blocks and are easier to verify. While this won’t translate into a dramatic reduction in transaction cost, Taproot users might notice a slight improvement in overall transaction speed and a very mild reduction in fees.
Regarding privacy, Taproot harmonizes the on-chain footprint of Bitcoin transactions. Without Taproot, it’s very easy for a malicious actor to observe the Bitcoin blockchain and tell a transaction involving multiple signatures (also known as a multisig transaction) from a transaction involving only one signature.
Multisig transactions are typically used to secure large amounts of Bitcoin so their users would rather not have their transactions easily flagged on the blockchain.
By aggregating any number of signatures into a single signature, Taproot can create transactions that all look identical on the Bitcoin blockchain, regardless of how many signatures were involved. As Taproot slowly becomes the new standard for transacting on Bitcoin, so will privacy improve for all Bitcoin users.
On a final note, Taproot also helps Bitcoin scale because signature aggregation reduces the cost of creating and executing complex Bitcoin transactions such as creating Lightning Network channels. You can learn more about the Bitcoin Lightning Network here.
As updates continue to occur with Taproot and Bitcoin, we will continue to provide secure and transparent information for you to use your Ledger devices seamlessly.
For additional information follow @Ledger and @LedgerSupport.
Updated: 10-29-2021
BTCPay Server Supports Taproot
# Taproot Woot Woot ????
BTCPay Server 1.3.0 adds the ability to create and track wallets that use the new Taproot format. This feature will be available starting block 709632, at which point Taproot becomes activated on the bitcoin network.
BTCPay Server already introduced Taproot sending support last August, and this was the last missing part for full Taproot support.
Updated: 11-14-2021
BREAKING: The Bitcoin Network Welcomes Taproot Soft Fork Upgrade
Taproot soft fork introduces the concept of Merkelized Abstract Syntax Tree (MAST) to improve the scripting capabilities and privacy of the Bitcoin network.
The Bitcoin (BTC) network successfully activated the Taproot soft fork following a 90% lock-in consensus from miners and mining pools between blocks 709,488 and 709,632. The milestone signifies the first major upgrade for Bitcoin since August 2017, which saw the launch of Bitcoin’s leading layer-two solution, the Lightning Network and Segregated Witness (SegWit).
The Taproot upgrade aims to improve the scripting capabilities and privacy of the Bitcoin network. To do this, the soft fork introduces the concept of Merkelized Abstract Syntax Tree (MAST). According to a Taproot-dedicated website run by prominent Bitcoin developer Hampus Sjöberg:
“[MAST] can help make smart contracts more efficient and private by only revealing the relevant parts of the contract when spending.”
Speaking to Cointelegraph, Sjöberg pointed out that Taproot activation shows that Bitcoin can do network upgrades again, which is extremely important for the longevity of the Bitcoin network. “I think that’s the greatest win,” he added.
Sjöberg, who is also a developer of a Bitcoin Lightning wallet Blixt Wallet, believes that the Taproot upgrade allows exploring off-chain capabilities, as to not put too much burden on the Bitcoin nodes of the network.
Taproot is a 100 years softfork.
Merging every contract and use-case under a single transaction type “Pay to Taproot” will in the long-run yield a more fungible and robust blockchain.
This is how you do it.
This is how you design a blockchain.— Hampus Sjöberg ⚡ (@hampus_s) June 3, 2021
In addition, Sjöberg believes that MAST can also help improve the privacy of the older Lightning Network “if the Lightning implementations choose to adopt Taproot.” The developers of the various Lightning Network node implementations met in Zurich, Switzerland just a few weeks ago at the LN Summit 2021 to discuss possible upgrade paths:
“One of the things that were discussed in the meeting was whether it’s best to upgrade Lightning in small iterations or do it as one big package.”
Moreover, Sjöberg explained how payment channels under normal circumstances can be made indistinguishable from normal transactions using Taproot for the Lightning Network:
“It’s not possible to tell if a Taproot transaction is just a normal payment or if it belongs to a Lightning channel. This is important for the fungibility and thus the censorship resistance of Bitcoin.”
Taproot’s successful activation is attributed to Speedy Trial, a soft fork deployment method that requires 90% of the miners to signal the deployment of the upgrade. As explained by Sjöberg, “the signaling method works in periods of 2016 blocks, meaning that within a 2016 block period, 90%, or 1815 of the 2016 blocks have to signal for readiness.”
Back in June 2021, the Bitcoin miners achieved a 90% consensus for the first time and Sjöberg tweeted the announcement:
WE HAVE LOCK IN! #Bitcoin #Taproot
Video by: @TheGuySwann!https://t.co/rCUp5VNCBX pic.twitter.com/YFLMTenWW0
— Hampus Sjöberg ⚡ (@hampus_s) June 12, 2021
However, the Taproot upgrade also marks the end of Speedy Trial deployments and future upgrades to the Bitcoin network will require provision for new soft fork deployment methods. “Taproot opens a world of possibilities, but the first thing I personally would like to see is a “MuSig 2″ transaction.” Sharing advice for fellow Bitcoin developers, Sjöberg said:
“While we should not take anything for granted in Bitcoin, I personally would like to eventually see “Cross-Input Signature Aggregation” as a future soft fork for Bitcoin.”
In Bitcoin’s near 13 years of existence, the Bitcoin network has undergone numerous community-driven hard and soft forks. While the Taproot upgrade is yet to prove its worth in time to come, the Lightning Network continues to attain new heights.
On Sept. 28, the Lightning Network witnessed a 160% increase in the number of nodes in the span of 12 months in addition to seeing a jump of 170% in the number of channels since January 2021.
As of Nov. 11, Bitcoin’s network capacity prior to Taproot soft fork was at an all-time high of 3,220 BTC, nearly worth $210 million.
Updated: 12-13-2021
How Blockchains Benefit From The Latest Taproot Upgrade On Bitcoin
A month ago, the Bitcoin community welcomed its first major network upgrade in four years, as the Taproot upgrade went live in November. The upgrade aims to introduce smart contract capabilities and offer greater transaction privacy on the Bitcoin network. Unlike the 2017 SegWit upgrade, the Taproot upgrade witnessed a rare moment of consensus among the network participants, with over 90% of the miners voting in favor of the upgrade.
At its core, the Taproot upgrade will make multisig transactions more private, while improving the network’s efficiency by unlocking the potential for smart contracts, which will reduce the cost of transactions and increase the speed of transactions.
Simply, the Taproot upgrade boosts the capabilities, utility, and functionalities of the Bitcoin network.
As mentioned above, the 2017 SegWit upgrade led to a contentious ‘civil war’ among the Bitcoin community causing a hard fork that created Bitcoin Cash, BCH. The latest upgrade took a cleaner and more community-focused route as Taproot gained near-universal support as the community agreed the improvements on the code were fair and efficient.
What Does Taproot Bring To Bitcoin?
The main advancement brought about by Taproot is digital signatures. Bitcoin uses the Elliptic Curve Digital Signature Algorithm (ECDSA) to create digital signatures and keys that verify transactions on the network. With the Taproot upgrade, Schnorr signatures will be introduced, which reduce the network data load, are more secure and simple to implement.
Via Schnorr signatures, users can batch multiple signatures and transactions together to send them as one transaction. This is quite to the current ECDSA signatures which require every signature to be validated against a single public key, which slows down the verification of Bitcoin transactions. This extended the time required for complex multisig transactions that require multiple inputs and signatures.
Simply, the Taproot upgrade will enable aggregation of multiple signatures into one transaction, easing up the validation and verification process. Now, users will be able to quickly verify multiple transactions in one batch instead of verifying one transaction at a time.
Additionally, the Taproot upgrade also improves the network’s privacy as it is more difficult to identify an individual transaction from a complex one. The aggregation of multi-signature transactions is masked from identification from the single-signature transactions.
The aggregated signature transactions also improve the smart contract capabilities of Bitcoin’s network. Theoretically, users will be able to create decentralized applications, or DApps, hence expanding the utility of the blockchain.
A New World For Other Blockchains
While the upgrade was focused on Bitcoin, other blockchains are also implementing the upgrade to make their platforms more accessible and efficient. Shortly after the consensus to upgrade to Taproot, QTUM, the 92nd largest blockchain, was among the leading blockchains apart from Bitcoin to support the Taproot upgrade.
In May, Qtum founder, Patrick Dai showed his support for the Taproot upgrade activation stating the upgrade “will bring incredible utility and robustness to Bitcoin” due to the Schnorr signatures. Months later, QTUM announced they will be supporting the Taproot upgrade on their blockchain to improve efficiency in transactions.
Founded in 2016, QTUM was one of the first blockchain projects to combine Ethereum and Bitcoin features onto a platform. The blockchain combines Ethereum’s smart contract functionality with the security of Bitcoin’s unspent transaction output model (UTXO) creating a scalable and cheap platform for large corporations or organizations to use.
With the Taproo’t upgrade, QTUM users will be able to send multi-sig transactions faster and pay a lower transaction fee every time they transact on the network.
However, QTUM is not the only blockchain to implement the Taproot upgrade on its blockchain. Nimble Syscoin, a Bitcoin-modeled blockchain offering fast, cheap and scalable transactions, announced they would be upgrading to Taproot to boost their transactional efficiency.
The Expected Bitcoin Upgrades In The Future
The Taproot upgrade is expected to scale the blockchain transactional system – making it more secure, private and lowering the fees. However, this is not the last upgrade expected on Bitcoin in the near future. Developers, miners, and other stakeholders are already working on new updates to further improve the network.
At the top is the cross-input signature aggregation, or CISA, which proposes to allow single transactions to be aggregated to enhance privacy and reduce the cost of mixing coins. According to the proposal, privacy-enabled wallets or mixers such as Wasabi and Samourai will be able to mash up all transactions at a given time into one large transaction, to make it difficult to distinguish the origin of the transaction while reducing the cost of the transaction.
Additionally, developers have also proposed to introduce “covenants”, which would restrict where a certain wallet can send funds. This would help corporations manage their wallets better, for example, allowing the transactions to be sent to only a few whitelisted addresses.
Final Words
The Taproot upgrade is set to breathe a new life to Bitcoin’s network. With faster and cheaper multi-sig transactions, corporations have a better leeway to use Bitcoin and transact through the chain. It also opens the door for other chains such as QTUM and Syscoin to improve their platforms and offer more efficient services.
Updated: 2-17-2022
It’s Time For Bitcoin To Become A Better Tool For Laundering Money
A popular criticism of Bitcoin is that it’s only good for laundering money. But in fact the problem is just the opposite. It’s not good enough.
In response to the arrest related to the Bitfinex theft, it turns out it’s extremely hard to launder money with Bitcoin because the blockchain is visible for the world to see. Of course, the chain itself doesn’t have user names associated with any specific address or wallet.
However, it’s very easy to watch some amount of Bitcoin and see if it’s on the move. And it’s not hard for regulated exchanges to reject Bitcoin that is deemed to be compromised in some way.
What’s more, while there’s technically no names associated with a given wallet, in many cases it’s not that hard to connect a wallet to a real name. If you buy your Bitcoin at an entity like Coinbase or any other established, regulated exchange, your name can be connected to a spend. It’s only a matter of working backwards from there.
So critics of Bitcoin are wrong about the money laundering aspect. And in theory this is great for industry participants who can disassociate with any unseemly elements.
There’s just one problem. If Bitcoin isn’t good for laundering money, it might not have a point.
A key selling point is that it’s stateless money. Alice can send money to Bob without any given country or authority getting in the way and saying “no you can’t.” If regulators can easily peer onto the chain and know who Alice and Bob are and what they’re up to, then it’s hard to see exactly what’s been achieved. It becomes especially tough for Alice and Bob if they want to, you know, spend their Bitcoin on actual things. Like food. Or gasoline. Or a house.
The relationship between money and the state is getting a lot of attention right now thanks to the ongoing situation in Canada with the trucker convoy. The Canadian government has invoked emergency powers in an attempt to cut off the truckers — and their supporters from the financial system. First we saw crowdfunding sites stop doing business with them. Now basically any financial entity — from banks to brokers — can cut them off.
So it would seem this is, in theory, what crypto was built for. An alternative, stateless money system that would allow anyone to transact without permission from the state. Except according to The Globe & Mail, regulated crypto entities have been instructed not to accept coins from 30 wallets that have been identified as being associated with the convoy.
I spoke yesterday with Alex Gladstein, a big Bitcoin advocate, and Chief Strategy Officer of the Human Rights Foundation. His main argument for years has been that Bitcoin can be a powerful tool for people living in oppressed societies, whose governments may shut dissidents off from the formal financial system.
Even if you don’t see the truckers in Canada as being oppressed dissidents, if they can’t use Bitcoin, then the cryptocurrency can’t be used by people towards whom you might be more sympathetic in a different environment.
Gladstein thinks it’s a mistake for Bitcoiners to accept the premise that it’s not good for money laundering. As he puts it, “It has to be good for money laundering if it’s going to be freedom money.”
As he put it, there was an understanding from the very beginning that Bitcoin didn’t have great privacy, and that it was a purposeful tradeoff at the start.
Other priorities — such as the ability of individuals to run full nodes and confirm the number of coins out there independently — were deemed to be more important. And for the first several years of Bitcoin’s existence, there was a kind of blissful state, where nobody really thought much about blockchain analysis. But obviously analysis of the chain has gotten extremely good, and now for Bitcoin to have a point the ecosystem needs to level up.
According to Gladstein, privacy tech is advancing all the time within the Bitcoin ecosystem. There are things like Coinjoin, where people can combine their Bitcoins, such that it’s difficult to see who has control of what. There are things like Payjoin and Coinswap that are variations on the idea of essentially putting money into a pot, and then obfuscating who took it out. Alex’s preferred solution, however, is to use the Lightning Network, which essentially allows Bitcoin transactions to settle ‘off chain.’
“The way to think about where we’re going with Lightning is it’s like an ATM,” says Gladstein.
So basically, when people take cash out of an ATM, it becomes extremely difficult for anyone to track how the money is being spent. With Lightning, Bitcoin transactions are still digital, but they’re not on the chain itself. (If you’re interested in more, we talked about how Lightning worked years ago in an episode of the podcast).
Of course, Bitcoin itself still isn’t particularly mainstream and within even the universe of Bitcoin holders, some of these more exotic efforts to obfuscate transactions (or even spend it) are still pretty niche. So per Gladstein, it was a mistake for the supporters of the truckers to publicly advertise a single wallet address that authorities could easily identify as being associated with them.
Ultimately he thinks Bitcoin’s goal should be the equivalent of other open projects, like Signal, Tor, or even email itself. Yes, they can be used by people you don’t like. But if they couldn’t be used by them, then they couldn’t be used by the people you do like.
And if Bitcoin never achieves this status — where it can be used by anyone without influence from a centralized entity like a government — then it’s really not clear at all what the point is. If all you want is just an inflation hedge to keep at a bank, then buy TIPS or something.
Updated: 2-25-2022
Should The Bitcoin Taproot Soft Fork Be Buried In The Code Base?
Bitcoin Core developers are considering “burying” the Taproot soft fork, to help developers when reviewing the code, but it could have unintended consequences.
In this episode of “Bitcoin, Explained,” hosts Aaron van Wirdum and Sjors Provoost revisit the Taproot activation saga, this time to discuss the burying of soft forks.
Taproot, the last soft fork to have been deployed on the Bitcoin network, activated in late 2021. Now, Bitcoin Core developers are considering “burying” the soft fork, which means that future Bitcoin Core releases will treat Taproot as if the rule change has been active since Bitcoin’s very beginning (with the exception of one block which was mined in 2021 and breached the Taproot rules, but it has since been added to the protocol).
In the episode, Provoost explains the benefits of burying a soft fork, in particular how it helps developers when they review the Bitcoin Core codebase or when they perform tests.
After explaining the benefits, van Wirdum and Provoost outline a potential edge case scenario where burying soft forks could, in a worst-case scenario, split the Bitcoin blockchain between upgraded and non-upgraded nodes.
Bitcoin Core developers generally don’t consider this edge case of a very long block reorganization as a realistic problem, and/or they believe that this would be such a big problem that a buried soft fork would comparatively be a minor concern. However, van Wirdum and Provoost explain that not everyone agrees entirely with this assessment.
Toward the end of the show, van Wirdum and Provoost touch on issues like whether soft fork activation logic itself should be considered a soft fork, and whether soft fork burying logic should be considered a consensus change and/or require a Bitcoin Improvement Proposal (BIP).
Updated: 3-8-2022
Bitcoin Mixers: How Do They Work and Why Are They Used?
Bitcoin offers pseudonymity to users by design. But in order to be completely anonymous, you’ll need to use tools like bitcoin mixers.
The Bitcoin blockchain is entirely public. Head to a blockchain explorer and you can find a watertight record of all the bitcoin transactions ever processed since the cryptocurrency’s launch in early 2009.
For some, that is a core feature, not a problem. But for those who need a little more anonymity, the public nature of the Bitcoin blockchain is a huge privacy flaw.
There are ways of keeping bitcoin transactions entirely private – to obscure who sends what to whom. One of the most popular methods is to use a bitcoin mixer, also known as a tumbler. These are tools that jumble up an amount of bitcoin in private pools before spitting them out to their intended recipients.
The idea is that, by shuffling bitcoin through a black box, it’s difficult to work out that person A sent 10 bitcoins to person B. All a public explorer will show is that person A sent some bitcoin to a mixer, as did a dozen other people, and that person B received some bitcoin from a mixer, as did a dozen other people.
Centralized vs. Decentralized Mixers
There Are Two Main Types Of Bitcoin Mixers:
-
Centralized mixers: like Blender.io.
-
Decentralized mixers: such as Wasabi and JoinMarket.
Centralized mixers are companies that will accept your bitcoin and send back different bitcoins for a fee. While they offer an easy solution for tumbling bitcoin, they also still present a privacy challenge, as while the links between “incoming” and “outgoing” bitcoin will not be public, the mixer itself will still have a record that connects the transactions. Meaning that in the future the company could give up those records and reveal a users’ connection to the coins.
Decentralized mixers employ protocols such as CoinJoin to fully obscure transactions via either a coordinated or peer-to-peer method. Basically, the protocol allows a large group of users to join together an amount of bitcoin (i.e. 100 people want to mix 1 bitcoin each) and then redistribute it so everyone gets 1 bitcoin back, but no one can tell who got what or where it came from.
Problems With Using Mixers
Mixers are not without their flaws. It’s unlikely that someone else in the mixer sent the exact amount of bitcoin as you, minus the tumbler’s fee. If a law enforcement agency knows the address used by its first suspect, and if the second suspect is the only one to have received a little less of a specific amount, it’s not going to be too hard to reconnect the flow of money. This problem becomes harder to solve the more people use the mixer.
Some exchanges don’t allow mixed bitcoin to enter or leave exchanges. Since exchanges can identify mixers, they label mixed bitcoin ‘tainted.” Binance, for instance, has blocked withdrawals to Wasabi, a privacy-preserving bitcoin wallet that integrates a popular mixing service called CoinJoin. Other popular bitcoin mixers include Samourai and JoinMarket.
It’s important to note that not all mixing services are legitimate, and some are far less effective at obscuring financial transactions than others. Be sure to do your research before using a mixer.
Are Bitcoin Mixers Illegal?
The ability to obfuscate bitcoin transactions makes mixers an obvious hotbed for money laundering, attracting the likes of tax dodgers and criminals interested in hiding the proceeds of illegal activity.
The question of whether using these services is illegal depends on which jurisdiction you are based in. In February 2021, then-U.S. Deputy Assistant Attorney General Brian Benczkowski said that using mixers to hide crypto transactions “is a crime.”
Two months later, U.S. authorities arrested Roman Sterlingov, aka the Russian-Swedish founder of bitcoin tumbling service “Bitcoin Fog,” for helping people launder $335 million. In August 2021, Larry Harmon, the owner of a bitcoin mixer called Helix, pleaded guilty to helping darknet market criminals launder around $300 million.
New anti-money laundering rules, like the Financial Action Task Force’s “travel rule” and the European Union’s AMLD-5 directive, will make laundering money tougher, and could make bitcoin tumblers less viable for people who want to join in the wider crypto economy – the sort that relies on popular exchanges accepting your coins.
Alternatives To Bitcoin Mixers
A bitcoin mixer isn’t the only way to hide the flow of bitcoin transactions.
After hacks, criminals often siphon funds through lots of exchanges using accounts created with cheaply bought or stolen identities. This method, known as chain-hopping, relies on the fact it takes law enforcement a long time to force exchanges to shut down accounts; plus, it’s tricky for exchanges to spot dodgy accounts in the first place if they have already passed through know-your-customer (KYC) procedures.
Privacy advocates maintain that methods like privacy coins are a powerful way to prevent the government from snooping on your financial transactions, asserting they are not just for criminals. To obscure the flow of funds, Monero uses one-time use “stealth” addresses and mixes genuine transaction signatures with decoys.
While one of the first major dark web marketplaces, the Silk Road, had a bitcoin tumbler baked into its infrastructure, former darknet market White House Market, known for its security, only accepted Monero.
Alternatively, Zcash offers optional private transactions that rely on zero-knowledge proofs, which don’t share transaction information. Dash’s options of private transactions function a little like CoinJoin.
Updated: 3-9-2022
‘People Will Get Burned’: Matt Odell On The Long Road To Bitcoin Privacy
Privacy advocate and hardcore bitcoiner Matt Odell discusses CoinJoins, privacy coins and “canaries.”
Ask a hundred people what Bitcoin is and you are bound to get a hundred different answers. It’s “digital gold.” An uncensorable transaction network. A high-alpha buy tracking tech stocks.
One thing is clear, however. Bitcoin is not an effective tool for money laundering.
The most notable example is perhaps Russia, which – facing never-before-seen sanctions blocking it from most of the dollar-denominated global economy – hasn’t yet been all that interested in using the stateless monetary network, Bitcoin. Not even the U.S. Treasury thinks crypto will be an effective means to skirt international sanctions.
Bitcoin, as it stands, just isn’t very good for the actual day-to-day needs of criminals, be they individuals or nation-states. That’s because there’s no privacy on Bitcoin. And that’s a problem for law-abiding users as well.
A fully auditable ledger of transactions, grouped and ordered by computer hashes to also make it immutable, the blockchain is unlike any other financial system. The books are fully open, and they leave a permanent record of crime.
Sure, there is a modicum of privacy on Bitcoin by way of native pseudonymous, alphanumeric addresses. You don’t have to reveal your true name to use Bitcoin. But you do if you want to use Coinbase or most other on-ramps to the fiat economy.
“Privacy is the ability to selectively reveal yourself to the world,” said privacy advocate and full-time bitcoiner Matt Odell, who has written a guide on how to achieve this using bitcoin. The system isn’t perfect, but it can be used pragmatically.
Staying private on Bitcoin requires a lot of work. It requires sourcing your bitcoin anonymously and figuring out how to store it, send it and spend it without divulging any personal information – ever. If at any point you leak identifying information, your whole history of financial transactions and all transactions going forward can be tied back to your identity. You have to start again.
Like other bitcoiners, Odell, the co-host of “Tales from the Crypt,” wants to make bitcoin better for anyone in a disadvantaged position – even if that might benefit money launders.
Part of the reason there are so many definitions of or metaphors explaining Bitcoin is that it’s a system that has promise to develop into so much more.
It could be the settlement layer for the global economy or even a reserve asset held by central banks. Despite the lack of privacy, Bitcoin’s other features – its supply limit and censorship-resistance – make it appealing. It’s the best money, Odell says. And because it is the best money, all other finance will fly to it.
In a recent interview, Odell talked about CoinJoins, using bitcoin privately and the need for “canaries.”
So There’s A “Canary” At The Bottom Of Your Website. What’s The Idea Behind That?
Usually companies do it. The idea is that the U.S. government has been known to issue warrants and subpoenas with gag orders where you cannot tell your customers that you’ve got a warrant. But those gag orders don’t stop you from removing something from your website.
So if you have a warrant canary up already, when you get a subpoena, warrant or a request for information, you remove the canary because it doesn’t violate the gag order.
Then you just hope that your audience is paying attention. I am not a company, obviously, but I am an outspoken privacy advocate. So who knows? If there is a situation where I just cannot talk on Twitter the canary text will disappear.
Is This A Serious Threat?
The stakes are extremely high. Privacy is a very sensitive topic, period. We have had governments push against encrypted communications and censor different privacy-related topics. Financial privacy is even more sensitive because it so quickly morphs into, “Oh, you’re enabling terrorists.”
That’s a real pigeonhole advocates face – when obviously the goal is accessible financial privacy for the whole world. Criminals are already going to be able to use these tools privately; the question is if the average person is going to, too.
Is There A Contradiction Between Living A Public Life And Advocating For Privacy?
Privacy advocates get stuck in a hole because if we do not have people talking about it then we have already lost. But if you care about privacy, you do not really want to talk about it, which is why you see a lot of privacy advocates or “nyms” [short for pseudonym] not showing their faces.
The unfortunate reality in our society is people do not take you as seriously if you are not a public individual. So the way I have circled that square is I put myself out there, but I try my best to elevate and empower nyms so it is more distributed. The other thing is, there is this disconnect between privacy and secrecy.
Privacy is the ability to selectively reveal yourself to the world – so people might know my face, they might know some things about me, but they know what I want them to know in a controlled way as much as possible.
If You Could Do It Over Again Would You Use A Pseudonym?
First of all, I have a ton of names. Many names. The name is not the issue. The issue is the face. If I did it again, I might not show it. You know, names can be changed, our faces are with us forever.
We live in a world of increasing facial recognition – my face is likely in government databases around the world. And that is not great. But it goes back to the same trade-off, right? I do not think my platform would be as large if I did it any other way.
What Does “Functional Privacy” Mean? It’s A Term I Hear A Lot In Reference To The Open Bitcoin System, Where, Strictly Speaking, Privacy Is Impossible, But Pseudonymity Can Be Maintained.
With Bitcoin, you do not explicitly have a name attached to your Bitcoin addresses or when sending transactions. But every transaction does get recorded in this public ledger that we call the blockchain forever, and that is going to outlast all of us if we are correct.
It can be explored by anybody who has an internet connection. One of the dangerous things that can be done – after the fact, you do not need an active adversary – is that someone can find something out about you and then go back on-chain and follow everything you have done. That means if you do not start practicing privacy best practices now, it could have massive effects for you down the line that you’re not even considering.
At the same time, we have every regulated company requiring intimate personal information on bitcoin users. They are keeping huge lists on our transaction history, our balances. That information is obviously used to track users, to deanonymize users.
We have surveillance, mercenary companies that have popped up that are focused purely on doing that for both corporations and governments, so the privacy situation on Bitcoin right now is not great. Over 95% of users are probably coming in through KYC [“know your customer”] on-ramps if not more.
At the same time, the fact that Bitcoin is an open ledger is a key aspect of its value prop[osition]. The whole idea is that you do not have to trust anybody, that you can verify everything yourself. That is enabled because it is easy to use your own node, and the ledger is transparent and verifiable.
Everything Has Trade-Offs. Where’s The Middle Ground?
The middle ground is more user-friendly apps that can give people practical privacy that is accessible on the app level rather than necessarily trying to bake it all into the actual Bitcoin protocol.
We have started to kind of see that over the last few years. We have Wasabi and Samourai wallets. They are about to put out Wasabi 2.0, which hopefully should fix a lot of the issues that we have seen in Wasabi 1, which I do not recommend right now. I recommend Samourai Wallet and JoinMarket.
Privacy is a very achievable goal in Bitcoinland, but the protocol is extremely hard to change – that’s another key aspect of its value prop, because if you could change it then you can change it to the negative. It is important for us to have achievable goals and I think the most achievable goal is more user-friendly apps.
That’s fair. But the pointed question to ask would be – putting aside that at least 95% of people are coming on through KYC exchanges and considering that you have to figure out how to store it, how to use it properly, get familiar with mixers, all of these steps that you cannot mess up once – is privacy on Bitcoin a dead end even with apps?
I get where you’re going with this.
First of all, it’s important to make a distinction between mixers and CoinJoin. Mixers to me are centralized custodial services where you send someone bitcoin and they send you new bitcoin.
Coinjoin Is A Collaborative Transaction: when you have multiple people sending a transaction together to help break the probability-analysis that chain-surveillance companies do. As a result, it’s a native bitcoin send transaction.
So obviously there’s been a long history of custodial mixers being deemed illegal specifically by the U.S. government (and others). There’s been no such cases with CoinJoin, but I am not necessarily the most optimistic person in terms of what our legal rights will be going forward.
There might be issues in terms of using bitcoin privately – with regulated services – and that’s just unavoidable because the issue is on the regulated banking side. To me, that is a short-term adoption growing pain while people are actually still connected to the traditional financial system.
In the future, ideally, you are looking at a bitcoin circular economy. People are not going to be buying bitcoin, they are going to be earning bitcoin through their jobs. They are not going to be selling bitcoin, they are going to be spending bitcoin. All of a sudden, those regulated entities that are attached to the banking system are way less crucial.
Do People Actually Care Enough About Privacy?
There are a lot of good arguments that they do not, that they could not give two [rhymes with “mitts”]. I mean, they have Alexa in their house. They have Google Home in their house. They have a smartwatch on their wrist. They are sending their DNA out to companies. There are plenty of examples of the overwhelming majority of people trading convenience for security and privacy.
There is a bright side with things like Signal or iMessage, which bridge the gap between the trade-offs of encryption and convenience. Bitcoiners should study Signal’s adoption – how they polished it as much as possible while providing good privacy guarantees.
You want to make it as convenient as possible to reduce friction for people’s needs. It cannot be much more expensive or more difficult than a regular bitcoin transaction. Ideally, it could be cheaper.
My most optimistic take on privacy sounds really pessimistic. We have never been in a world that is so digital and open to corporate and government surveillance.
What is going to happen is as more of our lives are online, we are going to see more and more leaks, hacks and compromises that put people at risk. As that happens, people will get burned, and when they get burned, they will seek out better alternatives.
At that point, it is important we have the tools and resources available for them so they can actually execute on that plan. But unfortunately, I think the majority of people will not wake up until they get burned.
Why Haven’t CoinJoins Become More Popular?
I think, first of all, there has been a decent amount of traction. It has not been a miserable failure. Small steps, right? The overwhelming majority of people are not using CoinJoin. I think there are a couple of reasons. First, it is significantly more expensive than a regular native bitcoin transaction.
Second, it is not exactly intuitive. The required tools are getting built and they are already much more user-friendly than they were a year ago. The team at Samourai Wallet has done a great job making using bitcoin privately much easier. Like everything else, it is a matter of reducing friction whether that’s cost or UX.
The third thing is a lot of people are just not actually transacting in bitcoin. No one is sending bitcoin privately or receiving bitcoin privately because they are just buying and holding. And of that subset, a lot of people are just onboarding directly onto custodial services, and they are not actually even taking custody themselves.
So if we’re going to talk about increasing CoinJoin adoption, you have to get people to actually send and receive bitcoin first.
What Do You Make Of The Fungibility Concerns About “Washed Coins?”
That is another point. There is a lot of fear, uncertainty and doubt surrounding CoinJoin. If people are in the short-term fiat game, they are thinking about whether or not they can sell their bitcoin in the future on a regulated service. That is a reasonable concern – that they are not going to be able to sell bitcoin with a CoinJoin history.
Personally, I think that is a short-term fear. Long term, if we cannot spend bitcoin with the CoinJoin history, then Bitcoin in general is going to have larger problems than your individual stack. Bitcoin would have basically failed at that point.
Why Is That?
It is a matter of fungibility. If you did a CoinJoin eight hops ago or received bitcoin with an UTXO [unspent transaction output] 10 hops ago – is that coin “nonspendable?” If I am a shop owner and accept bitcoin, do I have to [survey] you to make sure that it’s the right bitcoin or something?
In the short term – if you are a trader – I completely respect the viewpoint that CoinJoin is not for you. Keep your options open. But I am not in it for trading bitcoin – it is a long-term game of accumulation. I think you should operate under the assumption that you are never going to sell on a regulated exchange and will spend it eventually. If that is the viewpoint, then it is not a real concern.
This reminds me of Kevin O’Leary’s thoughts on “clean” and “dirty” bitcoin, where he thinks institutions will only want to deal with environmentally-neutral coins. But white and black markets can spring up in a lot of ways – FATF-compliant crypto, crypto tied to hacks. Isn’t this inevitable?
You know, in 2013, there was a big push for merchant adoption, but it was done in a nonproductive way. Regulated startups like BitPay came in, offered companies the ability to accept bitcoin and immediately sell it for fiat. The whole thing was centralized and regulated.
You were not really using bitcoin; you were selling it to a third party to buy goods and services in fiat. To me that’s not a proper circular economy.
Something like BTCPay Server that allows everyone to, in a sovereign way, accept bitcoin themselves with open source software rather than outsource it is an absolute game changer. We are seeing other open source projects like Satsale and CypherpunkPay emerge that provide this very easy to use open source stack to receive bitcoin.
All of a sudden merchants around the world can accept bitcoin without KYC requirements, without banking relationships and might even be able to accept bitcoin in situations where they cannot accept fiat.
There are probably more merchants than you would think that want to receive bitcoin. They are the type that will not immediately sell for fiat and want bitcoin in a sovereign way without taking on intimate KYC information.
There are businesses that want to stack sats [i.e., slowly accumulate bitcoin in small amounts] – so they offer discounts for payments in bitcoin or even refuse fiat. If you want to buy a Nodl [a bitcoin hardware product], you have to pay in bitcoin. You cannot get it any other way.
As things start to emerge, we will see more and more people using bitcoin in a slow, organic way. Bitcoin is ultimately a permissionless open system, there is really no way to force people to use it. People will find the need and will start to use it more.
That’s The Circular Economy. If You Really Want To Make It Happen, Shouldn’t You Similarly Resist Accepting KYC Bitcoin In The Same Way That Kevin O’leary Won’t Touch Contaminated Coins?
Ultimately, whether or not people want to use KYC services to onboard onto Bitcoin is a personal decision. Bitcoin is a system that relies on personal responsibility, and people should make their own decisions based on their own personal situation.
My biggest issue with KYC right now is that I do not think the trade-offs are very clear to people who are onboarding and using it. I don’t think they realize that KYC is forever and that there will always be a record of how much bitcoin you purchased, when you bought it and where you sent it. All that can be used going forward or backwards to track you on-chain. So users should be aware of that.
It is very much a personal issue because it puts users at risk of theft, extortion and persecution. If an authoritarian government knows you bought bitcoin, they could put you in jail or seize your coins. Or if your KYC information leaks, malicious criminals might try to rob or extort you.
We’re seeing so many newcomers come in and sign up for like eight different services – they are sending their passport and selfies to all these different places that are all secured horribly.
Have You Considered Zcash Or Monero?
I think Zcash is just a dead-end project. There’s concerns about the math being overly complicated. They had an inflation bug that took a while to detect. And I think even to this day, [people] are not 100% sure if it is compromised.
Worse, it was a situation where two or three people knew about it while they were trying to patch it – this undetectable bug – so you have that centralization risk. But besides the math, it is a U.S.-based company with U.S.-based VCs that have a massive amount of influence on it that still takes out a pre-mined reward every block. To my mind, that is a complete disqualifier.
Monero, on the other hand, is novel and unique and can provide very good transactional privacy. But there’s two things here. First, long term, I expect bitcoin to significantly outperform monero with respect to purchasing power.
Monero is less hard money because you do not have the ability to verify its supply without trusting complicated math assumptions. You cannot have both – there is a trade-off and they went with privacy. So, as a result, money will flow to the harder money, which is bitcoin.
The funny thing is, because monero is getting removed from regulated exchanges – they have made it easy to swap with bitcoin. Instead of relying on regulated exchanges, they rely on bitcoin as their on-ramp and off-ramp.
That means bitcoin users today can easily swap into monero basically as a private sidechain for transactions. It is a utility token but because XMR is trending to zero against bitcoin, there is no reason for you to hold the actual token long term.
That’s especially true once real privacy solutions are solved in Bitcoin, so to me both projects are flawed long term but for different reasons.
I’m about 90% of the way to being a bitcoiner, but it seems like there’s always a lot of solutionism [and widespread assumption] that problems – be they privacy, environmental, the fee economy – will always have a solution eventually. Why not be more pragmatic and use the worse tools for the better today?
There is a disconnect there, right? It’s something that is very frustrating to me about the bitcoin world, and it is not just a privacy thing. You normally will not hear a developer say anything like that, but on Bitcoin Twitter, you hear it all the time, “oh, this will fix it. We’ll figure it out.”
The privacy world in general cares more about practical solutions today because it is a real- world situation today. It is something that we absolutely need today. I do wish that there was more priority placed on some of these pressing issues but expect more people to get burned before the need for better privacy tools is realized.
Monero’s XMR, Zcash’s ZEC Jump As Privacy Coins Gain Favor
Crypto exchanges blocking known addresses could lead to a demand for privacy cryptos among investors, one analyst said.
Tokens of the privacy-focused cryptocurrencies of Monero, Zcash and Secret were among the biggest gainers in the past 24 hours as the crypto market bounced from Tuesday’s support levels to add more than 6% to total market capitalization. The moves were among the largest for privacy tokens in recent months.
Monero’s XMR gained more than 25% in the past 24 hours, spiking as high as $277 on Binance before falling back to $196 at the time writing. Zcash’s ZEC and Secret’s SCRT increased 16% in the same period, reaching prices not seen since late January.
Price-chart analysis suggests XMR could fall to a support level at $180, while ZEC and SCRT could drop from their current $137 and $5 to $129 and $4.20, respectively.
Some analysts say masking a user’s wallet address and identity could play a role in increasing investor demand for privacy coins.
“With the quality of shielding the identity and details of transactions, many crypto users still believe privacy coins help enshrine the core tenets of blockchain transactions,” Alexander Mamasidikov, a co-founder of crypto bank MinePlex, wrote in an email to CoinDesk.
“The tokens have inherent qualities and use cases that many investors believe will also stir an increase in their demand across the board,” he said.
Monero and Zcash, unlike bitcoin or ether, use a cryptographic process to ensure that transactions cannot be linked to wallet holders and are untraceable.
Such an arrangement is helpful to some users in the current environment: Exchanges like Coinbase blocked over 25,000 crypto addresses linked to illicit activity on Sunday, as reported.
Crypto exchanges have been under pressure to monitor Russia-linked crypto activity, especially as the country faces sanctions from western countries following its invasion of Ukraine. The sanctions include blocking funding to Russian businesses and entities, as well as avoiding purchases of Russian products and commodities.
Demand For Privacy Cryptos
Privacy coins have seen declining interest from investors in recent years as narratives in crypto circles shifted away from privacy to decentralized finance (DeFi) – which uses smart contracts for the development of financial services – and non-fungible tokens (NFT).
Layer 1, or base, blockchains like Terra, Cosmos and Avalanche have been another investor favorite for the scalability, speed, and affordability they provide to users. Their tokens have been among the highest gaining cryptos in the past two years.
But the war in Ukraine and resultant sanctions might have pulled some of the focus back toward privacy coins, some say.
“With some crypto exchanges announcing that they are blocking a large number of wallets many users that have normally nothing to hide or fear may still want to protect their assets,” Alexander Tkachenko, founder of VNX, said in a Telegram message. “During turbulent times safety assets like physical gold and privacy coins get large inflows of capital.”
Gold neared $2,000 on Wednesday, a level last seen in September 2020. The increase came amid a broader run in metals and commodities. Nickel jumped to $101,000 on Tuesday morning, while Brent oil touched nearly $140 a barrel.
Updated: 3-10-2022
FTX Joins Other Crypto Goliaths To Promote Autonomy Over Sensitive Information
FTX and Alkemi add to the list of 14 crypto companies partnered with Verite, including Coinbase, Circle, Hedera Hashgraph, Ledger, Solana Foundation and more.
Centre, an open-source technology project developed by Coinbase and Circle, has onboarded crypto exchange FTX and Alkemi Network as its latest partners to collaborate on Verite. Verite is a set of shared decentralized identity protocols — developed by Centre — to empower crypto-centric individuals and businesses by granting total control of personal information.
Supporting Verite’s commitment to collaborate on shared decentralized identity standards, FTX and Alkemi have added to the list of 14 crypto companies, which include Coinbase, Circle, Hedera Hashgraph, Ledger, the Solana Foundation and more.
Verite launch partners include @circlepay , @blocks, @Algorand, @coinbase, @compoundfinance, @ConsenSys, Espresso Systems, @hedera, @Ledger, @MMInstitutional, @phantom, @SolanaFndn, @SpruceID, and @StellarOrg
— CENTRE (@centre_io) February 17, 2022
Verite protocols are designed to help people and businesses keep track of their personal information and provide total control over how businesses use this information in the crypto economy. According to the company:
“Verite is returning autonomy over sensitive information to the individual while continuing to enable businesses to interact with identity-verified participants.”
Verite makes this possible by allowing users to cryptographically prove claims about their identities and carry those claims in the same crypto wallets where they store their digital assets. Centre CEO David Puth stated:
“We are pleased that our partners share our conviction that Verite’s identity standards will create a new level of clarity, privacy, and convenience to everyone transacting in the crypto economy.”
According to the announcement, Verite’s protocol integration into smart contracts, applications and websites does not introduce single-vendor or anti-competitive dependencies:
“Individuals will be able to use their credentials across the crypto ecosystem, making digital assets far more accessible to both crypto natives and novices.”
On Tuesday, FTX also expanded its crypto services into Europe soon after receiving regulatory approval from the Cyprus Securities and Exchange Commission.
Want to know where FTX is licensed and regulated?
Check out https://t.co/50ELyIX1cd!
The list is growing every week.
— SBF (@SBF_FTX) March 8, 2022
As Cointelegraph reported, Switzerland-based FTX Europe will serve European crypto clients through a licensed investment firm across the European Economic Area.
Updated: 3-11-2022
CoinSwap’s Privacy Technique Makes Bitcoin Transactions Invisible
The alpha release of Teleport implements the CoinSwap privacy technique in an effort to improve bitcoin privacy by making transactions “invisible.”
Developers have long been working on making Bitcoin more private because every bitcoin (BTC) transaction ever sent is stored in the blockchain, which anyone can see. Last week, Bitcoin privacy programmer Chris Belcher released an alpha version of Teleport, an implementation of privacy technique “CoinSwap,” in an effort to improve bitcoin privacy by making transactions “invisible.”
The first version of the open-source project is not ready for real funds because it needs more testing, Belcher said in the announcement on the Bitcoin developer email list. It’s also missing the key features needed to fully make transactions invisible. But the release shows CoinSwap, a long-standing idea – first described by cryptographer Gregory Maxwell on the Bitcointalk forum in 2013 – finally coming to life.
Belcher believes Teleport’s CoinSwap has advantages over CoinJoins, the main privacy-preserving mechanism used today by projects Wasabi, Samourai and JoinMarket. “Imagine a new privacy tech for bitcoin, like CoinJoin, but can’t be blocked [because] the [transactions] look exactly the same as regular [transactions],” Belcher wrote on Twitter.
Why ‘Teleport’ Your Bitcoin?
Today, privacy-conscious users take advantage of the wallets Wasabi and Samourai to execute CoinJoins, which scramble a user’s bitcoin with many other users’ bitcoins, obscuring the coins’ tracks.
The problem is that even if CoinJoins obscure where a user’s bitcoin is sent, fooling blockchain surveillers, it’s still obvious from a glance at the bitcoin blockchain that a CoinJoin has taken place.
If done the right way, CoinSwap transactions, on the other hand, can’t be detected on the blockchain. They look just like normal transactions.
“Imagine a future where a user, Alice, has bitcoins and wants to send them with maximal privacy, so she creates a special kind of transaction. For anyone looking at the blockchain her transaction appears completely normal with her coins seemingly going from address A to address B. But in reality her coins end up in address Z, which is entirely unconnected to either A or B,” Belcher writes. In a sense, the transaction is being “teleported” elsewhere, hence the project’s name “Teleport.”
Even users who don’t use CoinSwap can benefit from it.
“If even a small percentage of transactions were actually created by this software, anybody doing analysis on the blockchain would always have a niggle in the back of their mind: ‘What if this transaction I’m looking at was actually a CoinSwap? How would I know? What if these coins have actually disappeared into the mist?”” Belcher writes.
“The doubt and uncertainty added to every transaction would greatly boost the fungibility of bitcoin and so make it a better form of money,” Belcher added.
“Fungibility” is an important property of money, meaning that each unit can be exchanged for any other unit for exactly the same value. We take for granted that a dollar is worth just as much as any other dollar, for instance.
Privacy is crucial to preserving fungibility because without it some bitcoins can become “tainted” if they are used as part of criminal activity, for example. Then, there’s a possibility that an unwitting, non-criminal user receives the tainted coins, only to discover they are harder to trade (and therefore worth less) because of their historical association with a criminal or sanctioned event.
Next Steps For ‘Invisibility’
While it’s now possible to execute CoinSwaps using Teleport, the software doesn’t make the CoinSwap transactions look like normal transactions just yet.
That’s the next “really big task” on Belcher’s to-do list. The cryptographic technique ECDSA-2P can be used to make these transactions look like normal “single-sig” addresses, which are “overwhelmingly common out there and so provide an enormous anonymity set,” he writes.
When it comes to Taproot implementation, however, Teleport will have to wait. The Taproot upgrade to Bitcoin, which happened in November 2021, adds Schnorr signatures as an option beyond ECDSA signatures, which are how most transactions are signed today.
While Schnorr signatures can do the same thing as ECDSA-2P in an easier way, Belcher argues that Schnorr isn’t suitable for CoinSwap. “This is because the anonymity set for ECDSA would be much greater. All addresses today are ECDSA and none are Schnorr,” Belcher explained when he originally announced the project in 2020.
As such, Belcher suggested it might take years before there would be enough of a dataset to make the use of Schnorr in CoinSwaps practicable. But Bitcoin users need privacy much sooner than that.
This alpha release isn’t ready for prime time, but developers are invited to test the open-source software if they want to help battle-test it, by using dummy coins on the test and signet networks. “It is possible to run it on mainnet, but only the brave will attempt that, and only with small amounts,” Belcher writes.
Longer term, when the project is ready for real funds, he hopes users and wallets will take advantage of the improved privacy it provides.
“My aim is that the Teleport project will develop into a practical and secure project on the bitcoin mainnet, usable either standalone as a kind of bitcoin mixing app, or as a library that existing wallets will implement allowing their users with the touch of a button to send bitcoin CoinSwap transactions with much greater privacy than was possible before,” he said.
Mina Foundation Raises $92M To Accelerate Adoption of Zero-Knowledge Proofs
The terms of the token sale were not disclosed but FTX Ventures and Three Arrows Capital led the effort.
Zero-knowledge proofs took a step forward Thursday with a $92 million token sale to accelerate adoption for the Mina protocol.
The round was led by FTX Ventures and Three Arrows Capital, with the raise representing FTX Venture’s first investment in a zero-knowledge project.
Other participants include Alan Howard, Amber Group, Blockchain.com, Brevan Howard, Circle Ventures, Finality Capital Partners and Pantera.
“The main opportunity here is to be able to program with zero knowledge for regular developers,” Mina Foundation CEO Evan Shapiro said in an interview with CoinDesk.
He added: “Historically, this hasn’t been possible. You had to be a cryptographer that also happened to be super good at the kinds of programming you need to work with zero-knowledge proofs. What makes this exciting is any developer who knows JavaScript can now work with ZK proofs.”
Shapiro declined to share the price at which the tokens were sold or the percentage of the Mina Foundation treasury the round represents.
Grant Program
According to Shapiro, the network soft-launched in December 2021, and the team has been slowly raising production ever since.
“The main function of the raise is to increase our capacity to give out grants to proposals that can help support the protocol,” he said.
So far, “1,100 or so” grantees have received funds, and the team saw over 100 applications for its “ZK Bootcamp” application development program, of which the foundation selected a dozen to nurture.
An identity solution, multiple games and a “highly scalable layer 2” system count among the first cohort, and Shapiro said he expects to see many of them reach production within the next six months.
Other promising zero-knowledge applications include “a [decentralized finance] app that has a form of identity of private [know your customer],” private decentralized autonomous organization (DAO) transactions and memberships, and private non-fungible token (NFT) ownership – all of which are frequently requested features among users and developers.
“This is a special moment where zero-knowledge proofs are becoming something that people can generally use, and not just select developers. That’s an exciting thing for Mina and for the space,” Shapiro said.
Updated: 8-17-2022
Pushing Bitcoin To Become More Scalable With Zero-Knowledge Proofs
Cointelegraph Research explains the EC-STARKs technology and discusses what this means for the cryptocurrency market.
For all the good that Bitcoin brings to the table, it also possesses a commonly accepted issue in scalability. Bitcoin can only process a limited number of transactions per block and, as of Aug. 17, 2022, can handle about five transactions per second, which in comparison to most other blockchains is low.
The factor limiting scalability lies in Bitcoin’s cryptographic algorithm.
The Elliptic Curve Digital Signature Algorithm (ECDSA) is the essential cryptographic algorithm that powers Bitcoin and ensures that only the rightful owner can access and manage their funds.
Currently, verification of the ECDSA, a Bitcoin signature allowing to carry out transactions and send Bitcoin, is not efficient and limits the scalability of the Bitcoin blockchain.
A potential solution is using zero-knowledge proof (ZKP) technology, allowing higher degrees of privacy and security.
A recent Starkware paper presents the method for efficiently verifying ECDSA from within the STARK ecosystem, potentially resolving the blockchain trilemma for Bitcoin — i.e., achieving scalability, security and decentralization simultaneously.
Foundations Of The Technology
A ZKP is a cryptographic technique that enables the prover to confirm another person’s claim without supporting data. ZKPs are cryptographic protocols that keep third parties away from users’ privacy.
ZKPs can also be a helpful building block for many cryptographic protocols, ensuring participants follow the protocol’s specifications.
Privacy and scalability are enhanced with ZKPs because only certain data is revealed and transacted without disclosing all the information that needs to be proven.
Based on the ZKP technology, STARKs, or Scalable Transparent Argument of Knowledge — invented by Starkware — is a type of cryptographic proof technology that makes it possible to communicate data with a third party — e.g., sign transactions without revealing the data.
It also allows moving computations and storage of validated data off-chain, thus increasing scalability.
STARKs is a quantum-resistant system based on hash functions used by Ethereum, not elliptic curves utilized by Bitcoin.
Importantly, STARKs systems are considered more advanced than their predecessors, zk-SNARKs, and can resist attacks from quantum computers.
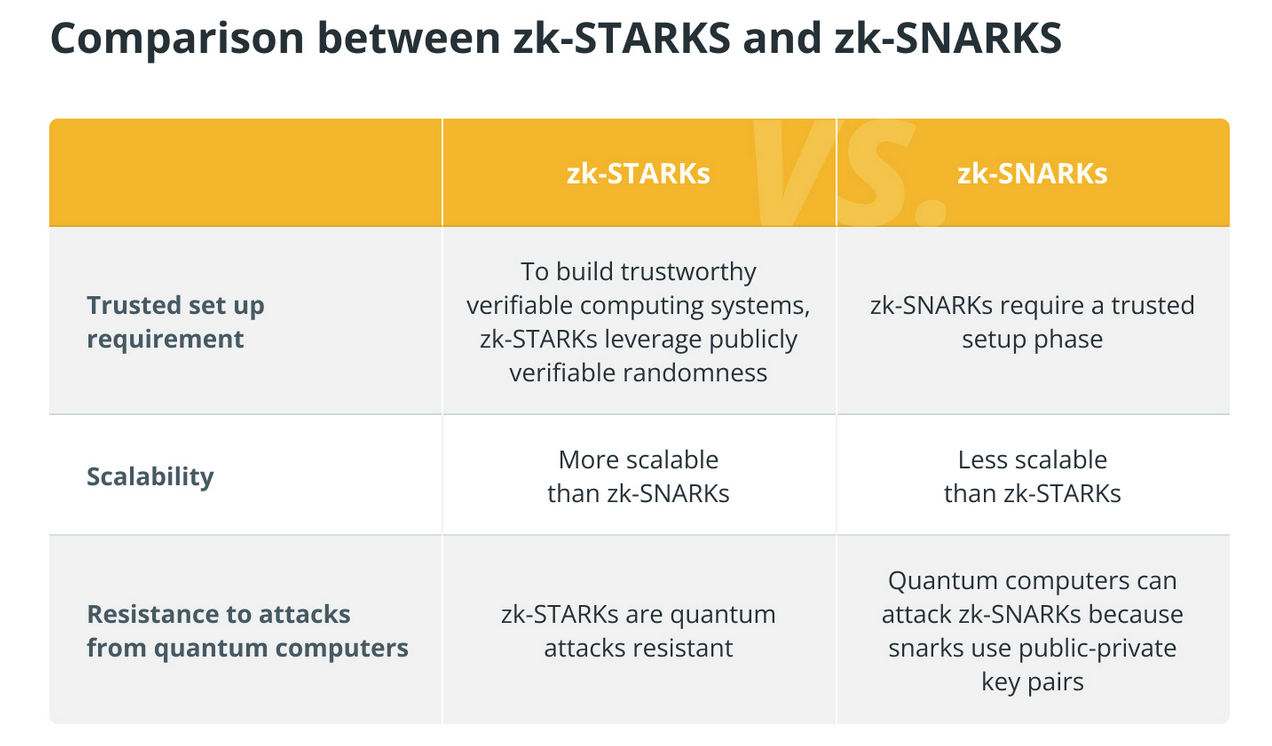
EC-STARKs: The Next Step In Bitcoin’s Scalability?
Earlier, Starkware announced governance token issuance for its StarkNet — a decentralized permissionless STARK-based validity rollup that operates as an Ethereum layer-2 chain — to decentralize the network further and maintain STARK technology as a public good.
However, Ethereum’s underlying storage cost constraints the scalability advantages of the technology. However, its application for the Bitcoin blockchain may present a better platform for decentralized applications in the near future.
EC-STARKs are the next generation of this technology, aiming to increase Bitcoin’s scalability and security by replacing hash functions with elliptic curves — i.e., making already-existing scalability solutions for Ethereum to be compatible with Bitcoin.
With EC-STARKs, one can run an off-chain protocol for Bitcoin and keep proofs in STARK. Simply put, Bitcoin can be emulated inside STARK, allowing highly sophisticated protocols to be built on Bitcoin-backed tokens with the same elliptic curve keys.
Thus, utilizing this technology may not only increase the scalability of Bitcoin but serve as the gateway for developers to create DApps on Bitcoin, potentially creating a rival for Ethereum.
Updated: 2-16-2023
European Union Discusses Using Zero-Knowledge Proofs For Digital IDs
The proposition to use zero-knowledge proofs was approved by the EU Committee and may become part of the updated legislation.
The European Union is famous for its ambivalent relationship with privacy — on the one hand, it was the first place in the world to apply strict data protection regulations.
On the other, its central bank digital currency (CBDC) project lacks the anonymity standards of private cryptocurrencies.
Nevertheless, last week EU lawmakers made a vital step to embrace privacy in the space of citizens’ digital identities. On Feb. 9, the Industry, Research and Energy Committee included the standard of zero-knowledge proofs in its amendments to the European digital identity framework (eID).
The latest update was voted in by 55 votes to 8 in the committee — the draft will now proceed to the trilogue phase of negotiations.
While the latest draft is still not available publicly, the press release specifies that EU citizens would be granted full control of their data, with the option to decide what information to share and with whom:
“The new eID would allow citizens to identify and authenticate themselves online (via a European digital identity wallet) without having to resort to commercial providers, as is the case today – a practice that raised trust, security and privacy concerns.”
As Jonas Fredriksen, The Senior Director For EU Government Affairs At Circle Has Noted On Twitter:
“The proposal would facilitate the emergence of new business models and opportunities in the digital economy, as companies develop innovative products and services that rely on zero-knowledge proofs and eID solutions.”
Zero-knowledge proofs have recently been at the center of researchers’ attention as a possible means to ensure regulatory compliance and privacy in digital currencies.
The joint paper by the San Francisco-based Mina Foundation, operator of the Mina Protocol; German Hauck Aufhäuser Lampe bank; and the Interdisciplinary Centre for Security, Reliability and Trust of the University of Luxembourg showed how exactly the zero proofs could be connected to Europe’s eIDAS electronic identity system.
However, not everyone is convinced by that solution. Writing for Cointelegraph, Balázs Némethi, the CEO of Veri Labs and a co-founder of kycDAO, claimed that when proofs alone are insufficient and personal information sharing between the participants of a transaction is essential, relying only on off-chain solutions is advised.
Updated: 3-28-2023
Zero-Knowledge Proofs Coming To Bitcoin, Overhauling Network State Validation
Zero-knowledge proofs have powered the development of Ethereum layer 2s, and now they’re coming to Bitcoin.
Bitcoin users will soon be able to use zero-knowledge proofs (ZK-proofs) to expedite the process of verifying individual blocks and, eventually, the entire blockchain.
ZeroSync Association, a Swiss-based nonprofit, is developing tooling which allows users to validate the state of the Bitcoin network without having to download the blockchain or trust a third party for verification.
ZeroSync was formed to develop and maintain open-source software that enables succinct ZK-proofs on the Bitcoin blockchain.
The group uses StarkWare’s proprietary Zero-Knowledge Scalable Transparent Argument of Knowledge (zk-STARK) validity proofs to generate ZK-proofs for the Bitcoin network.
The tool promises to overhaul the process of verifying the Bitcoin blockchain, which still requires node operators to download a large amount of data to synchronize the correct state of the Bitcoin network.
ZeroSync is using ZK-proofs to eventually generate valid proof and verify the latest state of the blockchain almost instantaneously.
ZK-proofs have been a revelation for the Ethereum ecosystem, with various proof methods powering several layer-2 scaling platforms, including Polygon, Arbitrum, Optimism and StarkNet.
An announcement from the ZeroSync Association highlights the promise of ZK-proofs for blockchain scalability and privacy by providing “almost-fixed-size” proofs verifying large computations.
The project’s work pioneers the application of ZK-proofs for the Bitcoin network, with the organization describes Bitcoin’s relative simplicity and the Unspent Transaction Output (UTXO) model as a unique value proposition for applying recursive proofs.
ZeroSync notes that the ZK-Proof tools do not require consensus changes or additional trust assumptions for the Bitcoin network and its users.
The organization is building a software development kit that will allow developers to generate custom validity proof for specific use cases without needing indepth domain expertise.
ZeroSync is in the process of building a client for fast initial block download as well as implementing the first complete proof of Bitcoin consensus. The client will allow users to sync a full node without making code changes to Bitcoin core.
ZeroSync is using the Cairo programming language, pioneered by StarkWare, to create STARK-provable programs for computations.
ZeroSync’s tool is currently in a prototype state but has the ability to prove the validity of individual assumed valid blocks, which verify all Bitcoin rules except for scripts.
The team also has a working in-browser demo verifier for STARK proofs of Bitcoin blocks.
The ZeroSync Association was initially funded by Geometry and StarkWare but is establishing a nonprofit entity to enable ongoing development and maintenance from stakeholders within the Bitcoin community.
A statement from StarkWare president and co-founder Eli Ben-Sasson, who co-invented zk-STARKS, summed up the magnitude of ZK-proofs coming to the Bitcoin ecosystem:
Lightning Labs, the team behind the Bitcoin layer-2 Lightning Network payment system, is a contributing partner to ZeroSync’s project.
The firm intends to use ZeroSync to power compressed transaction history proofs for its Taproot Asset Representation Overlay (Taro) protocol, which aims to power the issuance of digital assets on the Bitcoin blockchain.
Newly Formed ZeroSync Association Brings Zero-Knowledge Proofs To Bitcoin
The association has received sponsorship from crypto investment firm Geometry Research and StarkWare Industries, the software company behind layer 2 Ethereum zero-knowledge rollup scaling system StarkNet.
Three German computer scientists have created a Swiss nonprofit called the ZeroSync Association to help scale Bitcoin by using zero-knowledge proofs (zk-proofs), a cryptographic technique that has exploded in popularity on rival chain Ethereum.
Zero-knowledge proofs use cryptography to prove the validity of information without revealing the information itself. Using a zk-proof to validate the Bitcoin blockchain means nodes can sync almost instantly instead of taking hours (and sometimes days) to download the chain’s current 500 GB of data.
ZeroSync has already produced a working prototype that allows users to validate the state (who owns what right now) and transaction history of the Bitcoin blockchain without downloading the entire chain or trusting a third party.
The prototype can verify Bitcoin consensus rules but not transaction signatures. It’s also a bit clunky and still needs to be optimized for speed and security, so it’s not ready for prime time just yet, but the important thing is it works.
“It’s very much in the prototype stage,” ZeroSync co-founder Robin Linus told CoinDesk. “But the grand vision is that you download that one megabyte of proof and that is as good as if you had downloaded the 500 gigabytes.”
Light clients or simple payment verification (SPV) nodes have always existed on the Bitcoin blockchain. In fact, Satoshi Nakamoto mentioned the concept in the Bitcoin white paper. They are critical for small devices like mobile phones that can’t download the entire blockchain.
“It is possible to verify payments without running a full network node,” Satoshi wrote. “Verification is reliable as long as honest nodes control the network, but is more vulnerable if the network is overpowered by an attacker.”
ZeroSync goes a step further by verifying transactions via cryptographic proof rather than merely trusting honest nodes as suggested by Satoshi.
“You don’t have to trust. That is the entire point,” said Linus. “The proof proves it to you. That’s the great invention.”
A fully functioning zk-proof mechanism can be used to enable a wide range of applications outside of the flagship node syncing use case. ZeroSync has created a developer tool kit to enable applications like proof-of-reserves on exchanges and transaction history compression on second layer protocols like Lightning Labs’ Taro.
Linus and fellow co-founder Lukas George joined forces in July to work on implementing a full chain proof of the Bitcoin blockchain after George’s undergraduate thesis on implementing a proof of Bitcoin’s headers caught the attention of Geometry Research.
The team subsequently added Tino Steffens to the mix; all three co-founders have a background in computer science.
Linus was living in Santa Teresa, a remote beach town on Costa Rica’s Nicoya Peninsula that has one ATM machine with a 10 p.m. curfew. It drove Linus nuts and forced him to research alternative payment methods.
He stumbled upon Bitcoin, befriended the well-respected “Bitcoin sorcerer” Ruben Somsen (who coined the term “ZeroSync”), and the rest, as they say, is history.
“From there, I started to learn more and more about cryptography,” Linus said. “I developed some skills over time and then Ruben recommended me to Geometry Research. They offered me the opportunity to build STARK proofs for Bitcoin and that’s also how I got in touch with Lucas.”
Updated: 3-31-2023
ZeroSync And Blockstream To Broadcast Bitcoin Zero-Knowledge Proofs From Space

The partners say using zero-knowledge proofs will allow Bitcoin nodes to sync quickly from anywhere on earth, “even without Internet.”
Swiss non-profit ZeroSync Association and Bitcoin infrastructure firm Blockstream say they plan to broadcast Bitcoin zero-knowledge proofs – a type of cryptography that’s become one of 2023’s hottest blockchain-tech trends – from Blockstream’s satellite.
Using zk-proofs to validate the Bitcoin blockchain means nodes don’t have to download the chain’s current 500GB of data and can therefore sync in fractions of a second instead of hours or days.
We’re excited to announce that today @adam3us, CEO of @Blockstream, agreed to partner with @ZeroSync_ to broadcast #Bitcoin ZK chain proofs via Blockstream Satellite!
Fast sync from everywhere. Even without internet.
🚀🚀🚀🌎https://t.co/1ypzZOkQfq@StarkWareLtd @EliBenSasson pic.twitter.com/kcQpdP0YEt— ZeroSync (@ZeroSync_) March 31, 2023
Blockstream’s satellite network provides free global access to Bitcoin by broadcasting the blockchain to the entire planet, including areas with unreliable Internet coverage. ZeroSync expects the first experimental broadcast to take place by the end of the year.
The newly-formed ZeroSync Association was launched on Tuesday and plans to help scale Bitcoin by using zero-knowledge proofs (zk-proofs), a cryptographic technique to prove the validity of information without revealing the information itself.
“The security of Bitcoin requires every participant to verify every transaction,” ZeroSync co-founder Robin Linus told CoinDesk. “That didn’t scale well until now. Proof systems like STARKs have been invented. Applying them to generate a proof of Bitcoin’s chain state, and broadcasting it via satellite, can bring Bitcoin to almost everyone in the world. Don’t trust, verify.”
Related Articles:
Bitcoin Information & Resources (#GotBitcoin?)
US Deficit Will Be At Least 6 Times Bitcoin Market Cap — Every Year (#GotBitcoin?)
Central Banks Warm To Issuing Digital Currencies (#GotBitcoin?)
Meet The Crypto Angel Investor Running For Congress In Nevada (#GotBitcoin?)
Introducing BTCPay Vault – Use Any Hardware Wallet With BTCPay And Its Full Node (#GotBitcoin?)
How Not To Lose Your Coins In 2020: Alternative Recovery Methods (#GotBitcoin?)
H.R.5635 – Virtual Currency Tax Fairness Act of 2020 ($200.00 Limit) 116th Congress (2019-2020)
Adam Back On Satoshi Emails, Privacy Concerns And Bitcoin’s Early Days
The Prospect of Using Bitcoin To Build A New International Monetary System Is Getting Real
How To Raise Funds For Australia Wildfire Relief Efforts (Using Bitcoin And/Or Fiat )
Former Regulator Known As ‘Crypto Dad’ To Launch Digital-Dollar Think Tank (#GotBitcoin?)
Currency ‘Cold War’ Takes Center Stage At Pre-Davos Crypto Confab (#GotBitcoin?)
A Blockchain-Secured Home Security Camera Won Innovation Awards At CES 2020 Las Vegas
Bitcoin’s Had A Sensational 11 Years (#GotBitcoin?)
Sergey Nazarov And The Creation Of A Decentralized Network Of Oracles
Google Suspends MetaMask From Its Play App Store, Citing “Deceptive Services”
Christmas Shopping: Where To Buy With Crypto This Festive Season
At 8,990,000% Gains, Bitcoin Dwarfs All Other Investments This Decade
Coinbase CEO Armstrong Wins Patent For Tech Allowing Users To Email Bitcoin
Bitcoin Has Got Society To Think About The Nature Of Money
How DeFi Goes Mainstream In 2020: Focus On Usability (#GotBitcoin?)
Dissidents And Activists Have A Lot To Gain From Bitcoin, If Only They Knew It (#GotBitcoin?)
At A Refugee Camp In Iraq, A 16-Year-Old Syrian Is Teaching Crypto Basics
Bitclub Scheme Busted In The US, Promising High Returns From Mining
Bitcoin Advertised On French National TV
Germany: New Proposed Law Would Legalize Banks Holding Bitcoin
How To Earn And Spend Bitcoin On Black Friday 2019
The Ultimate List of Bitcoin Developments And Accomplishments
Charities Put A Bitcoin Twist On Giving Tuesday
Family Offices Finally Accept The Benefits of Investing In Bitcoin
An Army Of Bitcoin Devs Is Battle-Testing Upgrades To Privacy And Scaling
Bitcoin ‘Carry Trade’ Can Net Annual Gains With Little Risk, Says PlanB
Max Keiser: Bitcoin’s ‘Self-Settlement’ Is A Revolution Against Dollar
Blockchain Can And Will Replace The IRS
China Seizes The Blockchain Opportunity. How Should The US Respond? (#GotBitcoin?)
Jack Dorsey: You Can Buy A Fraction Of Berkshire Stock Or ‘Stack Sats’
Bitcoin Price Skyrockets $500 In Minutes As Bakkt BTC Contracts Hit Highs
Bitcoin’s Irreversibility Challenges International Private Law: Legal Scholar
Bitcoin Has Already Reached 40% Of Average Fiat Currency Lifespan
Yes, Even Bitcoin HODLers Can Lose Money In The Long-Term: Here’s How (#GotBitcoin?)
Unicef To Accept Donations In Bitcoin (#GotBitcoin?)
Former Prosecutor Asked To “Shut Down Bitcoin” And Is Now Face Of Crypto VC Investing (#GotBitcoin?)
Switzerland’s ‘Crypto Valley’ Is Bringing Blockchain To Zurich
Next Bitcoin Halving May Not Lead To Bull Market, Says Bitmain CEO
Bitcoin Developer Amir Taaki, “We Can Crash National Economies” (#GotBitcoin?)
Veteran Crypto And Stocks Trader Shares 6 Ways To Invest And Get Rich
Is Chainlink Blazing A Trail Independent Of Bitcoin?
Nearly $10 Billion In BTC Is Held In Wallets Of 8 Crypto Exchanges (#GotBitcoin?)
SEC Enters Settlement Talks With Alleged Fraudulent Firm Veritaseum (#GotBitcoin?)
Blockstream’s Samson Mow: Bitcoin’s Block Size Already ‘Too Big’
Attorneys Seek Bank Of Ireland Execs’ Testimony Against OneCoin Scammer (#GotBitcoin?)
OpenLibra Plans To Launch Permissionless Fork Of Facebook’s Stablecoin (#GotBitcoin?)
Tiny $217 Options Trade On Bitcoin Blockchain Could Be Wall Street’s Death Knell (#GotBitcoin?)
Class Action Accuses Tether And Bitfinex Of Market Manipulation (#GotBitcoin?)
Sharia Goldbugs: How ISIS Created A Currency For World Domination (#GotBitcoin?)
Bitcoin Eyes Demand As Hong Kong Protestors Announce Bank Run (#GotBitcoin?)
How To Securely Transfer Crypto To Your Heirs
‘Gold-Backed’ Crypto Token Promoter Karatbars Investigated By Florida Regulators (#GotBitcoin?)
Crypto News From The Spanish-Speaking World (#GotBitcoin?)
Financial Services Giant Morningstar To Offer Ratings For Crypto Assets (#GotBitcoin?)
‘Gold-Backed’ Crypto Token Promoter Karatbars Investigated By Florida Regulators (#GotBitcoin?)
The Original Sins Of Cryptocurrencies (#GotBitcoin?)
Bitcoin Is The Fraud? JPMorgan Metals Desk Fixed Gold Prices For Years (#GotBitcoin?)
Israeli Startup That Allows Offline Crypto Transactions Secures $4M (#GotBitcoin?)
[PSA] Non-genuine Trezor One Devices Spotted (#GotBitcoin?)
Bitcoin Stronger Than Ever But No One Seems To Care: Google Trends (#GotBitcoin?)
First-Ever SEC-Qualified Token Offering In US Raises $23 Million (#GotBitcoin?)
You Can Now Prove A Whole Blockchain With One Math Problem – Really
Crypto Mining Supply Fails To Meet Market Demand In Q2: TokenInsight
$2 Billion Lost In Mt. Gox Bitcoin Hack Can Be Recovered, Lawyer Claims (#GotBitcoin?)
Fed Chair Says Agency Monitoring Crypto But Not Developing Its Own (#GotBitcoin?)
Wesley Snipes Is Launching A Tokenized $25 Million Movie Fund (#GotBitcoin?)
Mystery 94K BTC Transaction Becomes Richest Non-Exchange Address (#GotBitcoin?)
A Crypto Fix For A Broken International Monetary System (#GotBitcoin?)
Four Out Of Five Top Bitcoin QR Code Generators Are Scams: Report (#GotBitcoin?)
Waves Platform And The Abyss To Jointly Launch Blockchain-Based Games Marketplace (#GotBitcoin?)
Bitmain Ramps Up Power And Efficiency With New Bitcoin Mining Machine (#GotBitcoin?)
Ledger Live Now Supports Over 1,250 Ethereum-Based ERC-20 Tokens (#GotBitcoin?)
Miss Finland: Bitcoin’s Risk Keeps Most Women Away From Cryptocurrency (#GotBitcoin?)
Artist Akon Loves BTC And Says, “It’s Controlled By The People” (#GotBitcoin?)
Ledger Live Now Supports Over 1,250 Ethereum-Based ERC-20 Tokens (#GotBitcoin?)
Co-Founder Of LinkedIn Presents Crypto Rap Video: Hamilton Vs. Satoshi (#GotBitcoin?)
Crypto Insurance Market To Grow, Lloyd’s Of London And Aon To Lead (#GotBitcoin?)
No ‘AltSeason’ Until Bitcoin Breaks $20K, Says Hedge Fund Manager (#GotBitcoin?)
NSA Working To Develop Quantum-Resistant Cryptocurrency: Report (#GotBitcoin?)
Custody Provider Legacy Trust Launches Crypto Pension Plan (#GotBitcoin?)
Vaneck, SolidX To Offer Limited Bitcoin ETF For Institutions Via Exemption (#GotBitcoin?)
Russell Okung: From NFL Superstar To Bitcoin Educator In 2 Years (#GotBitcoin?)
Bitcoin Miners Made $14 Billion To Date Securing The Network (#GotBitcoin?)
Why Does Amazon Want To Hire Blockchain Experts For Its Ads Division?
Argentina’s Economy Is In A Technical Default (#GotBitcoin?)
Blockchain-Based Fractional Ownership Used To Sell High-End Art (#GotBitcoin?)
Portugal Tax Authority: Bitcoin Trading And Payments Are Tax-Free (#GotBitcoin?)
Bitcoin ‘Failed Safe Haven Test’ After 7% Drop, Peter Schiff Gloats (#GotBitcoin?)
Bitcoin Dev Reveals Multisig UI Teaser For Hardware Wallets, Full Nodes (#GotBitcoin?)
Bitcoin Price: $10K Holds For Now As 50% Of CME Futures Set To Expire (#GotBitcoin?)
Bitcoin Realized Market Cap Hits $100 Billion For The First Time (#GotBitcoin?)
Stablecoins Begin To Look Beyond The Dollar (#GotBitcoin?)
Bank Of England Governor: Libra-Like Currency Could Replace US Dollar (#GotBitcoin?)
Binance Reveals ‘Venus’ — Its Own Project To Rival Facebook’s Libra (#GotBitcoin?)
The Real Benefits Of Blockchain Are Here. They’re Being Ignored (#GotBitcoin?)
CommBank Develops Blockchain Market To Boost Biodiversity (#GotBitcoin?)
SEC Approves Blockchain Tech Startup Securitize To Record Stock Transfers (#GotBitcoin?)
SegWit Creator Introduces New Language For Bitcoin Smart Contracts (#GotBitcoin?)
You Can Now Earn Bitcoin Rewards For Postmates Purchases (#GotBitcoin?)
Bitcoin Price ‘Will Struggle’ In Big Financial Crisis, Says Investor (#GotBitcoin?)
Fidelity Charitable Received Over $100M In Crypto Donations Since 2015 (#GotBitcoin?)
Would Blockchain Better Protect User Data Than FaceApp? Experts Answer (#GotBitcoin?)
Just The Existence Of Bitcoin Impacts Monetary Policy (#GotBitcoin?)
What Are The Biggest Alleged Crypto Heists And How Much Was Stolen? (#GotBitcoin?)
IRS To Cryptocurrency Owners: Come Clean, Or Else!
Coinbase Accidentally Saves Unencrypted Passwords Of 3,420 Customers (#GotBitcoin?)
Bitcoin Is A ‘Chaos Hedge, Or Schmuck Insurance‘ (#GotBitcoin?)
Bakkt Announces September 23 Launch Of Futures And Custody
Coinbase CEO: Institutions Depositing $200-400M Into Crypto Per Week (#GotBitcoin?)
Researchers Find Monero Mining Malware That Hides From Task Manager (#GotBitcoin?)
Crypto Dusting Attack Affects Nearly 300,000 Addresses (#GotBitcoin?)
A Case For Bitcoin As Recession Hedge In A Diversified Investment Portfolio (#GotBitcoin?)
SEC Guidance Gives Ammo To Lawsuit Claiming XRP Is Unregistered Security (#GotBitcoin?)
15 Countries To Develop Crypto Transaction Tracking System: Report (#GotBitcoin?)
US Department Of Commerce Offering 6-Figure Salary To Crypto Expert (#GotBitcoin?)
Mastercard Is Building A Team To Develop Crypto, Wallet Projects (#GotBitcoin?)
Canadian Bitcoin Educator Scams The Scammer And Donates Proceeds (#GotBitcoin?)
Amazon Wants To Build A Blockchain For Ads, New Job Listing Shows (#GotBitcoin?)
Shield Bitcoin Wallets From Theft Via Time Delay (#GotBitcoin?)
Blockstream Launches Bitcoin Mining Farm With Fidelity As Early Customer (#GotBitcoin?)
Commerzbank Tests Blockchain Machine To Machine Payments With Daimler (#GotBitcoin?)
Man Takes Bitcoin Miner Seller To Tribunal Over Electricity Bill And Wins (#GotBitcoin?)
Bitcoin’s Computing Power Sets Record As Over 100K New Miners Go Online (#GotBitcoin?)
Walmart Coin And Libra Perform Major Public Relations For Bitcoin (#GotBitcoin?)
Judge Says Buying Bitcoin Via Credit Card Not Necessarily A Cash Advance (#GotBitcoin?)
Poll: If You’re A Stockowner Or Crypto-Currency Holder. What Will You Do When The Recession Comes?
1 In 5 Crypto Holders Are Women, New Report Reveals (#GotBitcoin?)
Beating Bakkt, Ledgerx Is First To Launch ‘Physical’ Bitcoin Futures In Us (#GotBitcoin?)
Facebook Warns Investors That Libra Stablecoin May Never Launch (#GotBitcoin?)
Government Money Printing Is ‘Rocket Fuel’ For Bitcoin (#GotBitcoin?)
Bitcoin-Friendly Square Cash App Stock Price Up 56% In 2019 (#GotBitcoin?)
Safeway Shoppers Can Now Get Bitcoin Back As Change At 894 US Stores (#GotBitcoin?)
TD Ameritrade CEO: There’s ‘Heightened Interest Again’ With Bitcoin (#GotBitcoin?)
Venezuela Sets New Bitcoin Volume Record Thanks To 10,000,000% Inflation (#GotBitcoin?)
Newegg Adds Bitcoin Payment Option To 73 More Countries (#GotBitcoin?)
China’s Schizophrenic Relationship With Bitcoin (#GotBitcoin?)
More Companies Build Products Around Crypto Hardware Wallets (#GotBitcoin?)
Bakkt Is Scheduled To Start Testing Its Bitcoin Futures Contracts Today (#GotBitcoin?)
Bitcoin Network Now 8 Times More Powerful Than It Was At $20K Price (#GotBitcoin?)
Crypto Exchange BitMEX Under Investigation By CFTC: Bloomberg (#GotBitcoin?)
“Bitcoin An ‘Unstoppable Force,” Says US Congressman At Crypto Hearing (#GotBitcoin?)
Bitcoin Network Is Moving $3 Billion Daily, Up 210% Since April (#GotBitcoin?)
Cryptocurrency Startups Get Partial Green Light From Washington
Fundstrat’s Tom Lee: Bitcoin Pullback Is Healthy, Fewer Searches Аre Good (#GotBitcoin?)
Bitcoin Lightning Nodes Are Snatching Funds From Bad Actors (#GotBitcoin?)
The Provident Bank Now Offers Deposit Services For Crypto-Related Entities (#GotBitcoin?)
Bitcoin Could Help Stop News Censorship From Space (#GotBitcoin?)
US Sanctions On Iran Crypto Mining — Inevitable Or Impossible? (#GotBitcoin?)
US Lawmaker Reintroduces ‘Safe Harbor’ Crypto Tax Bill In Congress (#GotBitcoin?)
EU Central Bank Won’t Add Bitcoin To Reserves — Says It’s Not A Currency (#GotBitcoin?)
The Miami Dolphins Now Accept Bitcoin And Litecoin Crypt-Currency Payments (#GotBitcoin?)
Trump Bashes Bitcoin And Alt-Right Is Mad As Hell (#GotBitcoin?)
Goldman Sachs Ramps Up Development Of New Secret Crypto Project (#GotBitcoin?)
Blockchain And AI Bond, Explained (#GotBitcoin?)
Grayscale Bitcoin Trust Outperformed Indexes In First Half Of 2019 (#GotBitcoin?)
XRP Is The Worst Performing Major Crypto Of 2019 (GotBitcoin?)
Bitcoin Back Near $12K As BTC Shorters Lose $44 Million In One Morning (#GotBitcoin?)
As Deutsche Bank Axes 18K Jobs, Bitcoin Offers A ‘Plan ฿”: VanEck Exec (#GotBitcoin?)
Argentina Drives Global LocalBitcoins Volume To Highest Since November (#GotBitcoin?)
‘I Would Buy’ Bitcoin If Growth Continues — Investment Legend Mobius (#GotBitcoin?)
Lawmakers Push For New Bitcoin Rules (#GotBitcoin?)
Facebook’s Libra Is Bad For African Americans (#GotBitcoin?)
Crypto Firm Charity Announces Alliance To Support Feminine Health (#GotBitcoin?)
Canadian Startup Wants To Upgrade Millions Of ATMs To Sell Bitcoin (#GotBitcoin?)
Trump Says US ‘Should Match’ China’s Money Printing Game (#GotBitcoin?)
Casa Launches Lightning Node Mobile App For Bitcoin Newbies (#GotBitcoin?)
Bitcoin Rally Fuels Market In Crypto Derivatives (#GotBitcoin?)
World’s First Zero-Fiat ‘Bitcoin Bond’ Now Available On Bloomberg Terminal (#GotBitcoin?)
Buying Bitcoin Has Been Profitable 98.2% Of The Days Since Creation (#GotBitcoin?)
Another Crypto Exchange Receives License For Crypto Futures
From ‘Ponzi’ To ‘We’re Working On It’ — BIS Chief Reverses Stance On Crypto (#GotBitcoin?)
These Are The Cities Googling ‘Bitcoin’ As Interest Hits 17-Month High (#GotBitcoin?)
Venezuelan Explains How Bitcoin Saves His Family (#GotBitcoin?)
Quantum Computing Vs. Blockchain: Impact On Cryptography
This Fund Is Riding Bitcoin To Top (#GotBitcoin?)
Bitcoin’s Surge Leaves Smaller Digital Currencies In The Dust (#GotBitcoin?)
Bitcoin Exchange Hits $1 Trillion In Trading Volume (#GotBitcoin?)
Bitcoin Breaks $200 Billion Market Cap For The First Time In 17 Months (#GotBitcoin?)
You Can Now Make State Tax Payments In Bitcoin (#GotBitcoin?)
Religious Organizations Make Ideal Places To Mine Bitcoin (#GotBitcoin?)
Goldman Sacs And JP Morgan Chase Finally Concede To Crypto-Currencies (#GotBitcoin?)
Bitcoin Heading For Fifth Month Of Gains Despite Price Correction (#GotBitcoin?)
Breez Reveals Lightning-Powered Bitcoin Payments App For IPhone (#GotBitcoin?)
Big Four Auditing Firm PwC Releases Cryptocurrency Auditing Software (#GotBitcoin?)
Amazon-Owned Twitch Quietly Brings Back Bitcoin Payments (#GotBitcoin?)
JPMorgan Will Pilot ‘JPM Coin’ Stablecoin By End Of 2019: Report (#GotBitcoin?)
Is There A Big Short In Bitcoin? (#GotBitcoin?)
Coinbase Hit With Outage As Bitcoin Price Drops $1.8K In 15 Minutes
Samourai Wallet Releases Privacy-Enhancing CoinJoin Feature (#GotBitcoin?)
There Are Now More Than 5,000 Bitcoin ATMs Around The World (#GotBitcoin?)
You Can Now Get Bitcoin Rewards When Booking At Hotels.Com (#GotBitcoin?)
North America’s Largest Solar Bitcoin Mining Farm Coming To California (#GotBitcoin?)
Bitcoin On Track For Best Second Quarter Price Gain On Record (#GotBitcoin?)
Bitcoin Hash Rate Climbs To New Record High Boosting Network Security (#GotBitcoin?)
Bitcoin Exceeds 1Million Active Addresses While Coinbase Custodies $1.3B In Assets
Why Bitcoin’s Price Suddenly Surged Back $5K (#GotBitcoin?)
Zebpay Becomes First Exchange To Add Lightning Payments For All Users (#GotBitcoin?)
Coinbase’s New Customer Incentive: Interest Payments, With A Crypto Twist (#GotBitcoin?)
The Best Bitcoin Debit (Cashback) Cards Of 2019 (#GotBitcoin?)
Real Estate Brokerages Now Accepting Bitcoin (#GotBitcoin?)
Ernst & Young Introduces Tax Tool For Reporting Cryptocurrencies (#GotBitcoin?)
Recession Is Looming, or Not. Here’s How To Know (#GotBitcoin?)
How Will Bitcoin Behave During A Recession? (#GotBitcoin?)
Many U.S. Financial Officers Think a Recession Will Hit Next Year (#GotBitcoin?)
Definite Signs of An Imminent Recession (#GotBitcoin?)
What A Recession Could Mean for Women’s Unemployment (#GotBitcoin?)
Investors Run Out of Options As Bitcoin, Stocks, Bonds, Oil Cave To Recession Fears (#GotBitcoin?)
Goldman Is Looking To Reduce “Marcus” Lending Goal On Credit (Recession) Caution (#GotBitcoin?)

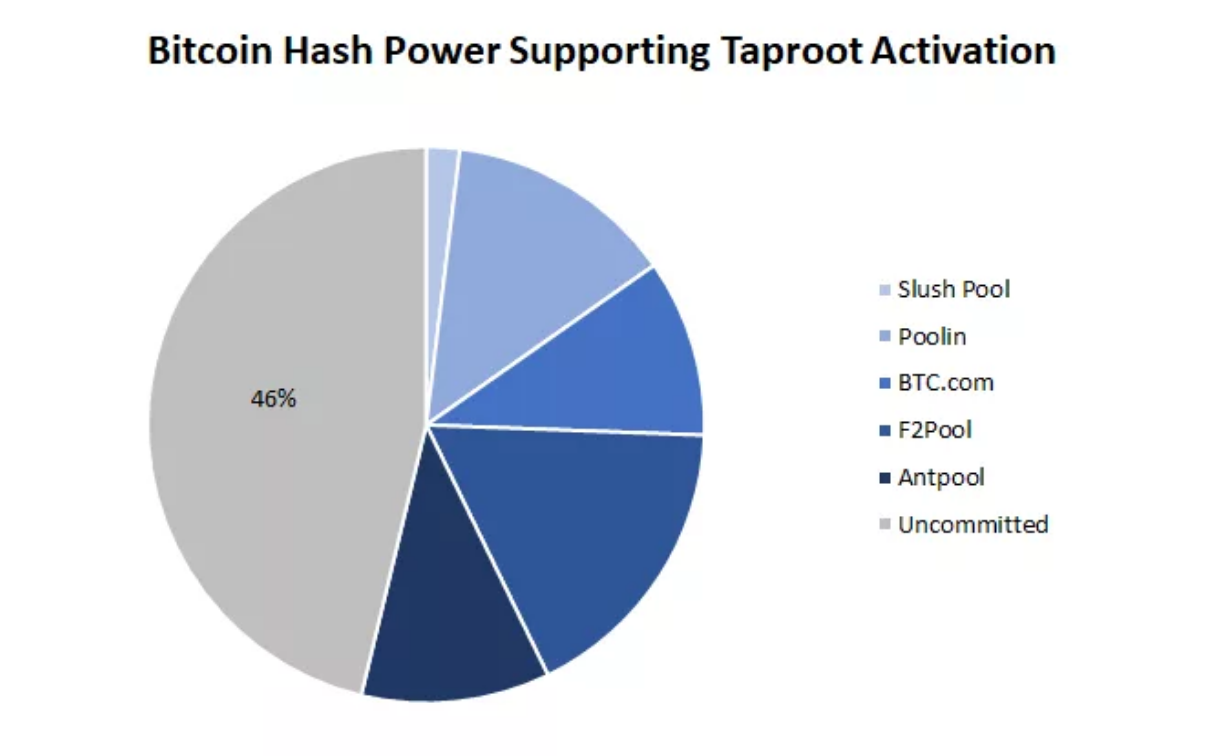
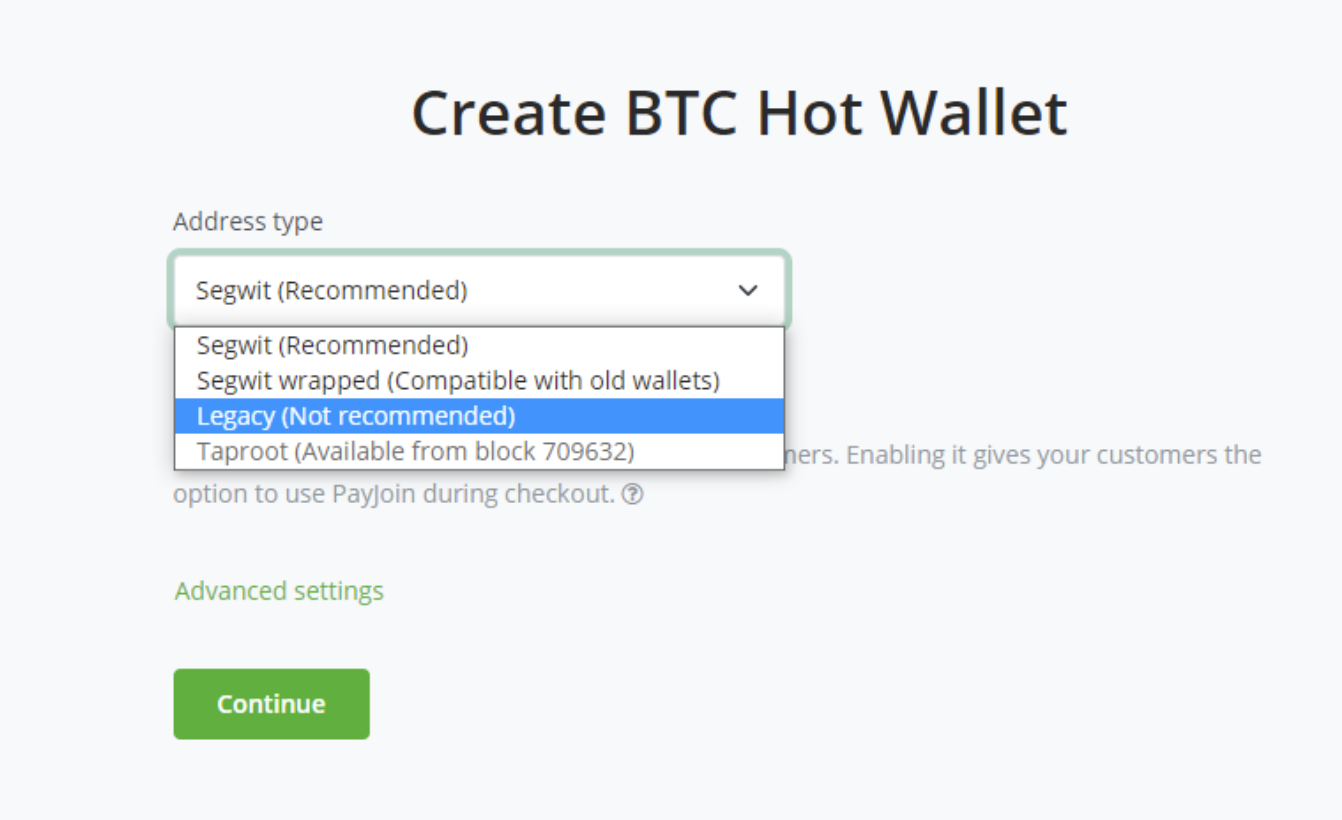
Leave a Reply
You must be logged in to post a comment.